Hi,
I am getting kind of frustrated with the way that the SCL's and quarantine works/does not work in EOP.
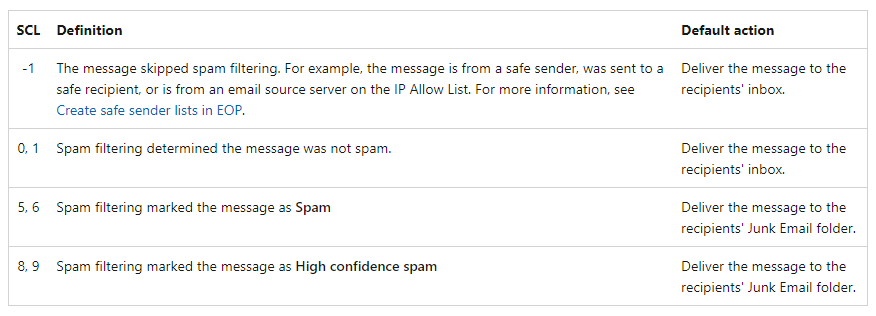
We have a hybrid setup, one on-prem exchange server with all of our mailboxes in O365. We have the E5 security license and in the last couple of days the amount of spams which are landing in our Quarantine (Q) has exploded. To try to contain this madness I have setup a transport rule in EXO that every e-mail that gets marked with SCL 9 ends up being deleted - so far so good? Well most of our spam e-mails are getting flagged with SCL 5! And also all of our good e-mails which also sometimes land in Q are also getting a SCL 5!
I will point out that we are disappointed and angry because those spams with SCL 5 contain the usual viagra, p. growth stuff and should be blocked by Microsoft servers 30 years ago, but hey, here we are in 2022 and still battling this issue. Maybe I don't know how to configure it correctly but I am not the one giving the SCL scores - Microsoft is.
All of our spams are getting delivered to the Q, not the junk folder of the users - it is really to dangerous for us. We have a setup that is based on the MS EOP best practices:
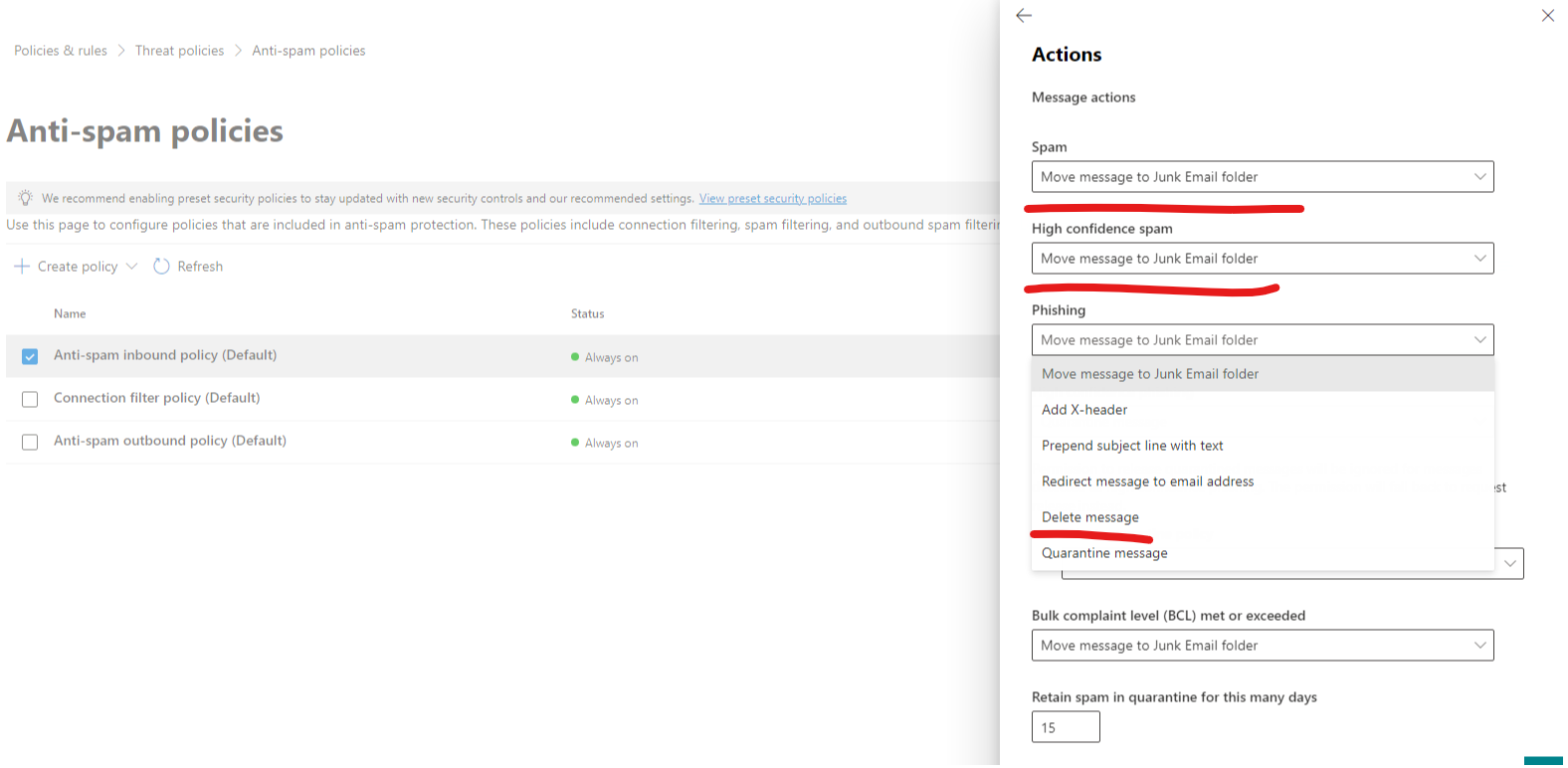
Settings for Anti-spam inbound policy (Default):
Bulk email spam action - On
Bulk email threshold - 5
URL to .biz or .info websites - Off
Image links to remote sites - Off
Numeric IP address in URL - Off
URL redirect to other port - Off
Empty messages - Off
JavaScript or VBScript in HTML - Off
Object tags in HTML - Off
Frame or iframe tags in HTML - Off
Embedded tags in HTML - Off
Form tags in HTML - Off
Web bugs in HTML - Off
Sensitive words - Off
SPF record: hard fail - Off
Conditional Sender ID filtering: hard fail - Off
Backscatter - Off
Test mode action - None
Bulk email spam action - On
International spam - languages - Off
International spam - regions - Off
Edit spam threshold and properties
Actions
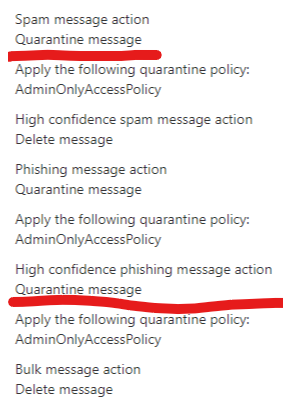
Spam message action
Quarantine message
Apply the following quarantine policy:
AdminOnlyAccessPolicy
High confidence spam message action
Delete message
Phishing message action
Quarantine message
Apply the following quarantine policy:
AdminOnlyAccessPolicy
High confidence phishing message action
Quarantine message
Apply the following quarantine policy:
AdminOnlyAccessPolicy
Bulk message action
Delete message
Enable spam safety tips
On
Enable for spam messages
On
Enable for phishing messages
On
Retain spam in quarantine for this many days
30
Edit actions
Allowed and blocked senders and domains
Allowed senders
-
Allowed domains
-
Blocked senders
37 senders
Blocked domains
27 domains
Also, the high-confidence phish e-mails are giving us a headache because they cannot be deleted automatically. Is there a way to DELETE a high-confidence phising e-mail?
There are examples of the headers for spam e-mails:
spf=none (sender IP is 212.192.218.207) smtp.mailfrom=friend.airfun.shop; dkim=none (message not signed) header.d=none;dmarc=none action=none header.from=friend.airfun.shop;compauth=pass reason=105
spf=pass (sender IP is 212.192.218.219) smtp.mailfrom=bury.worddeep.shop; dkim=none (message not signed) header.d=none;dmarc=bestguesspass action=none header.from=bury.worddeep.shop;compauth=pass reason=109
spf=pass (sender IP is 198.98.54.213) smtp.mailfrom=concretoslima.com; dkim=pass (signature was verified) header.d=concretoslima.com;dmarc=pass action=none header.from=concretoslima.com;compauth=pass reason=100
spf=pass (sender IP is 188.172.250.139) smtp.mailfrom=infos.tempus.de; dkim=pass (signature was verified) header.d=tempus.de;dmarc=bestguesspass action=none header.from=tempus.de;compauth=pass reason=109
spf=none (sender IP is 204.156.177.49) smtp.mailfrom=mailer1.acisummits.com; dkim=pass (signature was verified) header.d=acievents.eu;dmarc=bestguesspass action=none header.from=acievents.eu;compauth=pass reason=109
Cheers