I'm confused by your statement "ConfigMgr doesn't manage certificates"
This statement is accurate in the context of your question because self-signed certificates are automatically trusted and there's no such thing as a root CA or certificate for a root CA when using self-signed certs (in ConfigMgr or anywhere else). So that begs the question here: are you using PKI-issued client auth certs for ConfigMgr or not?
Is there some sort of white paper that has better documentation on MECM and PKI certificate integration in an environment that has Internet-only clients that may occasionally connect to VPN?
No, the two aren't specifically related topics.
A handful of facts here may help as I think you are conflating multiple, disparate things here:
- The ConfigMgr client always uses a client auth certificate to communicate with the site. This cert can be self-signed or issued from a separate PKI.
- The underlying path (i.e., VPN, intranet, Internet) for client communication is irrelevant for cert choice, i.e., the client won't choose to use a different type of cert based on the data path. The client always chooses the most secure certificate type available to it (which is a PKI cert if it's available and trusted).
- Self-signed certs are also self-generated and automatically trusted since they are self-generated. There's no hierarchy, PKI, or root CA involved.
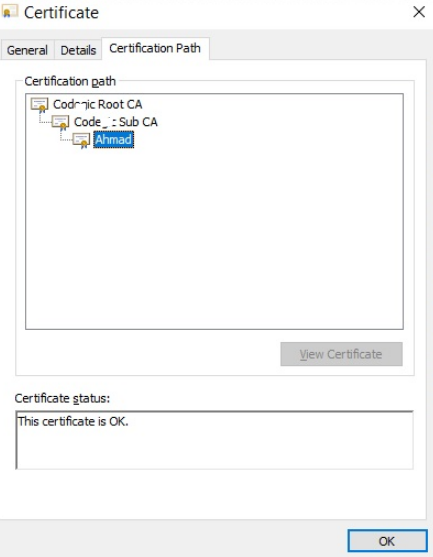
- Trust for PKI-issued certificates is established (in Windows) by adding CAs in the PKI hierarchy to the trusted root CA and intermediate CA stores. With an Enterprise (aka AD integrated) PKI this is done automatically for you on domain-joined devices. When your PKI is not AD integrated, the device is not AD joined, or there is no connectivity, then making the PKI trusted is a challenge without an automatic solution in most cases although you can use SCEP if the systems are managed by Intune to issue a cert and establish trust.
- PKI certificate trust is an OS function and not a ConfigMgr function.,
- All certificates "used" by a system must be trusted. For a ConfigMgr client, that means the local client auth cert as well as the server auth cert for any of the site roles it communicates with must all be trusted.