Hi @Nagashree Balasundaram Thanks for reaching out. You must use LastError property to achieve this please refer this document for more information https://learn.microsoft.com/en-us/azure/api-management/api-management-error-handling-policies#lasterror
please refer the below policy,
<policies>
<inbound>
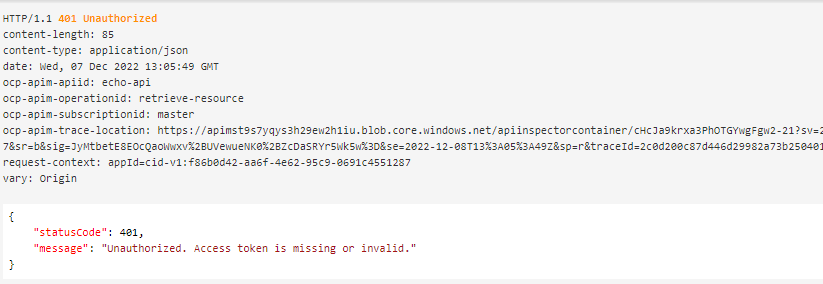
<validate-jwt header-name="Authorization" failed-validation-httpcode="401" failed-validation-error-message="Unauthorized. Access token is missing or invalid.">
<openid-config url="https://login.microsoftonline.com/common/v2.0/.well-known/openid-configuration" />
<required-claims>
<claim name="aud">
<value>524d5efb-664f-4aa2-9e14-xxxxxxxxx</value>
</claim>
</required-claims>
</validate-jwt>
</inbound>
<backend>
</backend>
<outbound
</outbound>
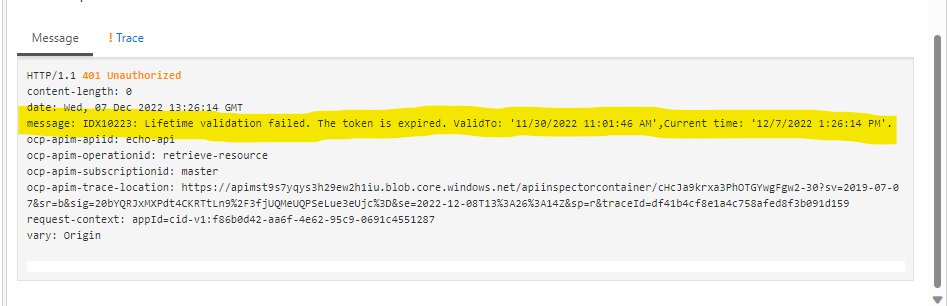
<on-error>
<return-response>
<set-status code="401" reason="Unauthorized" />
<set-header name="message" exists-action="override">
<value>@(context.LastError.Message)</value>
</set-header>
</return-response>
</on-error>
</policies>
do let me know incase of further queries, I would be happy to assist you.
Please 'Accept as answer' and ‘Upvote’ if it helped so that it can help others in the community looking for help on similar topics.