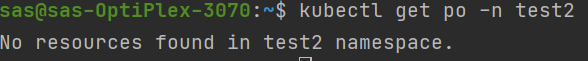
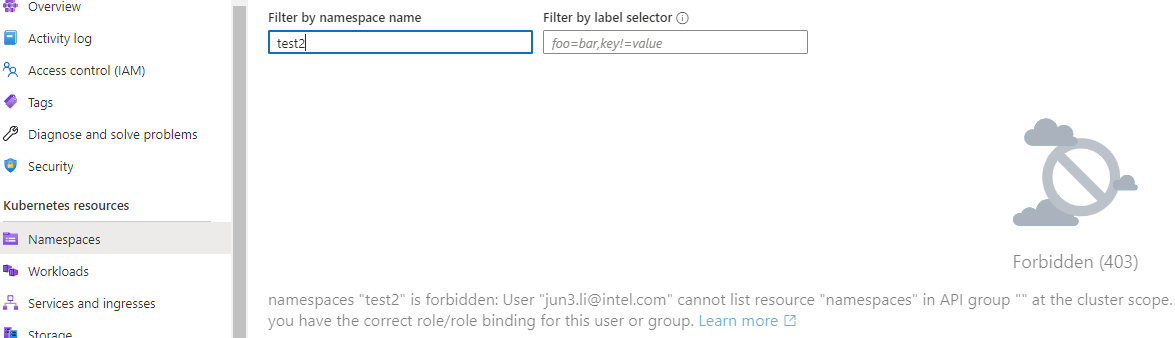
Hello @Li Jun - Hanson ,
Thanks for your query !
Can you try out the below steps:
1) Connect to the cluster using –admin flag
az aks get-credentials -g rgname -n aksclustername --admin
2) Get the user name UPN for which you want to provide the access using the below command
az ad signed-in-user show --query userPrincipalName -o tsv
3) Using the below document
- https://learn.microsoft.com/en-us/azure/aks/azure-ad-integration-cli#create-kubernetes-rbac-binding Create YAML file of Kind: ClusterRoleBinding
Sample clusterrole.yaml YAML FILE:
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: cluster-admin
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:- apiGroup: rbac.authorization.k8s.io
kind: User
name: UPN of the user from above command
4) kubectl apply -f C:\clusterrole.yml
- apiGroup: rbac.authorization.k8s.io
Hope above steps helps out in resolving the issue , kindly make sure to "Upvote and Accept the answer"