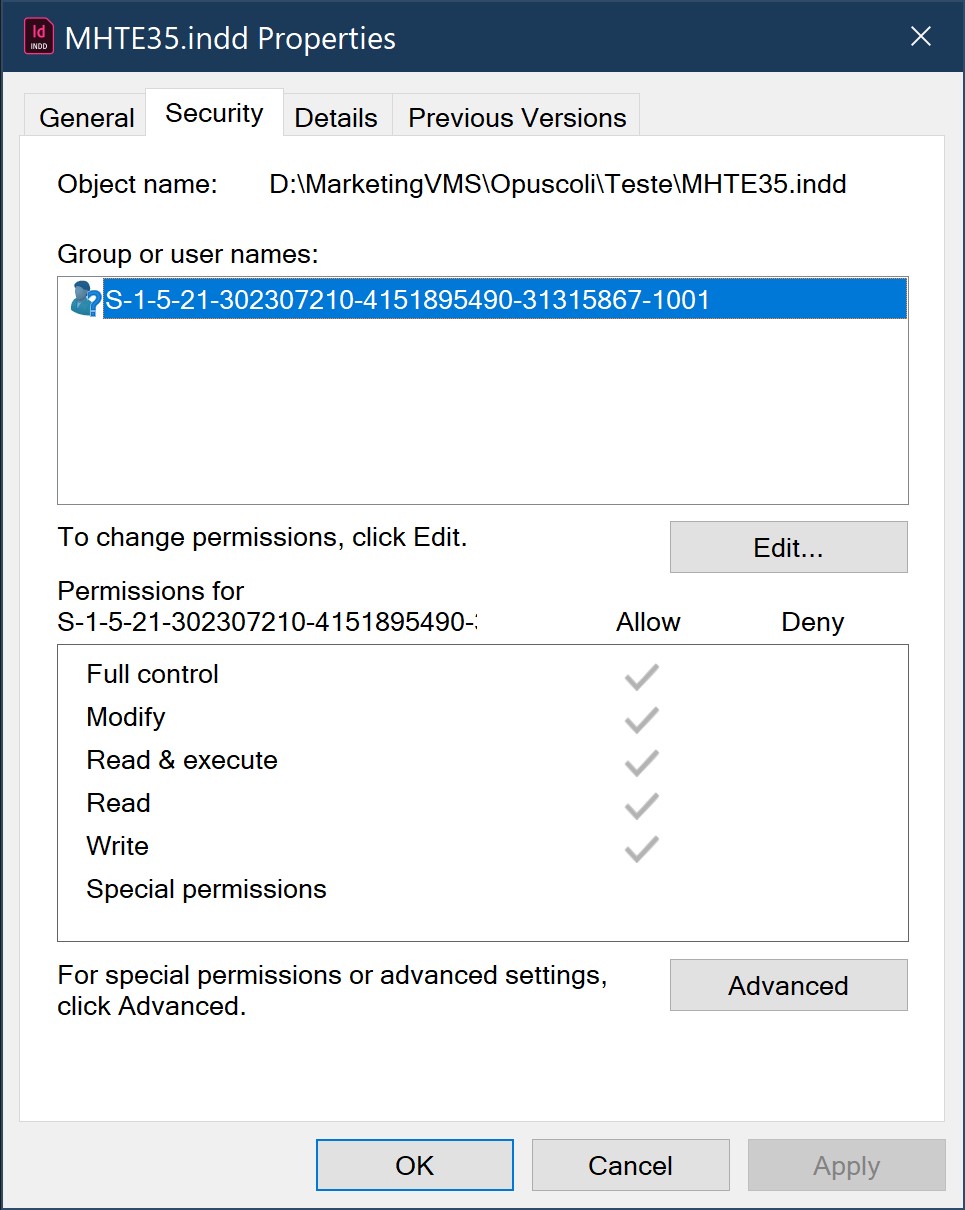
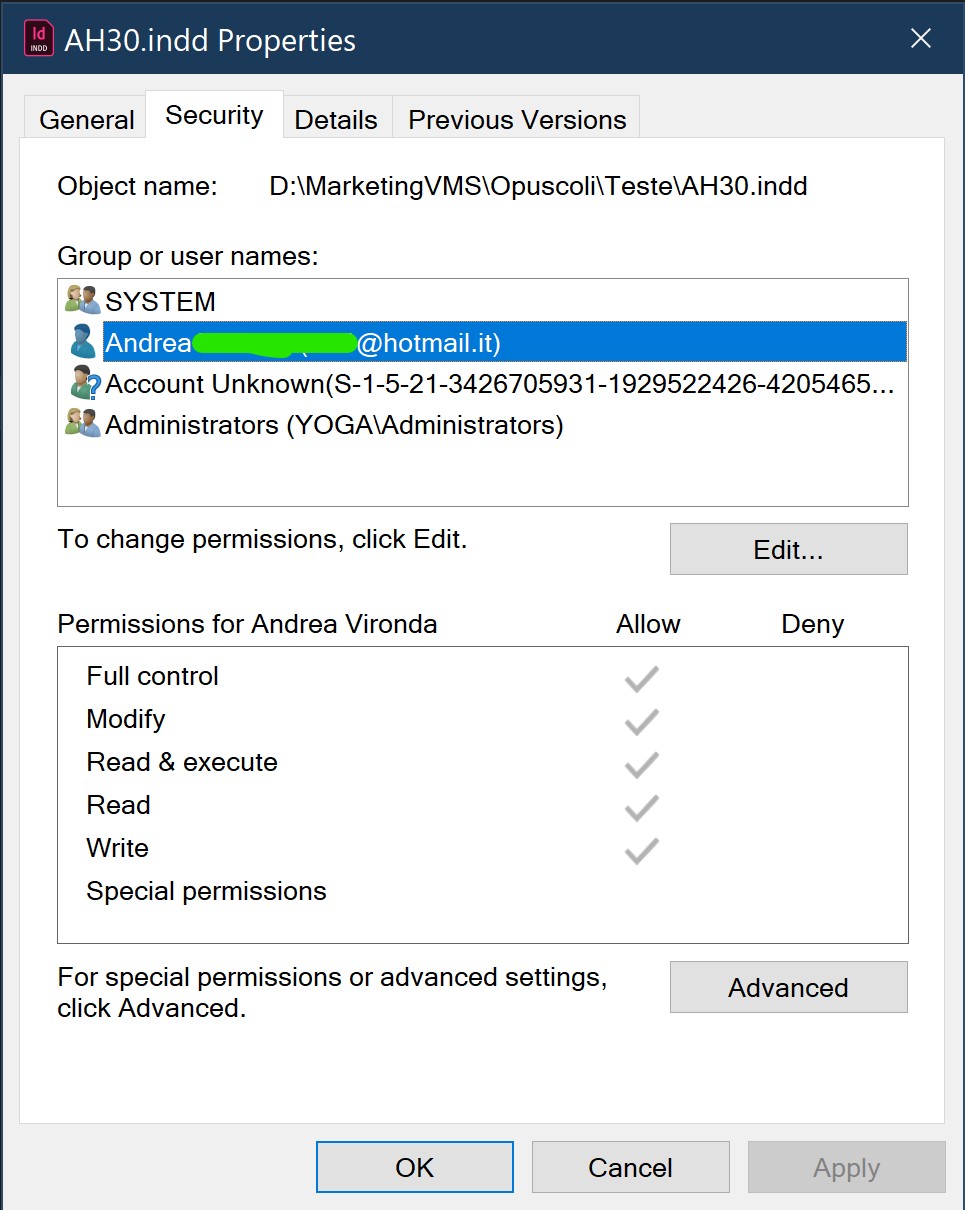
In the images that you posted, look at the difference in security permissions. MHTE53.indd only has one account that is allowed access. For AH30.indd in addition to your account and the unknown SID, you have what I would consider to be "normal" inherited permissions for SYSTEM and Administrators. Note the color of the check marks. A gray color is an inherited permissions. A black check is a ACL that is only on that file/folder.
The account that has access to MHTE53.indd either got deleted from the PC that you took the screen image on, or is another local account on anther PC. The crypto malware may have also altered NTFS permissions and removed the inherited permissions.
Permissions can easily be reset. Set the permissions that you want on the folder D:\MarketingVMS\Opuscoli\Teste. Save these commands below as a bat file, then open an admin command prompt and run the .bat file. You should then be able to access all files.
set badfolder="D:\MarketingVMS\Opuscoli\Teste"
takeown /d Y /a /r /f %badfolder%
icacls %badfolder% /reset /t
icacls %badfolder% /verify /t
You should also check the permissions on the WS2019 server.