Note that you don't have to change the sign-in method either. You can stay federated for everyone for now. And you can configure Azure MFA as a MFA provider in ADFS and use custom rules to assign MFA method based on group membership (requires ADFS on Windows Server 2019).
Using both ADFS authentication and standard Micosoft MFA on O365
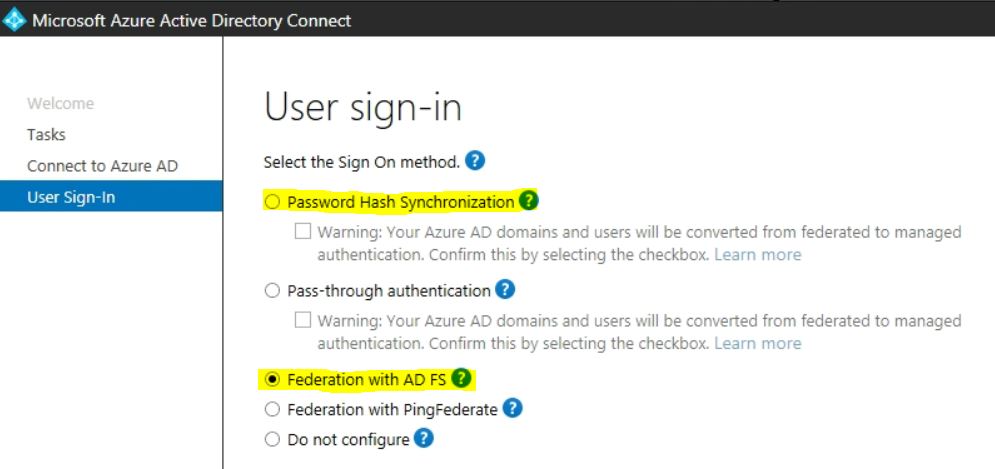
We are using an on premise ADFS server with RSA integration for authenticating on O365. We used the Azure Active directory connector to configure this with the ‘Federation with AD FS’ option.
Part of our RSA tokens and licensing will expire the next few month. We would like to gradually migrate to just Microsoft MFA authentication and configure this per user or group.
I can’t seem to configure authentication to O365 to both ADFS and standard O365 authentication. At least not with the Azure Active directory connector. Does anyone have any idea how we can fix this?
-
 Pierre Audonnet - MSFT 10,166 Reputation points Microsoft Employee
Pierre Audonnet - MSFT 10,166 Reputation points Microsoft Employee2021-04-04T14:04:22.68+00:00
2 additional answers
Sort by: Most helpful
-
 Andy David - MVP 141K Reputation points MVP
Andy David - MVP 141K Reputation points MVP2021-04-04T12:20:15.337+00:00 I would look at the staged rollout rather than changing the Sign in at this point:
https://learn.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-staged-rollout#:~:text=Staged%20rollout%20allows%20you%20to,before%20cutting%20over%20your%20domains. -
Wouter 26 Reputation points
2021-04-04T15:04:31.393+00:00 @Andy David - MVP @Pierre Audonnet - MSFT : This should work. Especially using the current ADSF server with Azure MFA will help me to phase out RSA token authentication short term. I will have to upgrade my ADFS server 2012 R2 to server 2019 but that's no problem. I will work on this the next few weeks.
thank you very much.!