Overview of Microsoft Defender for Storage
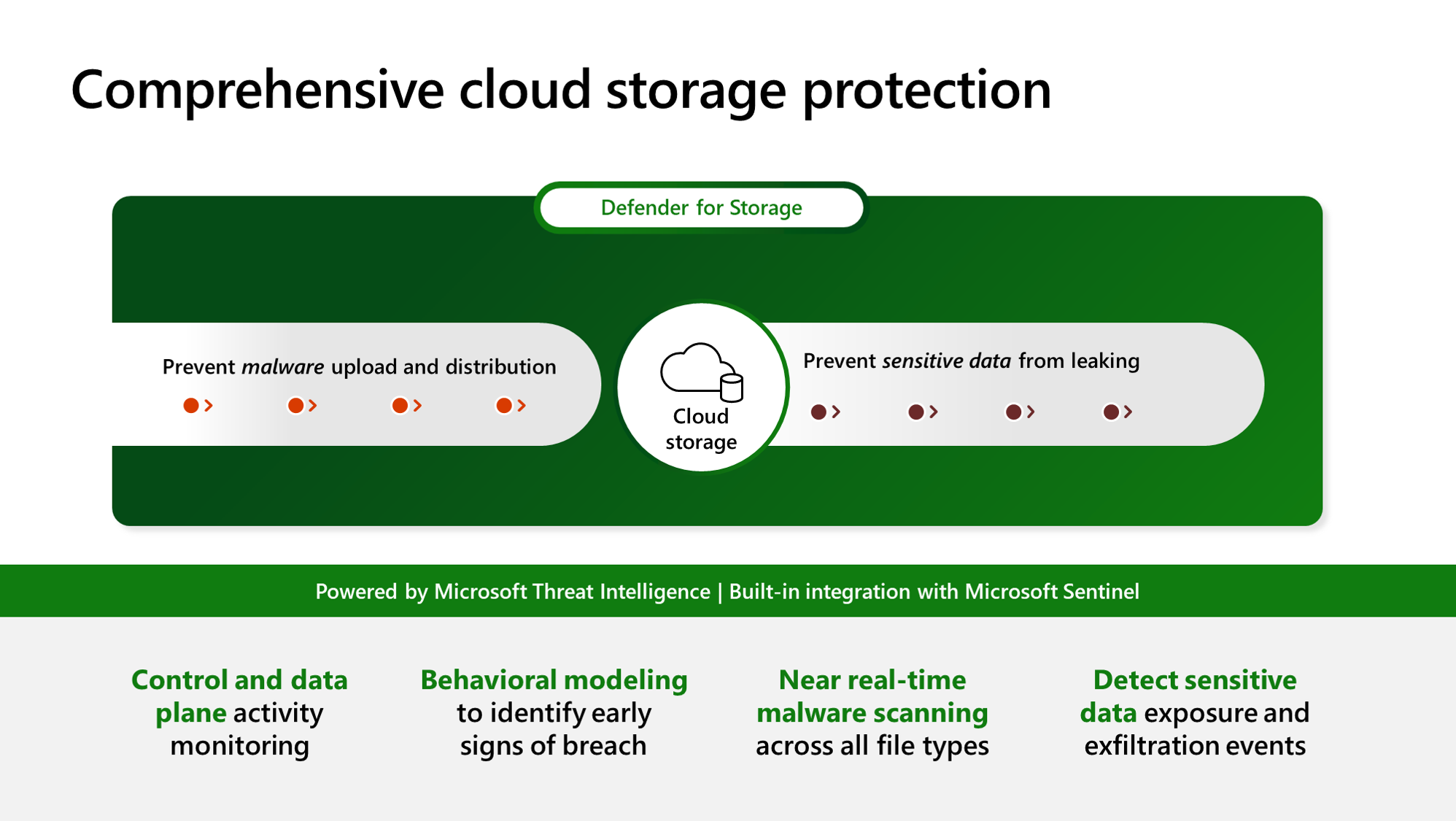
Microsoft Defender for Storage is an Azure-native layer of security intelligence that detects potential threats to your storage accounts.
It helps prevent the three major impacts on your data and workload: malicious file uploads, sensitive data exfiltration, and data corruption.
Note
This article is about the new Defender for Storage plan that was launched on March 28, 2023. It includes new features like Malware Scanning and Sensitive Data Threat Detection. This plan also provides a more predictable pricing structure for better control over coverage and costs. Additionally, all new Defender features will only be added to the new plan. Migrating to the new plan is a simple process, read here about how to migrate from the classic plan.
Microsoft Defender for Storage provides comprehensive security by analyzing the data plane and control plane telemetry generated by Azure Blob Storage, Azure Files, and Azure Data Lake Storage services. It uses advanced threat detection capabilities powered by Microsoft Threat Intelligence, Microsoft Defender Antivirus, and Sensitive Data Discovery to help you discover and mitigate potential threats.
Defender for Storage includes:
- Activity Monitoring
- Sensitive data threat detection (preview feature, new plan only)
- Malware Scanning (new plan only)
Getting started
With a simple agentless setup at scale, you can enable Defender for Storage at the subscription or resource levels through the portal or programmatically. When enabled at the subscription level, all existing and newly created storage accounts under that subscription will be automatically protected. You can also exclude specific storage accounts from protected subscriptions.
Note
If you already have the Defender for Storage (classic) enabled and want to access the new security features and pricing, you'll need to migrate to the new pricing plan.
Availability
| Aspect | Details |
|---|---|
| Release state: | General Availability (GA) |
| Feature availability: | - Activity monitoring (security alerts) – General Availability (GA) - Malware Scanning – General Availability (GA) - Sensitive data threat detection (Sensitive Data Discovery) – Preview |
| Pricing: | Microsoft Defender for Storage pricing applies to commercial clouds. Learn more about pricing and availability per region. |
Supported storage types: |
Blob Storage (Standard/Premium StorageV2, including Data Lake Gen2): Activity monitoring, Malware Scanning, Sensitive Data Discovery Azure Files (over REST API and SMB): Activity monitoring |
| Required roles and permissions: | For Malware Scanning and sensitive data threat detection at subscription and storage account levels, you need Owner roles (subscription owner/storage account owner) or specific roles with corresponding data actions. To enable Activity Monitoring, you need 'Security Admin' permissions. Read more about the required permissions. |
| Clouds: |
* Azure DNS Zone isn't supported for Malware Scanning and sensitive data threat detection.
What are the benefits of Microsoft Defender for Storage?
Defender for Storage provides the following:
Better protection against malware: The Malware Scanning scans and detects in near real-time all file types, including archives of every uploaded blob, and provides fast and reliable results, helping you prevent your storage accounts from acting as an entry and distribution point for threats. Learn more about Malware Scanning.
Improved threat detection and protection of sensitive data: The sensitive data threat detection capability enables security professionals to efficiently prioritize and examine security alerts by considering the sensitivity of the data that could be at risk, leading to better detection and protection against potential threats. By quickly identifying and addressing the most significant risks, this capability lowers the likelihood of data breaches and enhances sensitive data protection by detecting exposure events and suspicious activities on resources containing sensitive data. Learn more about sensitive data threat detection.
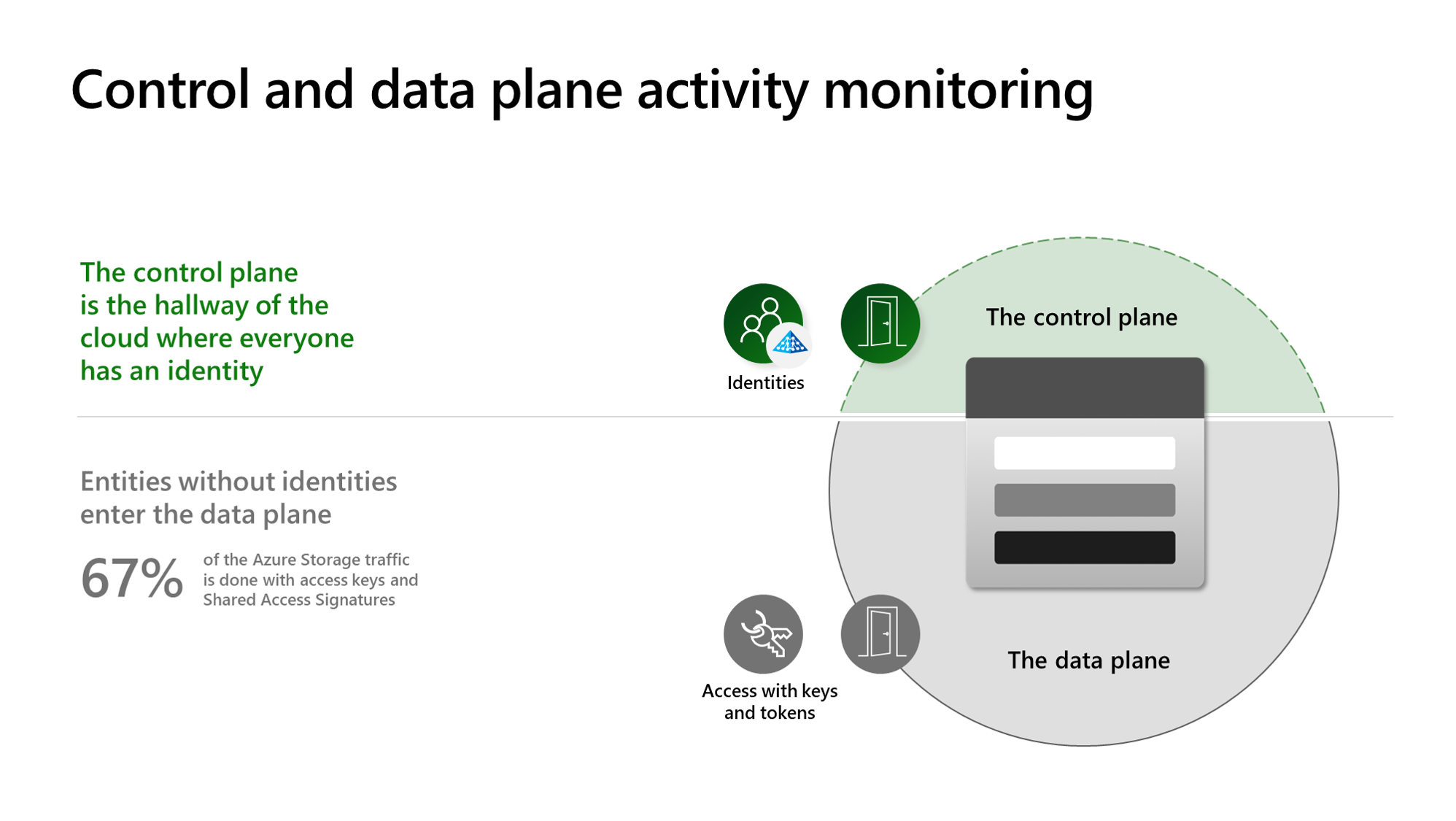
Detection of entities without identities: Defender for Storage detects suspicious activities generated by entities without identities that access your data using misconfigured and overly permissive Shared Access Signatures (SAS tokens) that might have leaked or compromised so that you can improve the security hygiene and reduce the risk of unauthorized access. This capability is an expansion of the Activity Monitoring security alerts suite.
Coverage of the top cloud storage threats: Powered by Microsoft Threat Intelligence, behavioral models, and machine learning models to detect unusual and suspicious activities. The Defender for Storage security alerts covers the top cloud storage threats, such as sensitive data exfiltration, data corruption, and malicious file uploads.
Comprehensive security without enabling logs: When Microsoft Defender for Storage is enabled, it continuously analyzes both the data plane and control plane telemetry stream generated by Azure Blob Storage, Azure Files, and Azure Data Lake Storage services without the requirement of enabling diagnostic logs.
Frictionless enablement at scale: Microsoft Defender for Storage is an agentless solution, easy to deploy, and enables security protection at scale using a native Azure solution.
How does the service work?
Activity monitoring
Defender for Storage continuously analyzes data and control plane logs from protected storage accounts when enabled. There's no need to turn on resource logs for security benefits. Use Microsoft Threat Intelligence to identify suspicious signatures such as malicious IP addresses, Tor exit nodes, and potentially dangerous apps. It also builds data models and uses statistical and machine-learning methods to spot baseline activity anomalies, which might indicate malicious behavior. You receive security alerts for suspicious activities, but Defender for Storage ensures you won't get too many similar alerts. Activity monitoring won't affect performance, ingestion capacity, or access to your data.
Malware Scanning (powered by Microsoft Defender Antivirus)
Note
Billing for Malware Scanning begins on September 3, 2023. To limit expenses, use the Monthly capping feature to set a cap on the amount of GB scanned per month, per storage account to help you control your costs.
Malware Scanning in Defender for Storage helps protect storage accounts from malicious content by performing a full malware scan on uploaded content in near real time, applying Microsoft Defender Antivirus capabilities. It's designed to help fulfill security and compliance requirements to handle untrusted content. Every file type is scanned, and scan results are returned for every file. The Malware Scanning capability is an agentless SaaS solution that allows simple setup at scale, with zero maintenance, and supports automating response at scale. This is a configurable feature in the new Defender for Storage plan that is priced per GB scanned. Learn more about Malware Scanning.
Sensitive data threat detection (powered by Sensitive Data Discovery)
The ‘sensitive data threat detection’ capability enables security teams to efficiently prioritize and examine security alerts by considering the sensitivity of the data that could be at risk, leading to better detection and preventing data breaches. ‘Sensitive data threat detection’ is powered by the “Sensitive Data Discovery” engine, an agentless engine that uses a smart sampling method to find resources with sensitive data. The service is integrated with Microsoft Purview's sensitive information types (SITs) and classification labels, allowing seamless inheritance of your organization's sensitivity settings.
This is a configurable feature in the new Defender for Storage plan. You can choose to enable or disable it with no other cost. For more details, visit Sensitive data threat detection.
Pricing and cost controls
Per storage account pricing
The new Microsoft Defender for Storage plan has predictable pricing based on the number of storage accounts you protect. With the option to enable at the subscription or resource level and exclude specific storage accounts from protected subscriptions, you have increased flexibility to manage your security coverage. The pricing plan simplifies the cost calculation process, allowing you to scale easily as your needs change. Other charges might apply to storage accounts with high-volume transactions.
Malware Scanning - Billing per GB, monthly capping, and configuration
Malware Scanning is charged on a per-gigabyte basis for scanned data. To ensure cost predictability, a monthly cap can be established for each storage account's scanned data volume, per-month basis. This cap can be set subscription-wide, affecting all storage accounts within the subscription, or applied to individual storage accounts. Under protected subscriptions, you can configure specific storage accounts with different limits.
By default, the limit is set to 5,000 GB per month per storage account. Once this threshold is exceeded, scanning will cease for the remaining blobs, with a 20-GB confidence interval. For configuration details, refer to configure Defender for Storage.
Important
Malware scanning in Defender for Storage is not included for free in the first 30 day trial and will be charged from the first day in accordance with the pricing scheme available on the Defender for Cloud pricing page. Malware scanning will also incur additional charges for other Azure services - Azure Storage read operations, Azure Storage blob indexing and Azure Event Grid notifications.
Enablement at scale with granular controls
Microsoft Defender for Storage enables you to secure your data at scale with granular controls. You can apply consistent security policies across all your storage accounts within a subscription or customize them for specific accounts to suit your business needs. You can also control your costs by choosing the level of protection you need for each resource. To get started, visit enable Defender for Storage.
Monitoring your malware scanning cap
To ensure uninterrupted protection while effectively managing costs, there are two informational security alerts related to malware scanning cap usage. The first alert, Malware Scanning will stop soon: 75% of monthly gigabytes scan cap reached (Preview), is triggered as your usage approaches 75% of the set monthly cap, offering a heads-up to adjust your cap if needed. The second alert, Malware Scanning stopped: monthly gigabytes scan cap reached (Preview), notifies you when the cap has been reached and scanning is paused for the month, potentially leaving new uploads unscanned. Both alerts come with details on affected storage accounts to facilitate prompt and informed action, ensuring you can maintain your desired level of security without unexpected expenses.
Understanding the differences between Malware Scanning and hash reputation analysis
Defender for Storage offers two capabilities to detect malicious content uploaded to storage accounts: Malware Scanning (paid add-on feature available only on the new plan) and hash reputation analysis (available in all plans).
Malware Scanning (paid add-on feature available only on the new plan)
Malware Scanning uses Microsoft Defender Antivirus (MDAV) to scan blobs uploaded to Blob storage, providing a comprehensive analysis that includes deep file scans and hash reputation analysis. This feature provides an enhanced level of detection against potential threats.
Hash reputation analysis (available in all plans)
Hash reputation analysis detects potential malware in Blob storage and Azure Files by comparing the hash values of newly uploaded blobs/files against those of known malware by Microsoft Threat Intelligence. Not all file protocols and operation types are supported with this capability, leading to some operations not being monitored for potential malware uploads. Unsupported use cases include SMB file shares and when a blob is created using Put Block and Put blocklist.
In summary, Malware Scanning, which is only available on the new plan for Blob storage, offers a more comprehensive approach to malware detection by analyzing the full content of files and incorporating hash reputation analysis in its scanning methodology.
Next steps
In this article, you learned about Microsoft Defender for Storage.
- Enable Defender for Storage
- Check out common questions about Defender for Storage.
Обратна връзка
Очаквайте скоро: През цялата 2024 г. постепенно ще отстраняваме проблемите в GitHub като механизъм за обратна връзка за съдържание и ще го заменим с нова система за обратна връзка. За повече информация вижте: https://aka.ms/ContentUserFeedback.
Подаване и преглед на обратна връзка за