Begivenhed
9. apr., 15 - 10. apr., 12
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Tilmeld dig nuDenne browser understøttes ikke længere.
Opgrader til Microsoft Edge for at drage fordel af de nyeste funktioner, sikkerhedsopdateringer og teknisk support.
This article describes the steps you need to perform in both N-able User Provisioning and Microsoft Entra ID to configure automatic user provisioning. When configured, Microsoft Entra ID automatically provisions and deprovisions users to N-able User Provisioning using the Microsoft Entra provisioning service. For important details on what this service does, how it works, and frequently asked questions, see Automate user provisioning and deprovisioning to SaaS applications with Microsoft Entra ID.
Bemærk
To use the OAuth2 flow, users should use the https://portal.azure.com/?feature.userProvisioningV2Authentication=true url to access the Azure portal.
The scenario outlined in this article assumes that you already have the following prerequisites:
Add N-able User Provisioning from the Microsoft Entra application gallery to start managing provisioning to N-able User Provisioning. If you have previously setup N-able User Provisioning for SSO, you can use the same application. However it's recommended that you create a separate app when testing out the integration initially. Learn more about adding an application from the gallery here.
The Microsoft Entra provisioning service allows you to scope who will be provisioned based on assignment to the application and or based on attributes of the user. If you choose to scope who will be provisioned to your app based on assignment, you can use the following steps to assign users to the application. If you choose to scope who will be provisioned based solely on attributes of the user, you can use a scoping filter as described here.
Start small. Test with a small set of users before rolling out to everyone. When scope for provisioning is set to assigned users, you can control this by assigning one or two users to the app. When scope is set to all users, you can specify an attribute based scoping filter.
If you need more roles, you can update the application manifest to add new roles.
This section guides you through the steps to configure the Microsoft Entra provisioning service to create, update, and disable users in N-able User Provisioning based on user assignments in Microsoft Entra ID.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
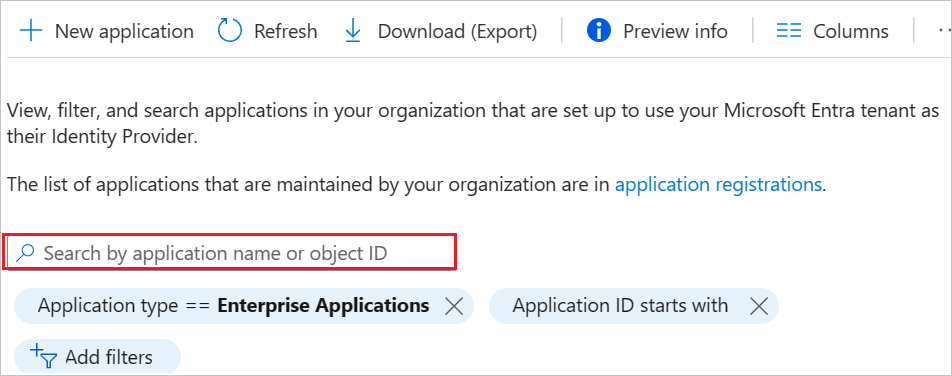
Browse to Identity > Applications > Enterprise applications
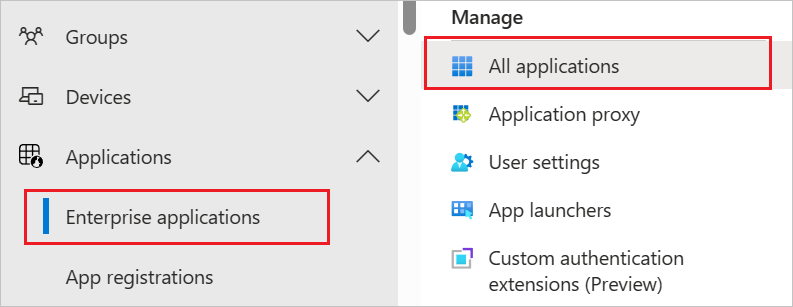
In the applications list, select N-able User Provisioning.
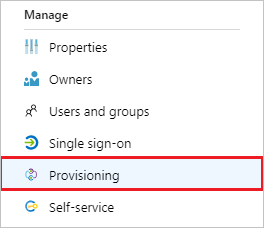
Select the Provisioning tab.
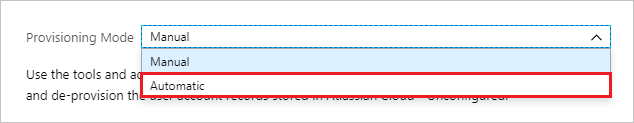
Set the Provisioning Mode to Automatic.
In the Admin Credentials section, enter your N-able User Provisioning Tenant URL, Token Endpoint, Client Identifier and Client Secret. Click Test Connection to ensure Microsoft Entra ID can connect to N-able User Provisioning. If the connection fails, ensure your N-able User Provisioning account has Admin permissions and try again.
Bemærk
To use the OAuth2 flow, users should use the https://portal.azure.com/?feature.userProvisioningV2Authentication=true url to access the Azure portal.

In the Notification Email field, enter the email address of a person who should receive the provisioning error notifications and select the Send an email notification when a failure occurs check box.
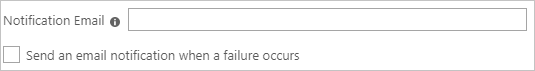
Select Save.
Under the Mappings section, select Synchronize Microsoft Entra users to N-able User Provisioning.
Review the user attributes that are synchronized from Microsoft Entra ID to N-able User Provisioning in the Attribute-Mapping section. The attributes selected as Matching properties are used to match the user accounts in N-able User Provisioning for update operations. If you choose to change the matching target attribute, you need to ensure that the N-able User Provisioning API supports filtering users based on that attribute. Select the Save button to commit any changes.
| Attribute | Type | Supported for filtering | Required by N-able User Provisioning |
|---|---|---|---|
| userName | String | ✓ | ✓ |
| active | Boolean | ✓ | |
| name.givenName | String | ✓ | |
| name.familyName | String | ✓ |
To configure scoping filters, refer to the following instructions provided in the Scoping filter article.
To enable the Microsoft Entra provisioning service for N-able User Provisioning, change the Provisioning Status to On in the Settings section.

Define the users that you would like to provision to N-able User Provisioning by choosing the desired values in Scope in the Settings section.
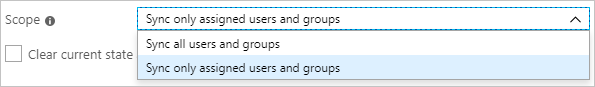
When you're ready to provision, click Save.

This operation starts the initial synchronization cycle of all users defined in Scope in the Settings section. The initial cycle takes longer to perform than subsequent cycles, which occur approximately every 40 minutes as long as the Microsoft Entra provisioning service is running.
Once you've configured provisioning, use the following resources to monitor your deployment:
Begivenhed
9. apr., 15 - 10. apr., 12
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Tilmeld dig nuTræning
Modul
Implement and monitor the integration of enterprise apps for SSO - Training
Deploying and monitoring enterprise applications to Azure solutions can ensure security. Explore how to deploy on-premises and cloud based apps to users.
Certificering
Microsoft Certified: Associate for identitets- og adgangsadministrator - Certifications
Demonstrer funktionerne i Microsoft Entra ID for at modernisere identitetsløsninger, implementere hybridløsninger og implementere identitetsstyring.
Dokumentation
Configure Egnyte for automatic user provisioning with Microsoft Entra ID - Microsoft Entra ID
Learn how to automatically provision and deprovision user accounts from Microsoft Entra ID to Egnyte.
Microsoft Entra single sign-on (SSO) integration with Freshworks - Microsoft Entra ID
Learn how to configure single sign-on between Microsoft Entra ID and Freshworks.
Learn how to automatically provision and deprovision user accounts from Microsoft Entra ID to Insightly SAML.