Events
9 Apr, 3 pm - 10 Apr, 12 pm
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
In this article, you'll learn how to integrate Upshotly with Microsoft Entra ID. When you integrate Upshotly with Microsoft Entra ID, you can:
To get started, you need the following items:
In this article, you configure and test Microsoft Entra SSO in a test environment.
To configure the integration of Upshotly into Microsoft Entra ID, you need to add Upshotly from the gallery to your list of managed SaaS apps.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, as well as walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO with Upshotly using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in Upshotly.
To configure and test Microsoft Entra SSO with Upshotly, perform the following steps:
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Upshotly > Single sign-on.
On the Select a single sign-on method page, select SAML.
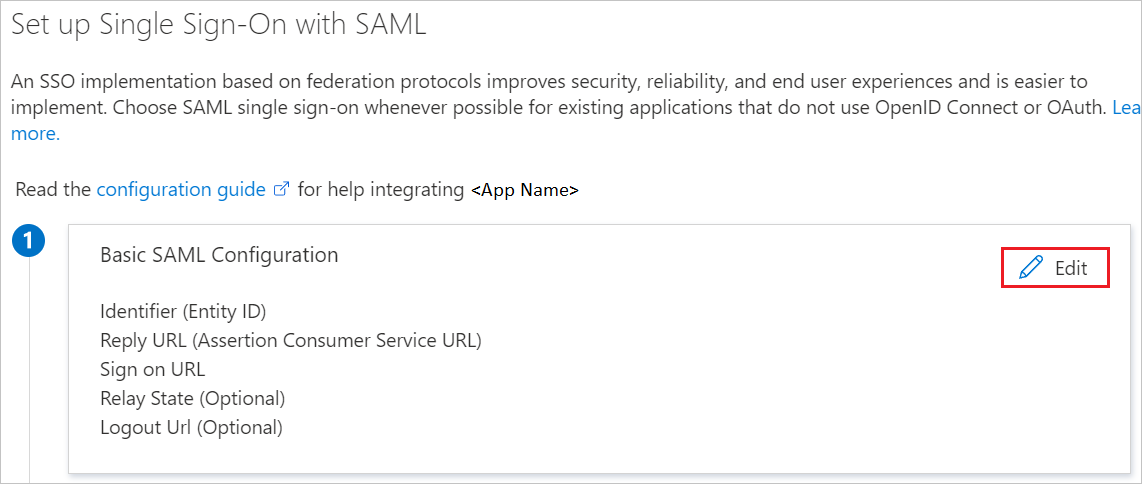
On the Set up single sign-on with SAML page, click the edit/pencil icon for Basic SAML Configuration to edit the settings.
On the Basic SAML Configuration section, if you wish to configure the application in IDP initiated mode, the application is pre-configured and the necessary URLs are already pre-populated with Azure. The user needs to save the configuration by clicking the Save button.
Click Set additional URLs and perform the following step if you wish to configure the application in SP initiated mode:
In the Sign-on URL text box, type a URL using the following pattern:
https://app.upshotly.com/api/sso/login/<companyID>
Note
The Sign-on URL value is not real. Update this values with the actual Sign-on URL. You will get the companyID value explained later in the article. Contact Upshotly Client support team for queries. You can also refer to the patterns shown in the Basic SAML Configuration section.
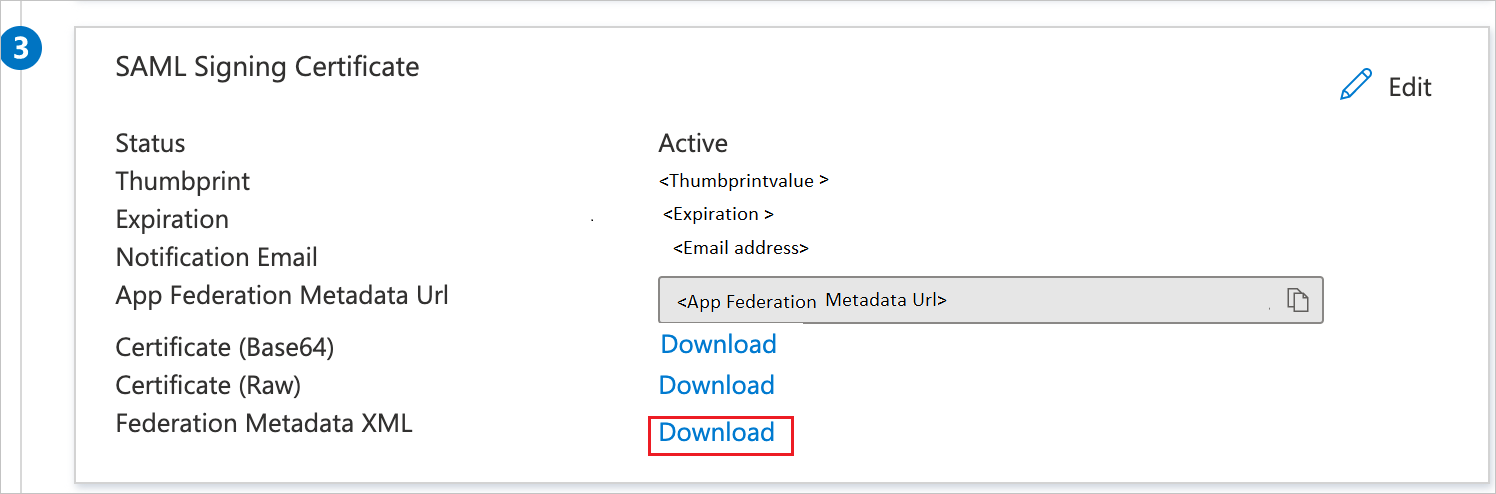
On the Set up single sign-on with SAML page, in the SAML Signing Certificate section, find Federation Metadata XML and select Download to download the certificate and save it on your computer.
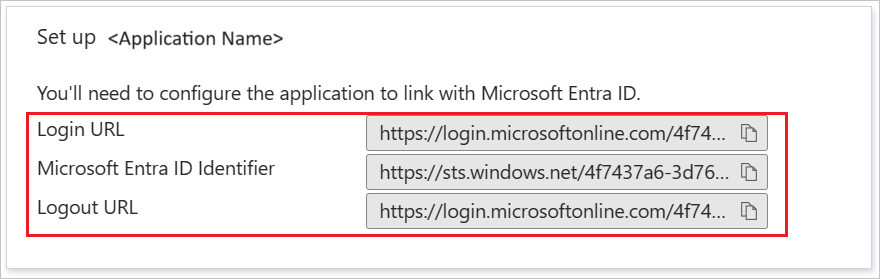
On the Set up Upshotly section, copy the appropriate URL(s) based on your requirement.
In this section, you'll create a test user called B.Simon.
B.Simon.B.Simon@contoso.com.In this section, you'll enable B.Simon to use single sign-on by granting access to Upshotly.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Upshotly.
In the app's overview page, find the Manage section and select Users and groups.
Select Add user, then select Users and groups in the Add Assignment dialog.
In the Users and groups dialog, select B.Simon from the Users list, then click the Select button at the bottom of the screen.
If you are expecting a role to be assigned to the users, you can select it from the Select a role dropdown. If no role has been set up for this app, you see "Default Access" role selected.
In the Add Assignment dialog, click the Assign button.
In a different web browser window, sign in to your Upshotly company site as an administrator
Click on the User Profile and navigate to Admin > SSO and perform the following steps:

a. Copy the Company ID value and use this Company ID value to replace Company ID value present in the Sign On URL in the Basic SAML Configuration section.
b. Open downloaded Federation metadata XML from Azure portal into Notepad, copy the content of metadata XML and paste it into XML metadata textbox.
In this section, you create a user called B.Simon in Upshotly Edge Cloud. Work with Upshotly Client support team to add the users in the Upshotly Edge Cloud platform. Users must be created and activated before you use single sign-on.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Click on Test this application, this will redirect to Upshotly Sign on URL where you can initiate the login flow.
Go to Upshotly Sign-on URL directly and initiate the login flow from there.
You can also use Microsoft My Apps to test the application in any mode. When you click the Upshotly tile in the My Apps, if configured in SP mode you would be redirected to the application sign on page for initiating the login flow and if configured in IDP mode, you should be automatically signed in to the Upshotly for which you set up the SSO. For more information about the My Apps, see Introduction to the My Apps.
Once you configure Upshotly you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
Events
9 Apr, 3 pm - 10 Apr, 12 pm
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowTraining
Module
Узнайте, как Внешняя идентификация Microsoft Entra обеспечить безопасный, простой вход для потребителей и бизнес-клиентов. Ознакомьтесь с созданием клиента, регистрацией приложений, настройкой потока и безопасностью учетной записи.
Certification
Microsoft Certified: Identity and Access Administrator Associate - Certifications
Продемонстрировать функции идентификатора Microsoft Entra для модернизации решений удостоверений, реализации гибридных решений и реализации управления удостоверениями.