Best practices for Microsoft Sentinel
This collection of best practices provides guidance to use when deploying, managing, and using Microsoft Sentinel, including links to other articles for more information.
Important
Before deploying Microsoft Sentinel, review and complete pre-deployment activities and prerequisites.
Best practice references
The Microsoft Sentinel documentation has best practice guidance scattered throughout our articles. In addition to the content provided in this article, see the following for more information:
Admin users:
- Pre-deployment activities and prerequisites for deploying Microsoft Sentinel
- Microsoft Sentinel workspace architecture best practices
- Design your Microsoft Sentinel workspace architecture
- Microsoft Sentinel sample workspace designs
- Data collection best practices
- Microsoft Sentinel costs and billing
- Permissions in Microsoft Sentinel
- Protecting MSSP intellectual property in Microsoft Sentinel
- Threat intelligence integration in Microsoft Sentinel
- Microsoft Sentinel content and solutions
- Audit Microsoft Sentinel queries and activities
Analysts:
For more information, also see our video: Architecting SecOps for Success: Best Practices for Deploying Microsoft Sentinel
Regular SOC activities to perform
Schedule the following Microsoft Sentinel activities regularly to ensure continued security best practices:
Daily tasks
Triage and investigate incidents. Review the Microsoft Sentinel Incidents page to check for new incidents generated by the currently configured analytics rules, and start investigating any new incidents. For more information, see Tutorial: Investigate incidents with Microsoft Sentinel.
Explore hunting queries and bookmarks. Explore results for all built-in queries, and update existing hunting queries and bookmarks. Manually generate new incidents or update old incidents if applicable. For more information, see:
Analytic rules. Review and enable new analytics rules as applicable, including both newly released or newly available rules from recently connected data connectors.
Data connectors. Review the status, date, and time of the last log received from each data connector to ensure that data is flowing. Check for new connectors, and review ingestion to ensure set limits haven't been exceeded. For more information, see Data collection best practices and Connect data sources.
Log Analytics Agent. Verify that servers and workstations are actively connected to the workspace, and troubleshoot and remediate any failed connections. For more information, see Log Analytics Agent overview.
Playbook failures. Verify playbook run statuses and troubleshoot any failures. For more information, see Tutorial: Use playbooks with automation rules in Microsoft Sentinel.
Weekly tasks
Content review of solutions or standalone content. Get any content updates for your installed solutions or standalone content from the Content hub. Review new solutions or standalone content that might be of value for your environment, such as analytics rules, workbooks, hunting queries, or playbooks.
Microsoft Sentinel auditing. Review Microsoft Sentinel activity to see who has updated or deleted resources, such as analytics rules, bookmarks, and so on. For more information, see Audit Microsoft Sentinel queries and activities.
Monthly tasks
Review user access. Review permissions for your users and check for inactive users. For more information, see Permissions in Microsoft Sentinel.
Log Analytics workspace review. Review that the Log Analytics workspace data retention policy still aligns with your organization's policy. For more information, see Data retention policy and Integrate Azure Data Explorer for long-term log retention.
Integrate with Microsoft security services
Microsoft Sentinel is empowered by the components that send data to your workspace, and is made stronger through integrations with other Microsoft services. Any logs ingested into products such as Microsoft Defender for Cloud Apps, Microsoft Defender for Endpoint, and Microsoft Defender for Identity allow these services to create detections, and in turn provide those detections to Microsoft Sentinel. Logs can also be ingested directly into Microsoft Sentinel to provide a fuller picture for events and incidents.
For example, the following image shows how Microsoft Sentinel ingests data from other Microsoft services and multi-cloud and partner platforms to provide coverage for your environment:
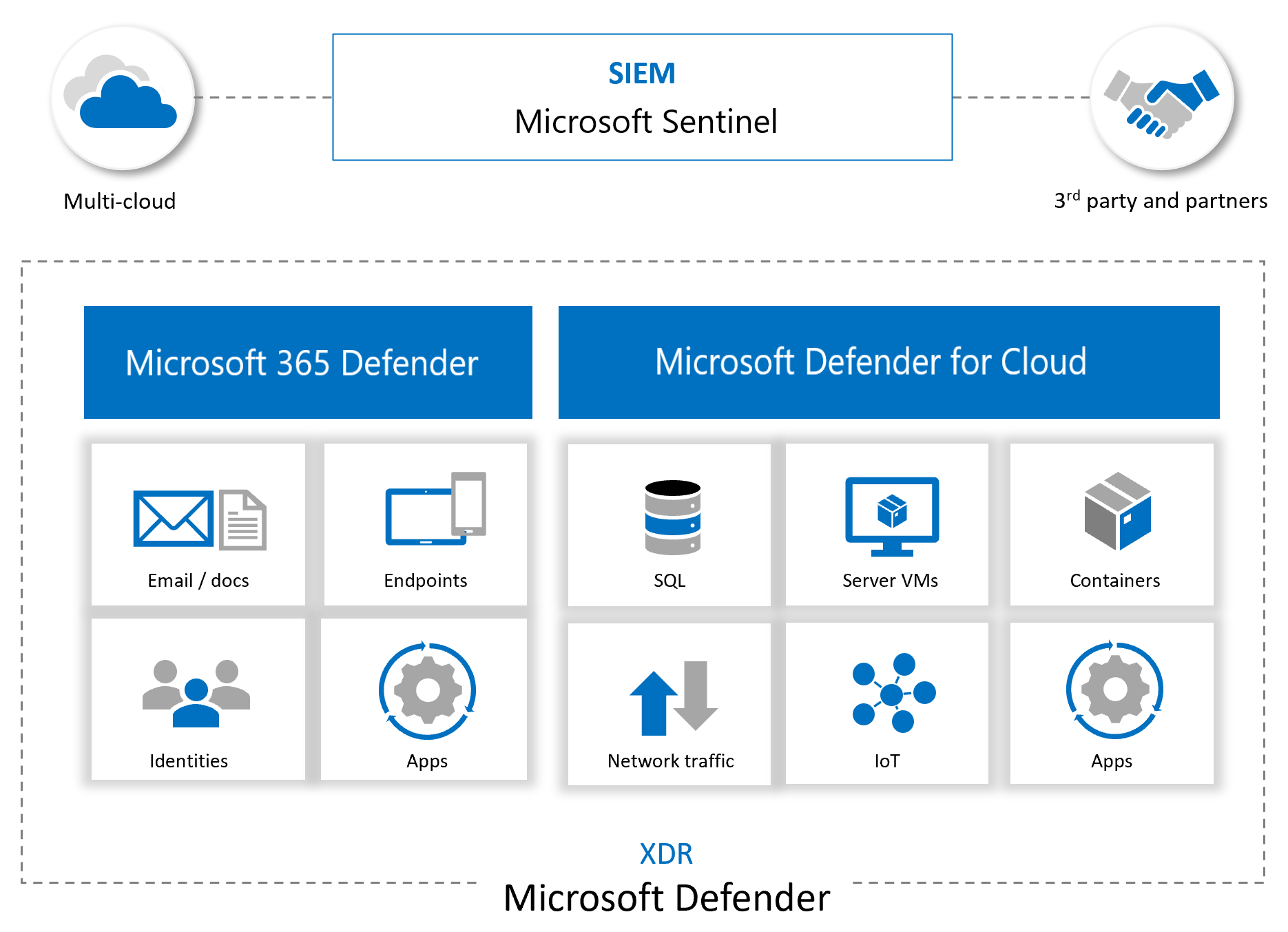
More than ingesting alerts and logs from other sources, Microsoft Sentinel also:
- Uses the information it ingests with machine learning that allows for better event correlation, alert aggregation, anomaly detection, and more.
- Builds and presents interactive visuals via workbooks, showing trends, related information, and key data used for both admin tasks and investigations.
- Runs playbooks to act on alerts, gathering information, performing actions on items, and sending notifications to various platforms.
- Integrates with partner platforms, such as ServiceNow and Jira, to provide essential services for SOC teams.
- Ingests and fetches enrichment feeds from threat intelligence platforms to bring valuable data for investigating.
Manage and respond to incidents
The following image shows recommended steps in an incident management and response process.
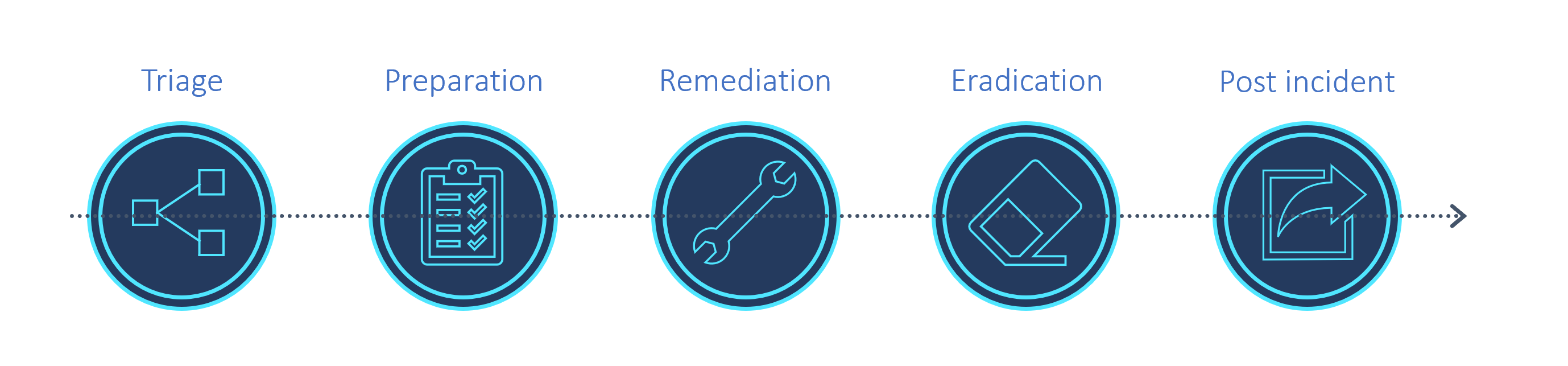
The following sections provide high-level descriptions for how to use Microsoft Sentinel features for incident management and response throughout the process. For more information, see Tutorial: Investigate incidents with Microsoft Sentinel.
Use the Incidents page and the Investigation graph
Start any triage process for new incidents on the Microsoft Sentinel Incidents page in Microsoft Sentinel and the Investigation graph.
Discover key entities, such as accounts, URLs, IP address, host names, activities, timeline, and more. Use this data to understand whether you have a false positive on hand, in which case you can close the incident directly.
Any generated incidents are displayed on the Incidents page, which serves as the central location for triage and early investigation. The Incidents page lists the title, severity, and related alerts, logs, and any entities of interest. Incidents also provide a quick jump into collected logs and any tools related to the incident.
The Incidents page works together with the Investigation graph, an interactive tool that allows users to explore and dive deep into an alert to show the full scope of an attack. Users can then construct a timeline of events and discover the extent of a threat chain.
If you discover that the incident is a true positive, take action directly from the Incidents page to investigate logs, entities, and explore the threat chain. After you've identified the threat and created a plan of action, use other tools in Microsoft Sentinel and other Microsoft security services to continue investigating.
Handle incidents with workbooks
In addition to visualizing and displaying information and trends, Microsoft Sentinel workbooks are valuable investigative tools.
For example, use the Investigation Insights workbook to investigate specific incidents together with any associated entities and alerts. This workbook enables you to dive deeper into entities by showing related logs, actions, and alerts.
Handle incidents with threat hunting
While investigating and searching for root causes, run built-in threat hunting queries and check results for any indicators of compromise.
During an investigation, or after having taken steps to remediate and eradicate the threat, use livestream to monitor, in real time, whether there are any lingering malicious events, or if malicious events are still continuing.
Handle incidents with entity behavior
Entity behavior in Microsoft Sentinel allows users to review and investigate actions and alerts for specific entities, such as investigating into accounts and host names. For more information, see:
- Enable User and Entity Behavior Analytics (UEBA) in Microsoft Sentinel
- Investigate incidents with UEBA data
- Microsoft Sentinel UEBA enrichments reference
Handle incidents with watchlists and threat intelligence
To maximize threat intelligence-based detections, make sure to use threat intelligence data connectors to ingest indicators of compromise:
- Connect data sources required by the Fusion and TI Map alerts
- Ingest indicators from TAXII and TIP platforms
Use indicators of compromise in analytics rules, when threat hunting, investigating logs, or generating more incidents.
Use a watchlist that combines data from ingested data and external sources, such as enrichment data. For example, create lists of IP address ranges used by your organization or recently terminated employees. Use watchlists with playbooks to gather enrichment data, such as adding malicious IP addresses to watchlists to use during detection, threat hunting, and investigations.
During an incident, use watchlists to contain investigation data, and then delete them when your investigation is done to ensure that sensitive data does not remain in view.
Next steps
To get started with Microsoft Sentinel, see:
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for