I am trying ti write a service that answers on https requests and process it.
For test purposes a generated a selfsignd ssl certificate with makecert and openssl and add it to the root and personal certificat.
In both cases, when i try
netsh http add sslcert ipport=0.0.0.0:8180 certhash=99858B7A5DF30E700653E7A832F21AB68722C93F appid={82f96a4e-ad9c-4448-9f69-e9e9150c661e}
i get error 1312 ssl certificate can't be added
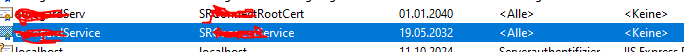
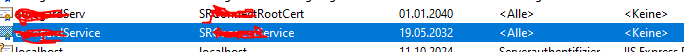
I checked in the personal certificate folder of local machine as in trusted root certificate, all certificate are present and valid
makecert
makecert -sky exchange -r -n "CN=SRRootCert,OU=myprog,O=company,L=city,S=NRW,C=DE" -pe -b 01/01/2021 -e 12/31/2031 -a sha256 -len 2048 -sv D:\Zertifikate\SRRootCA.pvk -ss SRCertStore D:\Zertifikate\SRRootCA.cer
makecert -sk SRRootCert -iv D:\Zertifikate\SRRootCA.pvk -n "CN=SRServ" -a sha256 -len 2048 -ic D:\Zertifikate\SRRootCA.cer D:\Zertifikate\SRService.cer -sr localmachine -ss SRCertStore
POWERSHELL Import-Certificate -FilePath "D:\Zertifikate\SRRootCA.cer" -CertStoreLocation Cert:\LocalMachine\Root
POWERSHELL Import-Certificate -FilePath "D:\Zertifikate\SRService.cer" -CertStoreLocation Cert:\LocalMachine\My
netsh http add sslcert ipport=0.0.0.0:8180 certhash=99858B7A5DF30E700653E7A832F21AB68722C93F appid={aaaaaa-aaaaaa-aaaa-aaaa-aaaaaaaaa}
And my try with openssl-
openssl genrsa -des3 -out D:\Zertifikate\ServicerootCA.key 2048
openssl req -x509 -new -nodes -key D:\Zertifikate\ServicerootCA.key -sha256 -days 4096 -out D:\Zertifikate\ServicerootCA.crt
openssl genrsa -out D:\Zertifikate\SRClient.key 2048
openssl req -new -sha256 -key D:\Zertifikate\SRClient.key -subj "/C=DE/ST=NRW/O=company/Lcity/CN=eService" -out D:\Zertifikate\SRClient.csr
openssl req -in D:\Zertifikate\SRClient.csr -noout -text
openssl x509 -req -in D:\Zertifikate\SRClient.csr -CA D:\Zertifikate\ServicerootCA.crt -CAkey D:\Zertifikate\ServicerootCA.key -CAcreateserial -out D:\Zertifikate\SRConnectClient.crt -days 4096 -sha256
openssl x509 -in D:\Zertifikate\SRClient.crt -text -noout
POWERSHELL Import-Certificate -FilePath "D:\Zertifikate\EServicerootCA.crt" -CertStoreLocation Cert:\LocalMachine\Root
POWERSHELL Import-Certificate -FilePath "D:\Zertifikate\SRClient.crt" -CertStoreLocation Cert:\LocalMachine\My
and then
netsh http add sslcert ipport=0.0.0.0:8180 certhash=99858B7A5DF30E700653E7A832F21AB68722C93F appid={aaaaaa-aaaaaa-aaaa-aaaa-aaaaaaaaa}
Every step is tested and runs without error, files a re created checks run and finally add to the cetificat storage, but but produce an error.
To test netsh http add sslcert, i bond another certificat that was made for us by a "official" CA and it runs.
So nothing basically is wrong with the final step, but i can't figure out why it will not accept the self signed certifucates, which
which are as shown in the image registered and valid.
I also added the certificates with the mmc only to see if it makes any difference, which it didn't .
And in added the certificate, to the personal folder