/common accepts both OrgID and MicrosoftIDs, for your scenario you'd want to use https://login.microsoftonline.com/organizations/ instead. This will "force" the app to only accept other Azure AD/Office 365 accounts, more info here: https://learn.microsoft.com/bs-latn-ba/azure/active-directory/develop/msal-client-application-configuration#authority
AADSTS50020 Error when trying to sign in with live MS account: msalConfig
Hi, I would like to know if it is possible to fix this error which I am receiving with error code AADSTS50020.
The problem is that when I was testing the sign-in option, it was working just fine, but when my friend tried it, it gave an error mentioned.
As I understood the error, it is because the user is logged in using the live account in the management portal.
What I've found on the internet is that I need to add a parameter in url &domain_hint=http://foo.com for it to fix it, but I am unsure how.
I also found on the document saying:
authority: Optional. A URL indicating a directory that MSAL can request tokens from. Default value is:
https://login.microsoftonline.com/common.
The only thing that worked for me was the https://login.microsoftonline.com/
Everything else was giving me this message:
We're unable to complete your request
unauthorized_client: The client does not exist or is not enabled for consumers. If you are the >application developer, configure a new application through the App Registrations in the Azure >Portal at https://go.microsoft.com/fwlink/?linkid=2083908.
How can I fix the issue?
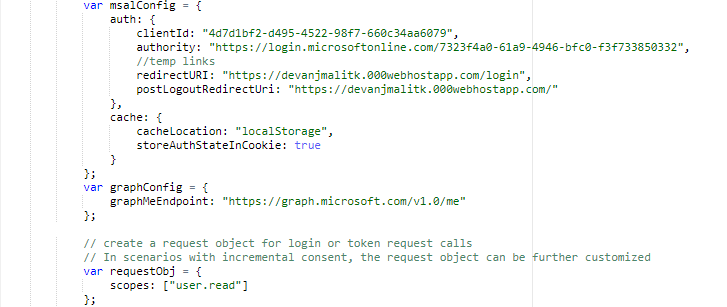
Here's the current config:
var msalConfig = { auth: { clientId: "4d7d1bf2-d495-4522-98f7-660c34aa6079", authority: "https://login.microsoftonline.com/7323f4a0-61a9-4946-bfc0-f3f733850332", //temp links redirectURI: "https://devanjmalitk.000webhostapp.com/login", postLogoutRedirectUri: "https://devanjmalitk.000webhostapp.com/" }, cache: { cacheLocation: "localStorage", storeAuthStateInCookie: true } }; var graphConfig = { graphMeEndpoint: "https://graph.microsoft.com/v1.0/me" };
If there is anything else you need, please let me know, thank you.
1 additional answer
Sort by: Most helpful
-
vanjmali 26 Reputation points
2020-01-07T18:20:58.967+00:00 I would rather want to connect using personal accounts, using https://login.microsoftonline.com/consumers/ or https://login.microsoftonline.com/common/ gives me
unauthorized_client: The client does not exist or is not enabled for consumers.
as mentioned already and the only ones working are https://login.microsoftonline.com/organizations/ and https://login.microsoftonline.com//
Can I somehow use the common link rather than organizations without receiving the error?
