As per my research , there are two events to look out for after successful KRBTGT Password Reset :
1st event that gets triggered is 4738
2nd event that gets triggered is 4724
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Hello Team,
Please help.
I have used the KRBTGT script/ ADUC console to perform the reset of KRBTGT and in both the cases I have NOT observed Event ID's generated on Domain controller.
Script downloaded from below:
https://gist.github.com/mubix/fd0c89ec021f70023695
Guess its an older version of script but we dont have RODC hence should be good enough I believe and i have tested in the Test environment hence will be using it on the production.
AD Environment details:
OS : 2019
DFL/FFL - 2012 R2
Below events are for 2008 Domain controller, where do I find the events equivalent to below on my 2019 Domain controller where I run the script.
KDC Password Configuration
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2008-r2-and-2008/cc733984(v=ws.10)
Event ID 9 and 10
Source - Microsoft-Windows-Kerberos-Key-Distribution-Center
Kerberos Key Integrity
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2008-r2-and-2008/cc734061(v=ws.10)
Event ID 13,14,16
Source : Microsoft-Windows-Kerberos-Key-Distribution-Center
As per my research , there are two events to look out for after successful KRBTGT Password Reset :
1st event that gets triggered is 4738
2nd event that gets triggered is 4724
Hello @Shadab Basha ,
Thank you so much for posting here.
I tried to open the provided links but could not succeed. I am wondering whether all goes well when we tried to reset the krbtgt password.
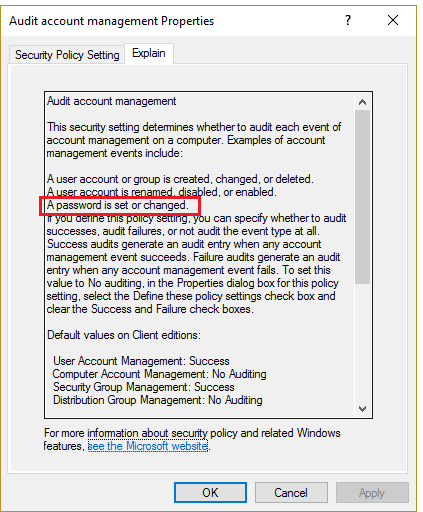
Besides, if we would like to audit the change of AD account, we could enable the audit. For more information about the audit, we could refer to:
https://www.lepide.com/how-to/track-password-changes-and-resets-in-active-directory.html
Please note: Information posted in the given link is hosted by a third party. Microsoft does not guarantee the accuracy and effectiveness of information.
Thanks a lot.
Best regards,
Hannah Xiong
Hello @Hannah Xiong
Thank you for the response.
The links are working but clicking on the links is trimming off the last bracket ")" of the URL and hence we get 404
Please copy and paste the links instead.
KDC Password Configuration
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2008-r2-and-2008/cc733984(v=ws.10)
Event ID 9 and 10
Source - Microsoft-Windows-Kerberos-Key-Distribution-Center
Kerberos Key Integrity
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2008-r2-and-2008/cc734061(v=ws.10)
Regarding the Auditing , yes that's enabled however will that trigger for KRBTGT account as well ?
The event ID Event ID 4723, should it be considered equivalent to the event ID 9 which is specifically meant for KRBTGT ?
=================
Event ID 9 — KDC Password Configuration
02/02/2010
2 minutes to read
Applies To: Windows Server 2008
The Kerberos ticket-granting ticket (TGT) is enciphered with the Kerberos Key Distribution Center (KDC) account's password. The TGT is issued to the Kerberos client from the KDC.
Event Details
EVENT DETAILS
Product: Windows Operating System
ID: 9
Source: Microsoft-Windows-Kerberos-Key-Distribution-Center
Version: 6.0
Symbolic Name: KDCEVENT_KRBTGT_PASSWORD_CHANGED
Message: The password on the KRBTGT account was changed.
End Goal - During a KRBTGT Password Reset, I would like to know the event ID's which can confirm if the KRBTGT password is success or failure and any other Event ID's which needs to be verified.
The event ID's in the link provided are quite critical ones so I am expecting equivalent event ID's to be available for windows 2019 Domain controller.
Currently I am relying on the PWDlastset attribute on the KRBTGT account to check if pwd has been updated.
Hello @Shadab Basha ,
Thank you so much for your kindly reply.
If we have enabled the audit for AD accounts, normally it will trigger for KRBTGT account as well. And it will tell us the information about the password reset or change from the event ID 4723.
I totally understand that we need to check the event ID 9 or 10 to confirm whether the KRBTGT password reset is successful or failed. Yeah, we could check the PwdLastset attribute for the update. This attribute is crucial and reliable.
Besides, when we performed the operations to reset KRBTGT password, is there any error or failed checking? If all goes well without any error or failed checking, and the Pwdlastset attribute is updated, I think all should be Okay.
For any question, please feel free to contact us.
Best regards,
Hannah Xiong
Hello @Hannah Xiong ,
sorry was on Annual Leave.
So as per you , the only ways to confirm KRBTGT password reset is pwdlastset attribute and event ID 4723 and no other events to monitor during the KRBTGT password reset.
If yes, then thank you for your assistance .. no more queries.