Azure key vault is another way to manage storage account keys.
Storage account keys can be stored as key vault secrets which can help to sync the keys with the storage account by regenerating the keys on a schedule that is configured. The storage account key values are never returned. So shared access signature definitions are set up for account level or service level SAS tokens. Then when an application calls the REST URI path the key vault generates a SAS token using the storage account key and the shared access signature template and returns it to the caller as a key vault secret, and the application then can use the SAS token to authenticate to azure storage.
By default Global administrator have access to your key vault.
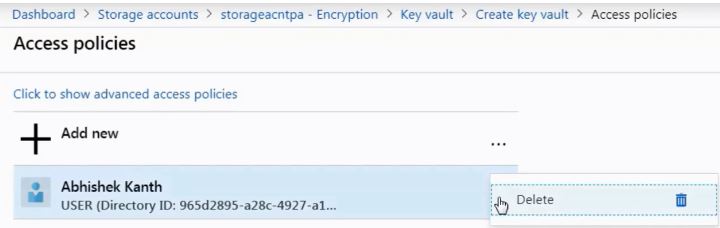
But while creating key vault, below pricing tier you will find an option Access Policies.
If you go to this access policy section you can see a default access policy is applied to the user who is the global administrator. If you want to remove any access policy here then you can click on context menu and delete it.
@kanna : You can find the step by step process for azure key vault in below blog post: