@Walid Mougharbel
Thank you for your post! In order to better understand why SAML is the default method, we have to first understand the difference between OAuth, OpenID Connect, and SAML. I found a Stack Overflow post that explains it perfectly and will post the answer below.
OAuth2.0:
OAuth2 builds the trust relation on a direct HTTPs call from the application to the identity. The request contains the access token (obtained by the application during the protocol flow) and the response contains the information about the user.
OpenID Connect:
OpenID Connect further expands this to make it possible to obtain the identity without this extra step involving the call from the application to the identity provider.
SAML:
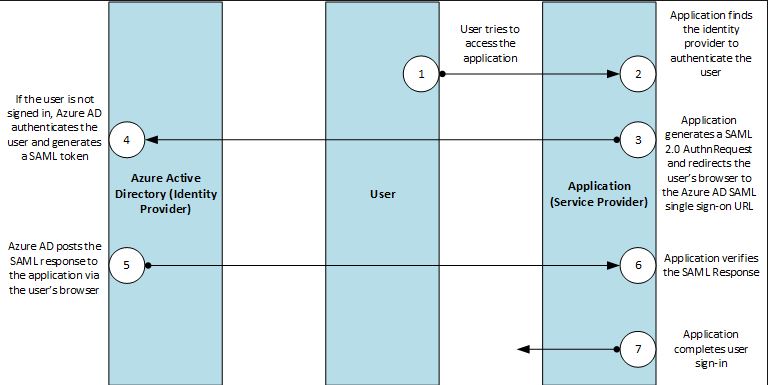
SAML builds the trust relation on a digital signature, SAML tokens issued by the identity provider are signed XMLs, the application validates the signature itself and the certificate it presents. The user information is included in a SAML token, among other information. SAML is also based on an explicit trust between your site and the identity provider so it's rather uncommon to accept credentials from an unknown site.
Looking at the SalesForce SSO documentation, it's utilizing SAML for multiple reasons, you can:
-Control in AzureAD who has access to SalesForce
-Enable your users to be automatically signed-in to Salesforce with their Azure AD accounts.
-Manage your accounts in one central location - the Azure portal.
Please let me know if you have any other questions.
Thank you for your time and patience!