Hello all,
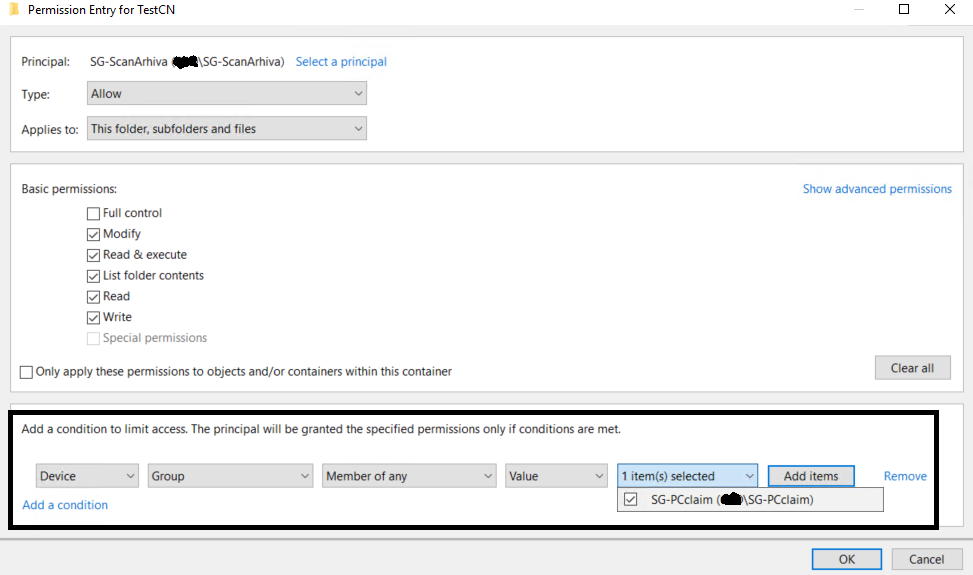
I have "simple" problem and DAC is simple solution for me. I have security group with users that can access certain folder on our FS (servers 2019). But they should be able to access mentioned folder ONLY from ONE or TWO workstations (win10 or server 2019)
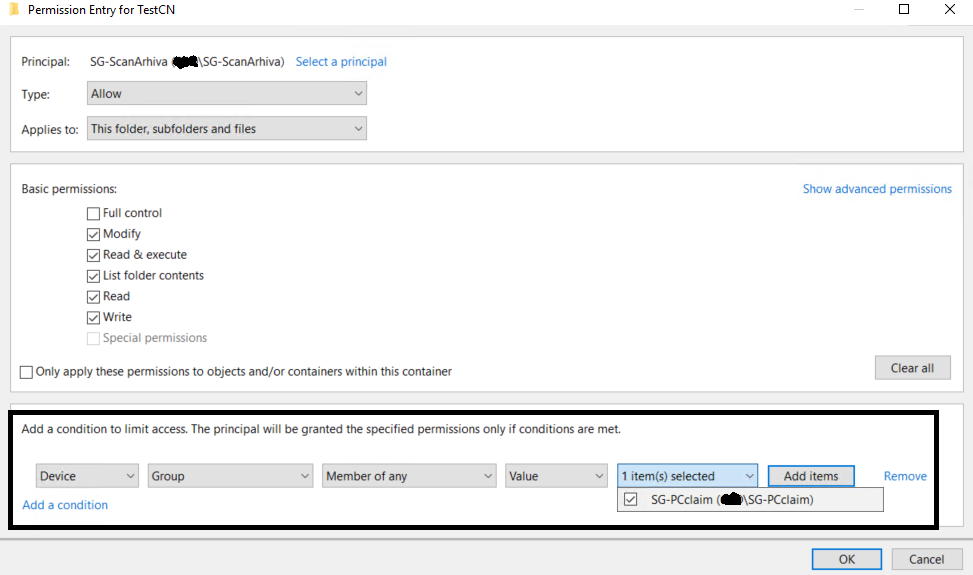
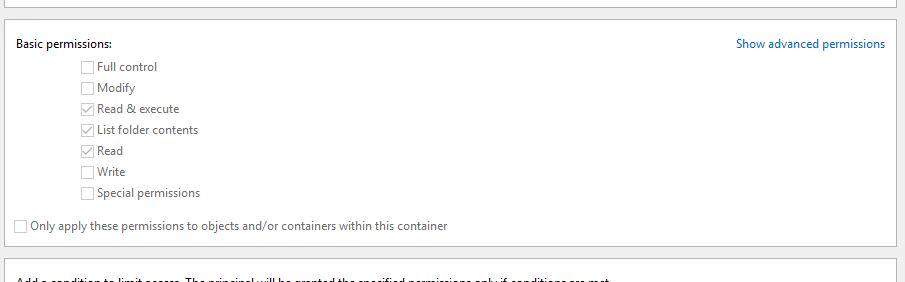
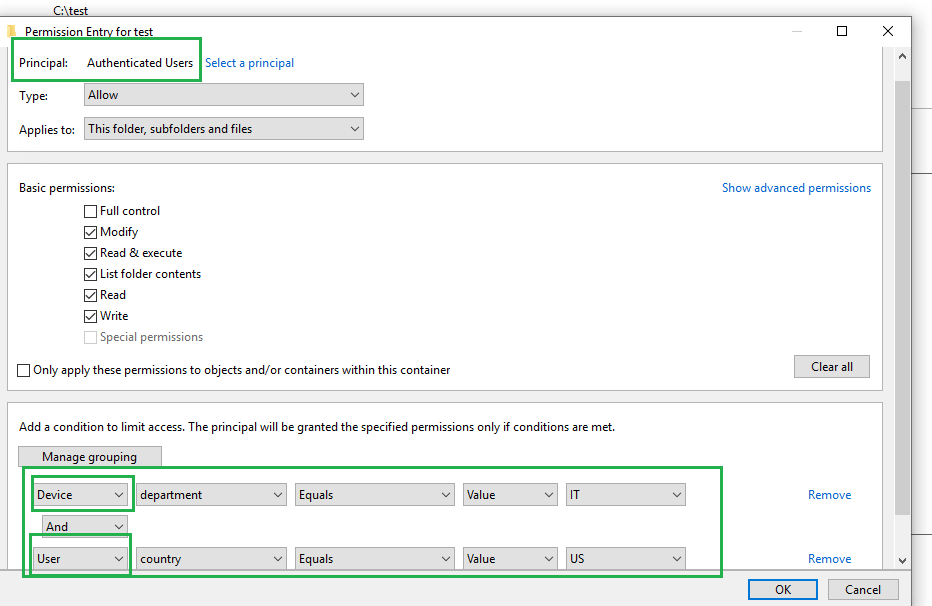
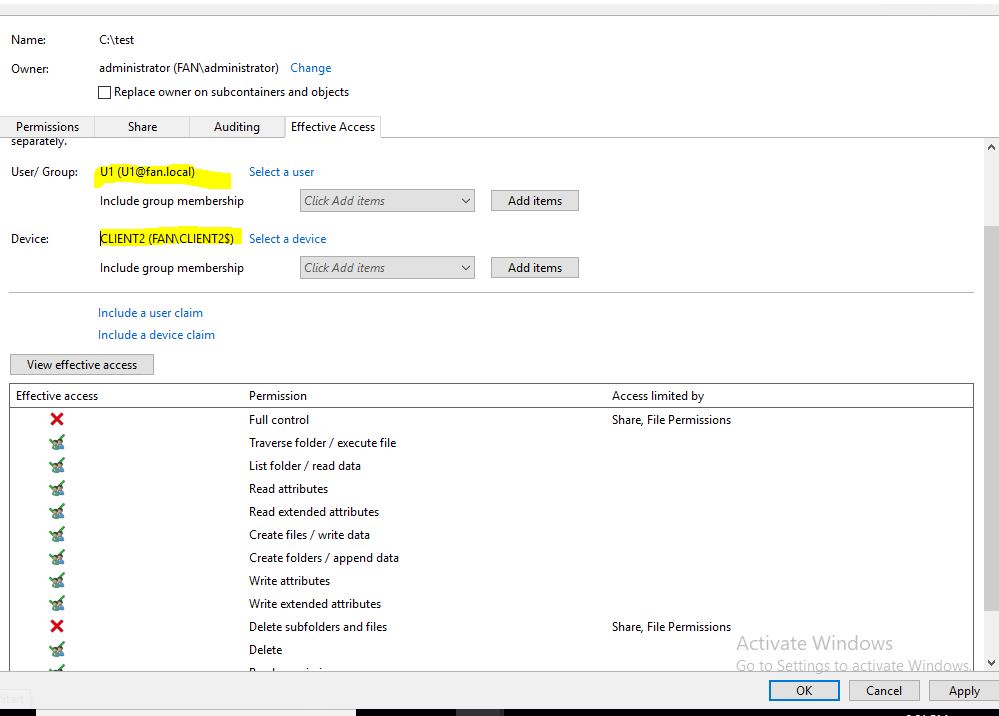
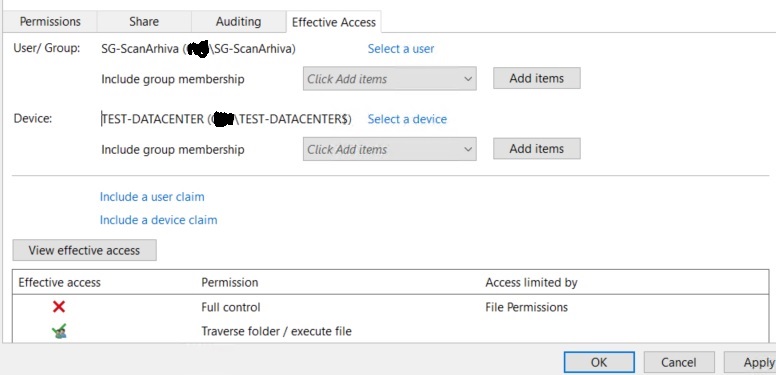
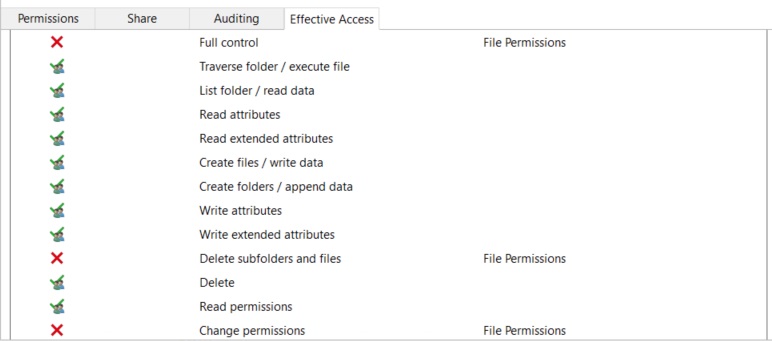
Picture above represents NTFS permissions I want...and adding DEVICE claim should do the work. But DEVICE CLAIMS are NOT working. USER CLAIMS work.
1.GPO "kerberos armoring" for domain controllers (all 2016) is in place.
2.GPO "Kerberos client support for claims" is in place for needed workstations (win10)
SG-scanarhiva contains users, SG-PCclaim contains workstations from witch SG-scanarhiva should access folder testCN.
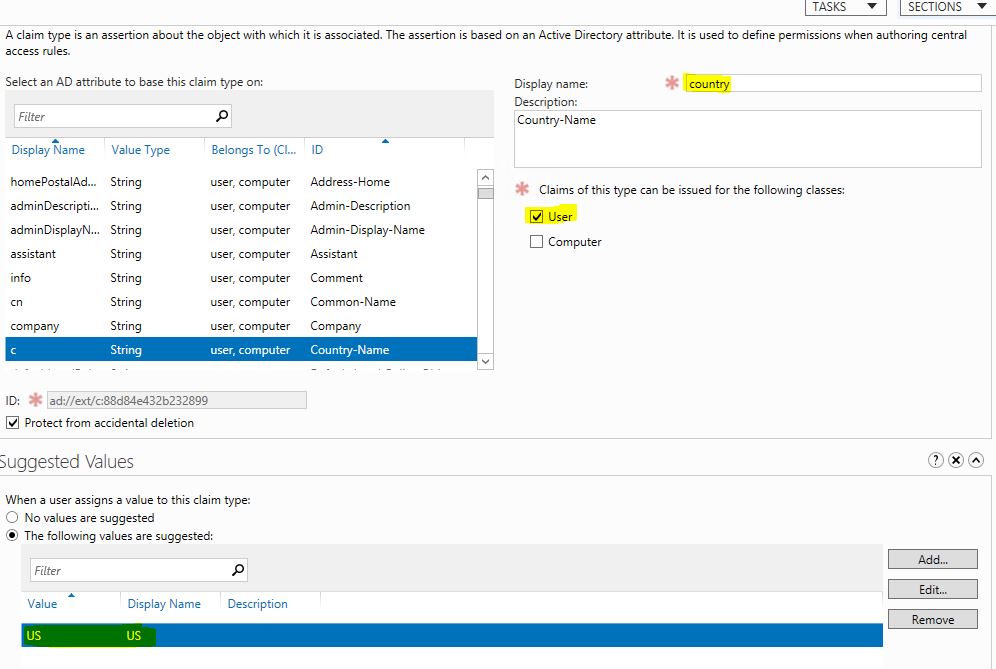
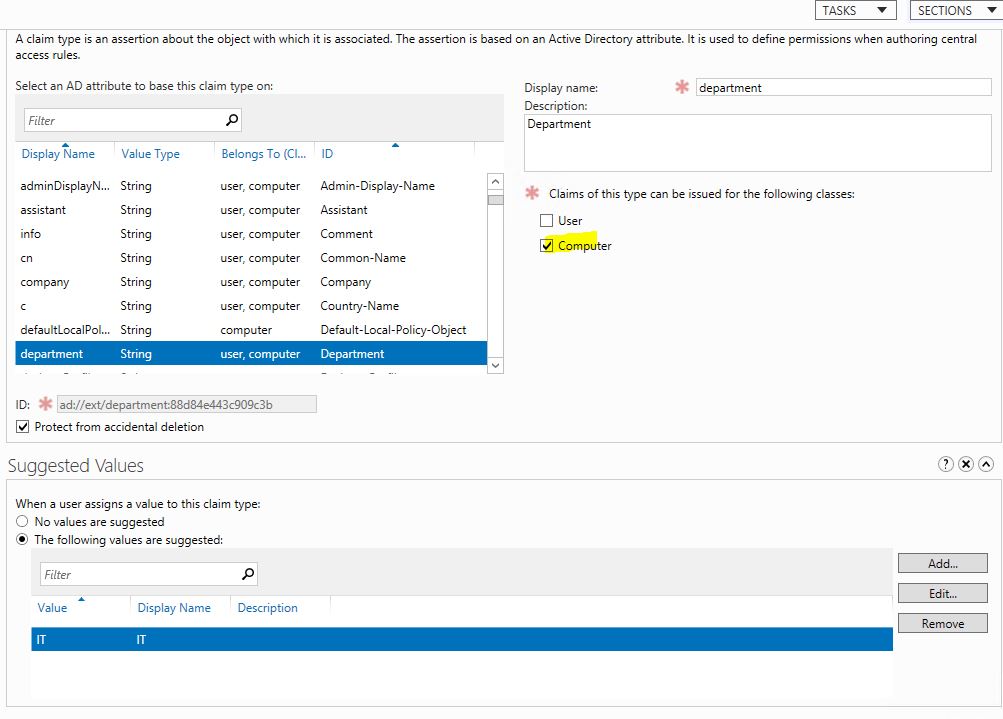
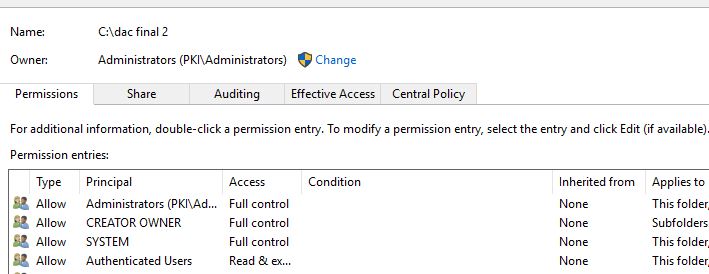
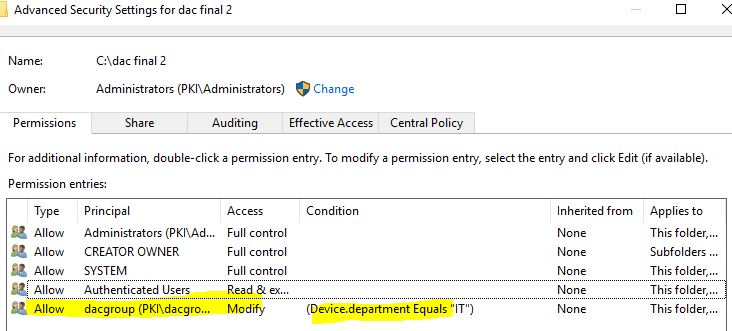
Like i mentioned user claims work. I created new "Claim type" in ADAC and tested it with department atribute. All users having for example "IT" string in department field can access folder. Users without cannot.
When i type "whoami /claims" i cmd i can clearly see claims for particular user.
Problem is whatever combination I try with DEVICE CLAIM, with any attribute (CN, department...etc) folder does not give NTFS access.
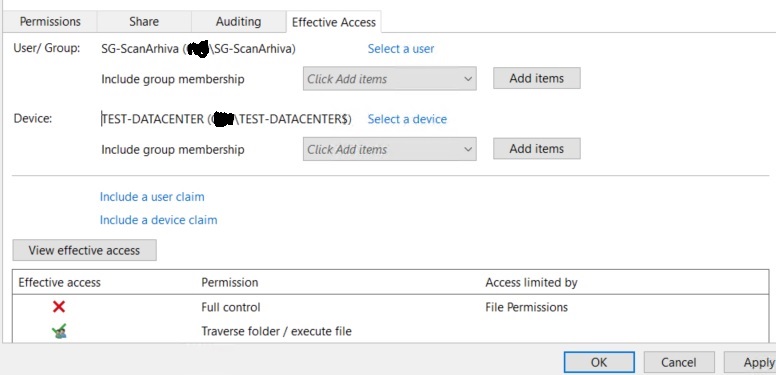
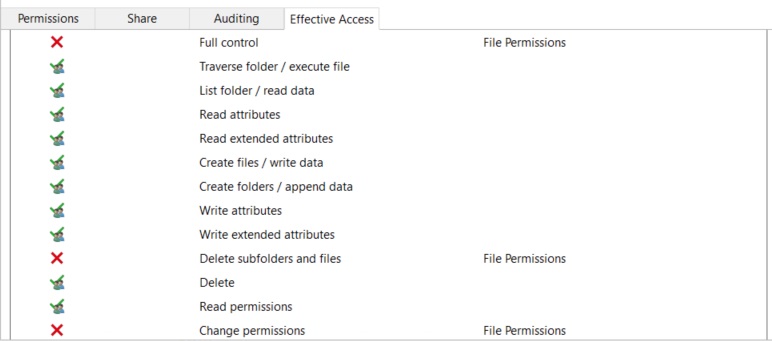
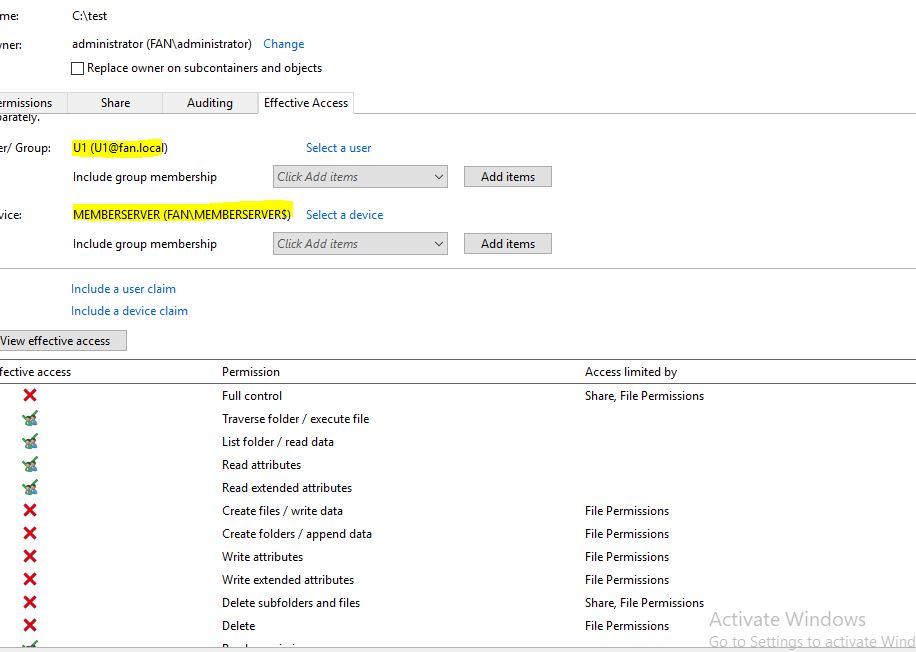
But if I test it in "effective access" looks like I should have permissions.
I really don't know how to troubleshoot Device claims... What is the difference between device and user claims?? Can you help me and point me to right direction ??
Additionally, i tried to make device claims based on department, CN and location... (same way like i do for users and for users it works). But with devices, No luck..
And I want't to check device claims by runing: New-Object System.Security.Principal.WindowsIdentity("PC$@keyman .local")
result is:
DeviceClaims : {}