Enable combined security information registration in Microsoft Entra ID
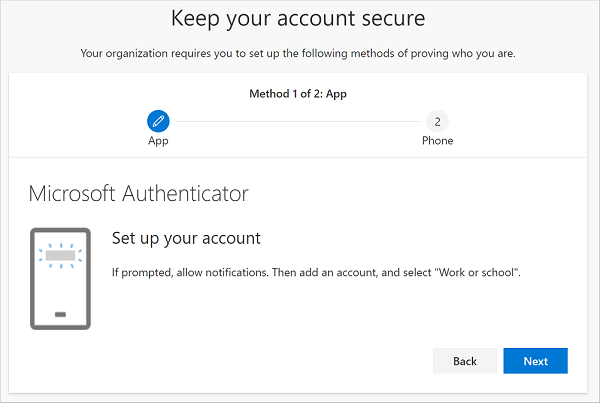
Before combined registration, users registered authentication methods for Microsoft Entra multifactor authentication and self-service password reset (SSPR) separately. Users were confused that similar methods were used for Microsoft Entra multifactor authentication and SSPR but they had to register for both features. Now, with combined registration, users can register once and get the benefits of both Microsoft Entra multifactor authentication and SSPR.
To help you understand the functionality and effects of the new experience, see the Combined security information registration concepts.
Conditional Access policies for combined registration
To secure when and how users register for Microsoft Entra multifactor authentication and self-service password reset, you can use user actions in Conditional Access policy. This functionality may be enabled in organizations that want users to register for Microsoft Entra multifactor authentication and SSPR from a central location, such as a trusted network location during HR onboarding.
Note
This policy applies only when a user accesses a combined registration page. This policy doesn't enforce MFA enrollment when a user accesses other applications.
You can create an MFA registration policy by using Microsoft Entra ID Protection - Configure MFA Policy.
For more information about creating trusted locations in Conditional Access, see What is the location condition in Microsoft Entra Conditional Access?
Create a policy to require registration from a trusted location
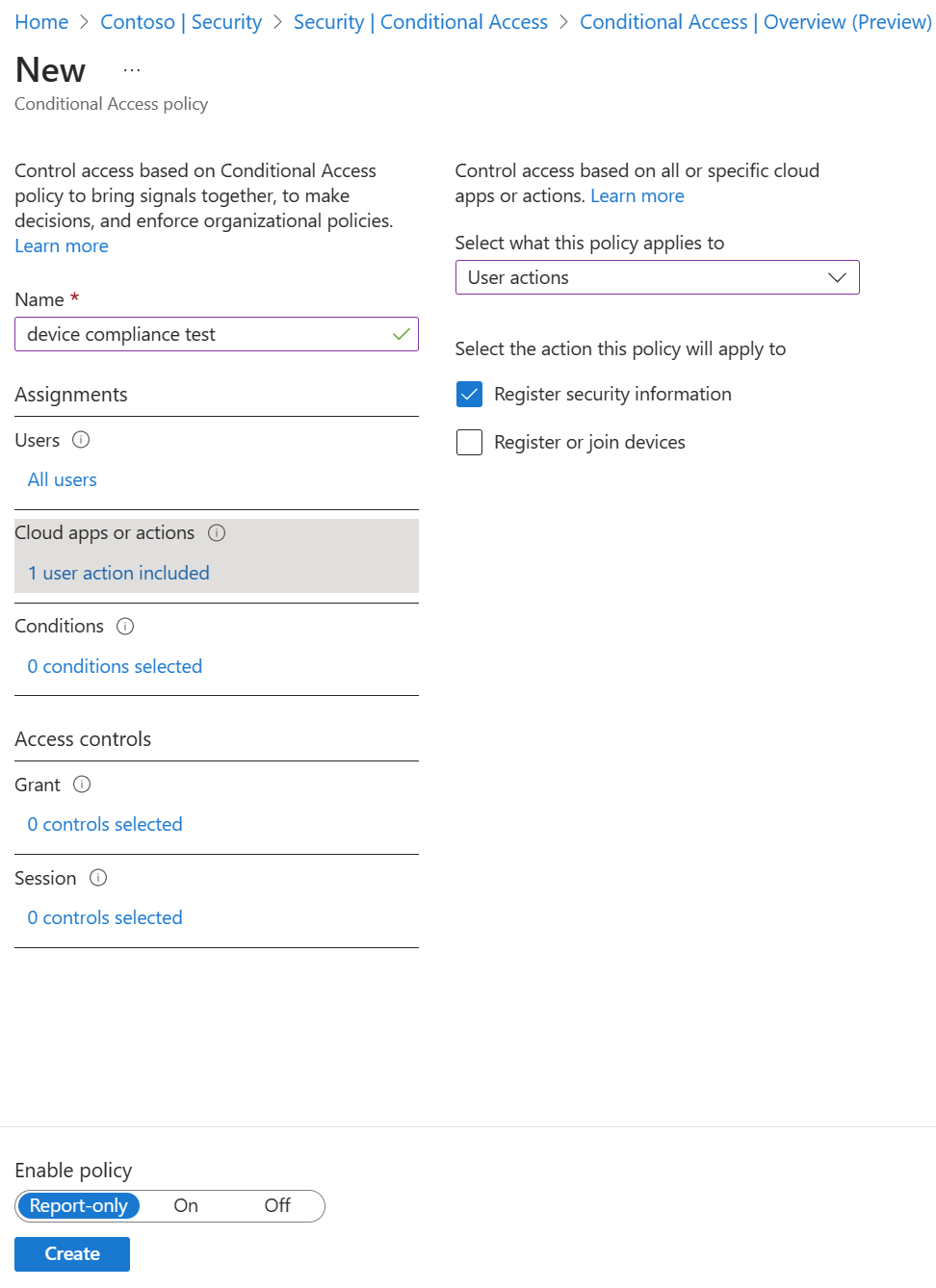
Complete the following steps to create a policy that applies to all selected users that attempt to register using the combined registration experience, and blocks access unless they are connecting from a location marked as trusted network:
Sign in to the Microsoft Entra admin center as at least an Conditional Access Administrator.
Browse to Protection > Conditional Access.
Select + New policy.
Enter a name for this policy, such as Combined Security Info Registration on Trusted Networks.
Under Assignments, select Users. Choose the users and groups you want this policy to apply to.
Warning
Users must be enabled for combined registration.
Under Cloud apps or actions, select User actions. Check Register security information, then select Done.
Under Conditions > Locations, configure the following options:
- Configure Yes.
- Include Any location.
- Exclude All trusted locations.
Under Access controls > Grant, choose Block access, then Select.
Set Enable policy to On.
To finalize the policy, select Create.
Next steps
If you need help, see troubleshoot combined security info registration or learn What is the location condition in Microsoft Entra Conditional Access?
Review how you can enable self-service password reset and enable Microsoft Entra multifactor authentication in your tenant.
If needed, learn how to force users to re-register authentication methods.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for