Tutorial: Configure Datawiza to enable Microsoft Entra multifactor authentication and single sign-on to Oracle PeopleSoft
In this tutorial, learn how to enable Microsoft Entra single sign-on (SSO) and Microsoft Entra multifactor authentication for an Oracle PeopleSoft application using Datawiza Access Proxy (DAP).
Learn more: Datawiza Access Proxy
Benefits of integrating applications with Microsoft Entra ID using DAP:
- Embrace proactive security with Zero Trust - a security model that adapts to modern environments and embraces hybrid workplace, while it protects people, devices, apps, and data
- Microsoft Entra single sign-on - secure and seamless access for users and apps, from any location, using a device
- How it works: Microsoft Entra multifactor authentication - users are prompted during sign-in for forms of identification, such as a code on their cellphone or a fingerprint scan
- What is Conditional Access? - policies are if-then statements, if a user wants to access a resource, then they must complete an action
- Easy authentication and authorization in Microsoft Entra ID with no-code Datawiza - use web applications such as: Oracle JDE, Oracle E-Business Suite, Oracle Sibel, and home-grown apps
- Use the Datawiza Cloud Management Console (DCMC) - manage access to applications in public clouds and on-premises
Scenario description
This scenario focuses on Oracle PeopleSoft application integration using HTTP authorization headers to manage access to protected content.
In legacy applications, due to the absence of modern protocol support, a direct integration with Microsoft Entra SSO is difficult. Datawiza Access Proxy (DAP) bridges the gap between the legacy application and the modern ID control plane, through protocol transitioning. DAP lowers integration overhead, saves engineering time, and improves application security.
Scenario architecture
The scenario solution has the following components:
- Microsoft Entra ID - identity and access management service that helps users sign in and access external and internal resources
- Datawiza Access Proxy (DAP) - container-based reverse-proxy that implements OpenID Connect (OIDC), OAuth, or Security Assertion Markup Language (SAML) for user sign-in flow. It passes identity transparently to applications through HTTP headers.
- Datawiza Cloud Management Console (DCMC) - administrators manage DAP with UI and RESTful APIs to configure DAP and access control policies
- Oracle PeopleSoft application - legacy application to be protected by Microsoft Entra ID and DAP
Learn more: Datawiza and Microsoft Entra authentication architecture
Prerequisites
Ensure the following prerequisites are met.
- An Azure subscription
- If you don't have one, you can get an Azure free account
- A Microsoft Entra tenant linked to the Azure subscription
- Docker and Docker Compose
- Go to docs.docker.com to Get Docker and Install Docker Compose
- User identities synchronized from an on-premises directory to Microsoft Entra ID, or created in Microsoft Entra ID and flowed back to an on-premises directory
- An account with Microsoft Entra ID and the Application Administrator role
- An Oracle PeopleSoft environment
- (Optional) An SSL web certificate to publish services over HTTPS. You can use default Datawiza self-signed certs for testing.
Getting started with DAP
To integrate Oracle PeopleSoft with Microsoft Entra ID:
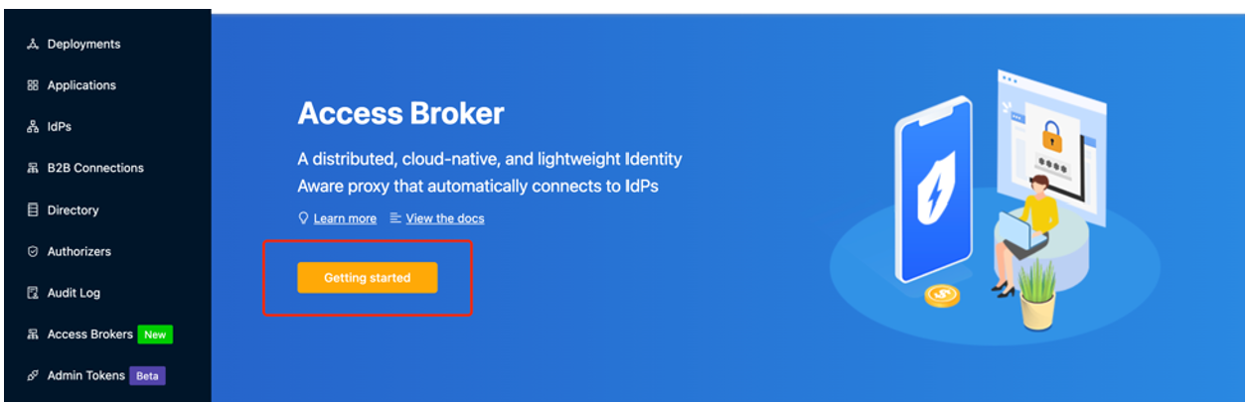
Sign in to Datawiza Cloud Management Console (DCMC).
The Welcome page appears.
Select the orange Getting started button.
In the Name and Description fields, enter information.
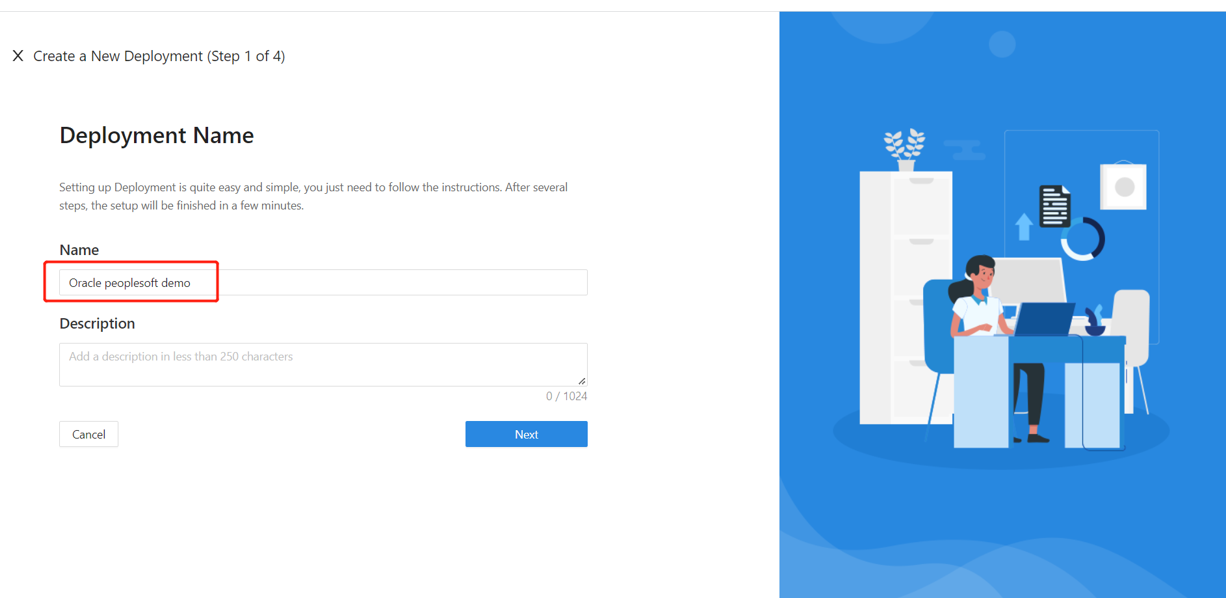
Select Next.
The Add Application dialog appears.
For Platform, select Web.
For App Name, enter a unique application name.
For Public Domain, for example use
https://ps-external.example.com. For testing, you can use localhost DNS. If you aren't deploying DAP behind a load balancer, use the Public Domain port.For Listen Port, select the port that DAP listens on.
For Upstream Servers, select the Oracle PeopleSoft implementation URL and port to be protected.
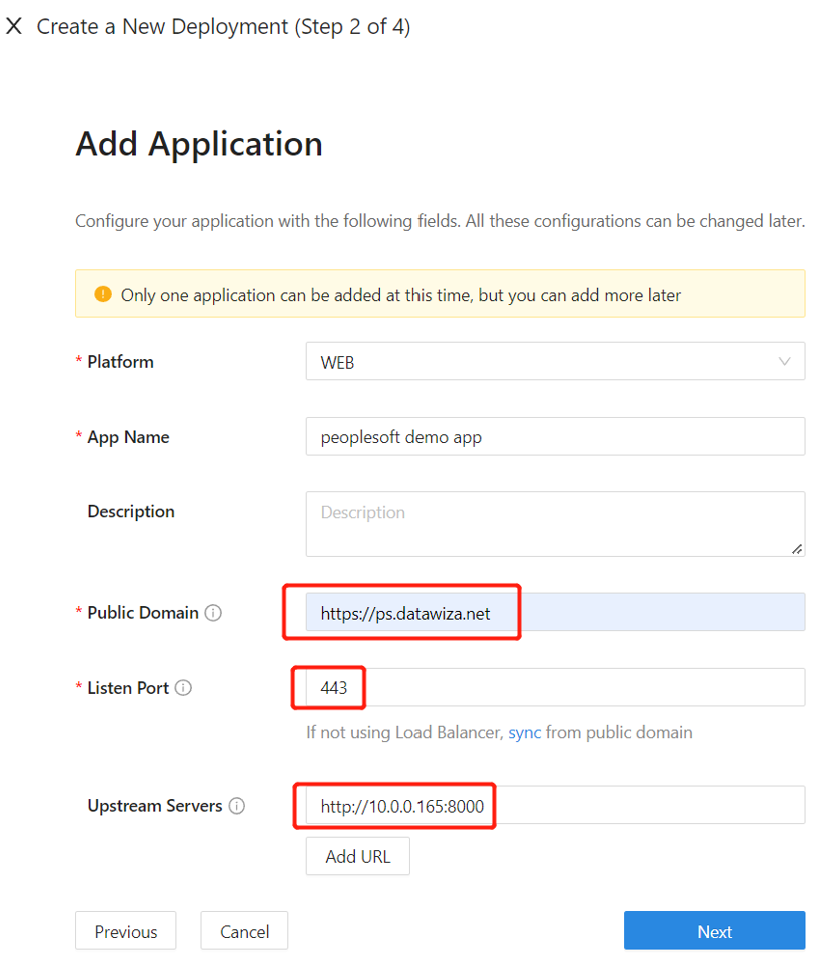
- Select Next.
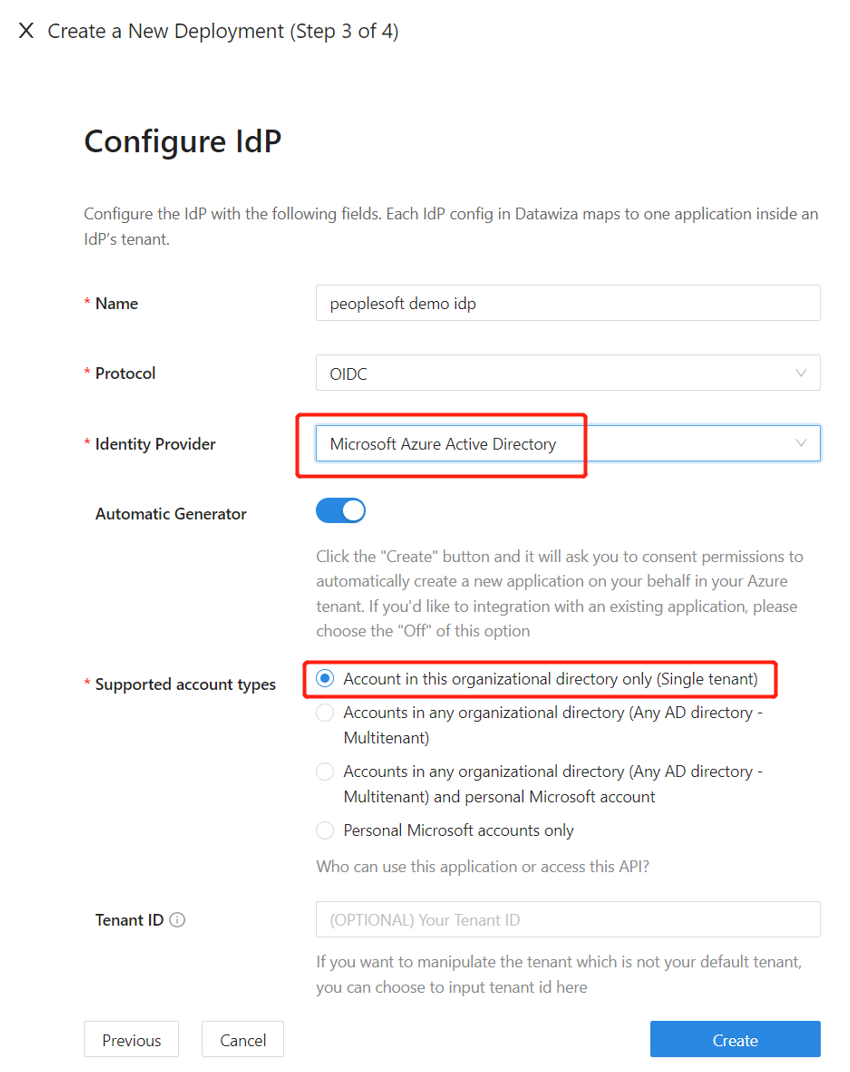
- On the Configure IdP dialog, enter information.
Note
DCMC has one-click integration to help complete Microsoft Entra configuration. DCMC calls the Microsoft Graph API to create an application registration on your behalf in your Microsoft Entra tenant. Learn more at docs.datawiza.com in One Click Integration with Microsoft Entra ID
- Select Create.
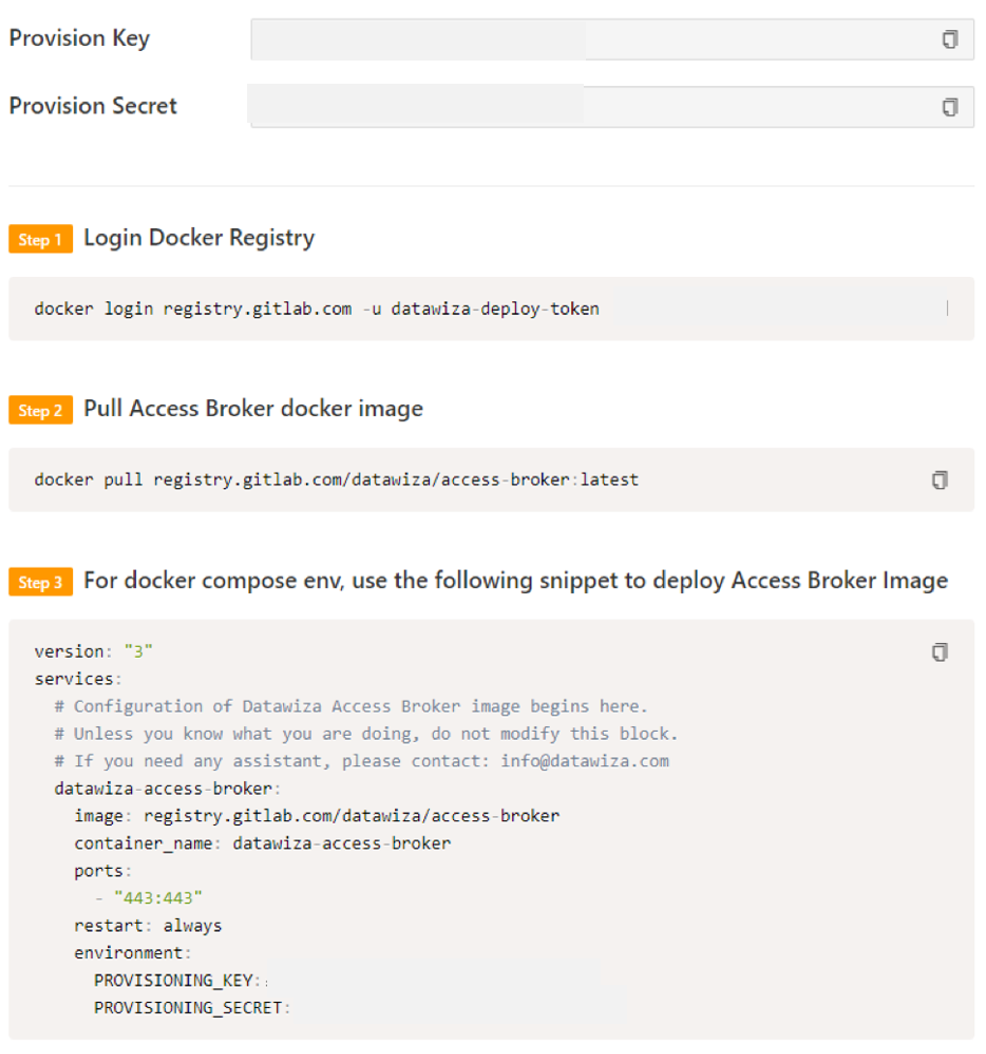
- The DAP deployment page appears.
- Make a note of the deployment Docker Compose file. The file includes the DAP image, the Provisioning Key and Provision Secret, which pulls the latest configuration and policies from DCMC.
SSO and HTTP headers
DAP gets user attributes from the identity provider (IdP) and passes them to the upstream application with a header or cookie.
The Oracle PeopleSoft application needs to recognize the user. Using a name, the application instructs DAP to pass the values from the IdP to the application through the HTTP header.
In Oracle PeopleSoft, from the left navigation, select Applications.
Select the Attribute Pass subtab.
For Field, select email.
For Expected, select PS_SSO_UID.
For Type, select Header.
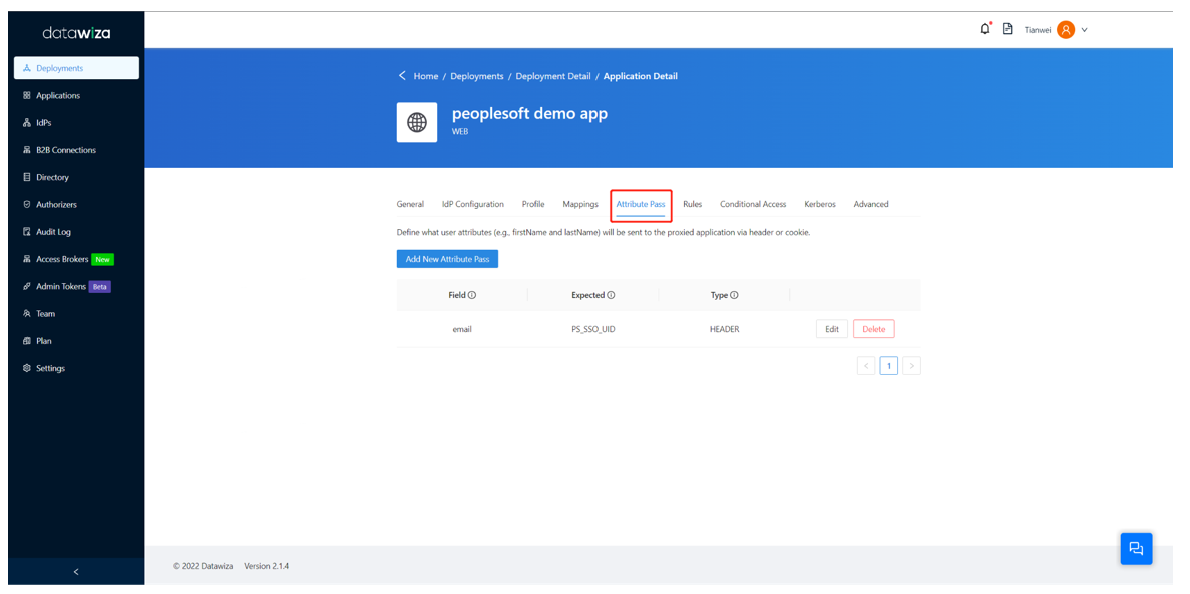
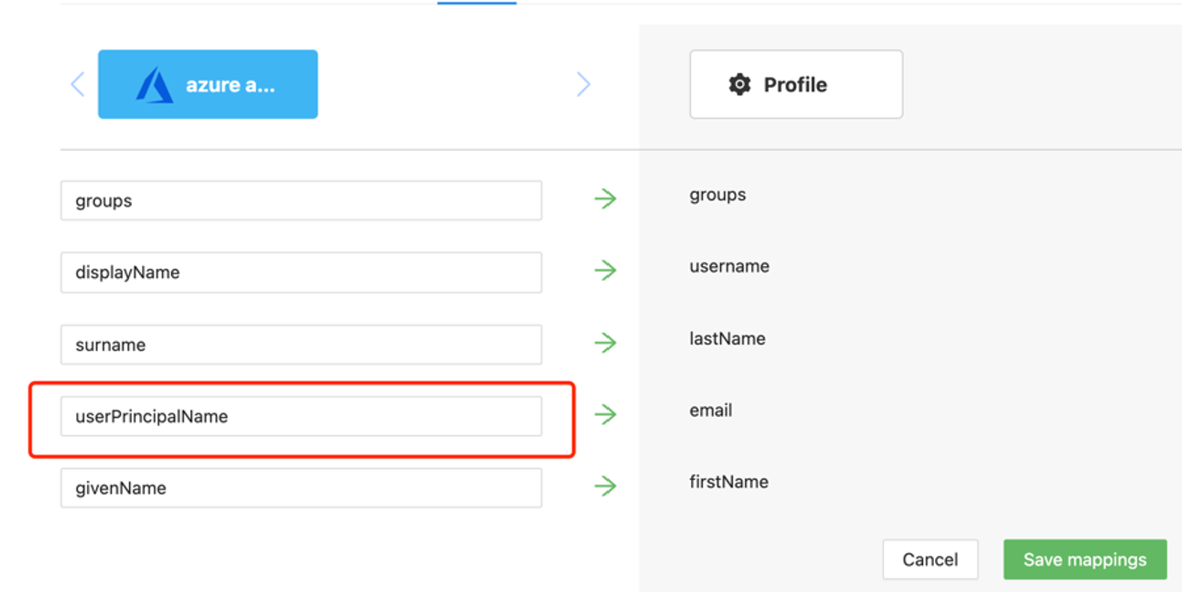
Note
This configuration uses Microsoft Entra user principal name as the sign-in username for Oracle PeopleSoft. To use another user identity, go to the Mappings tab.
SSL Configuration
Select the Advanced tab.
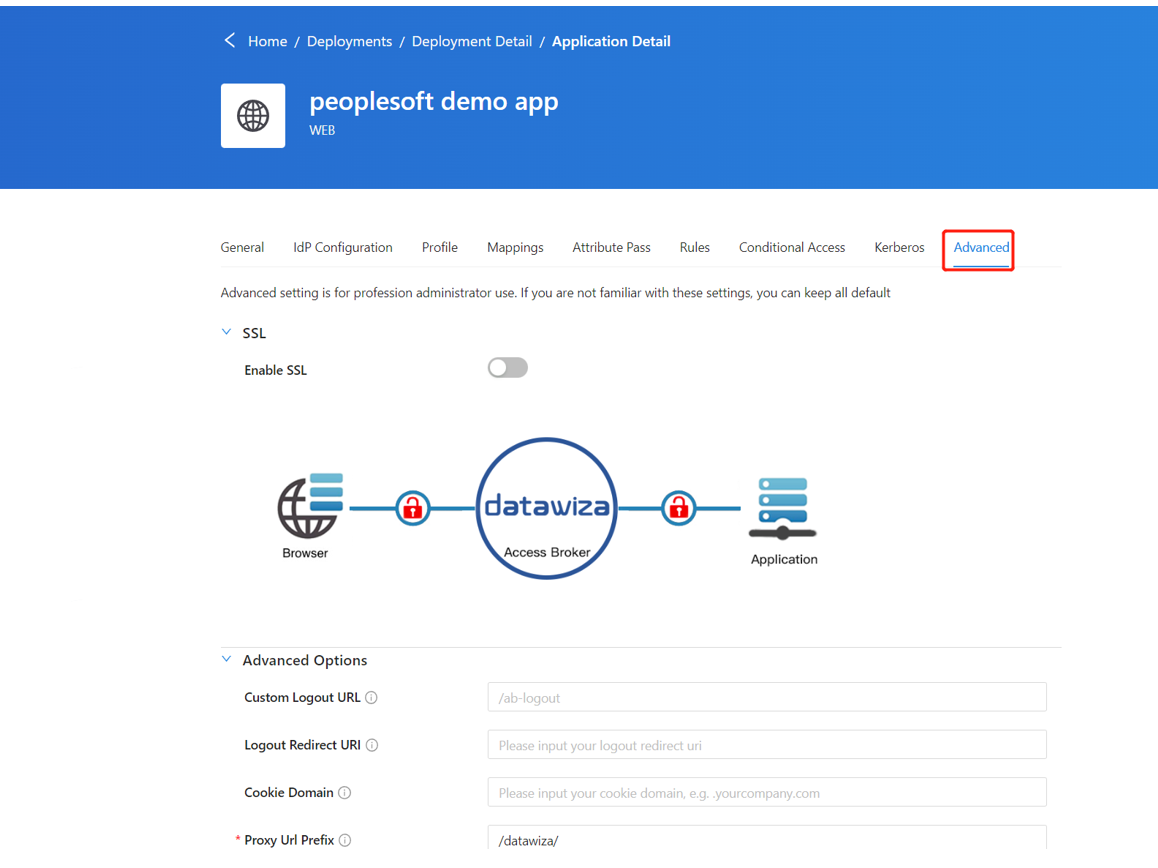
Select Enable SSL.
From the Cert Type dropdown, select a type.
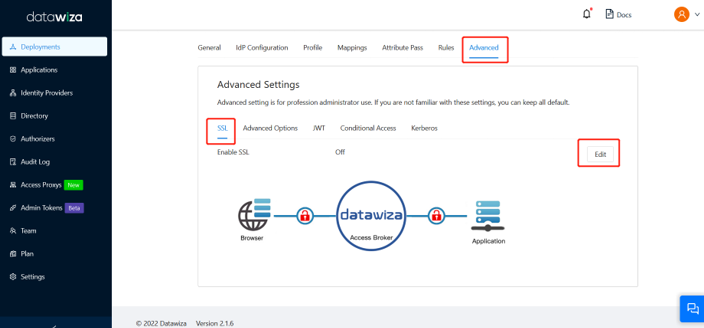
For testing the configuration, there's a self-signed certificate.
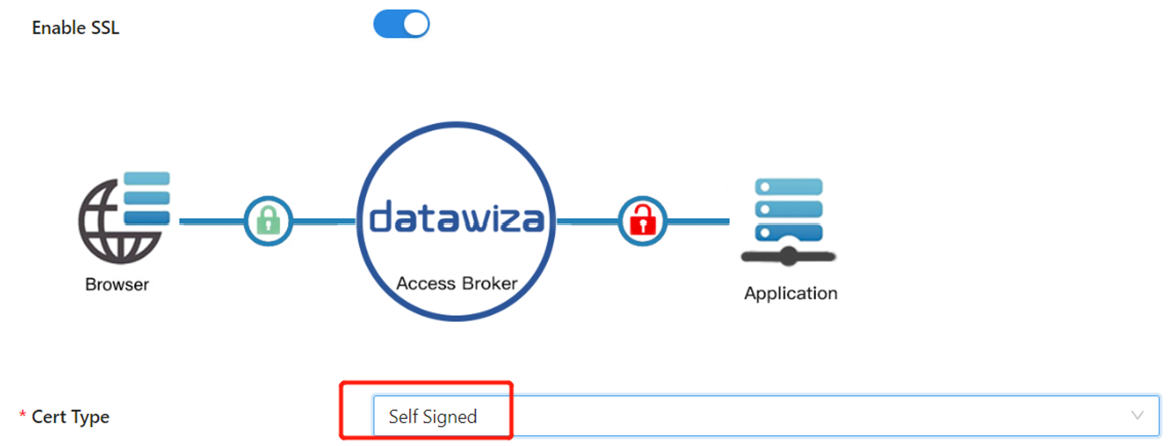
Note
You can upload a certificate from a file.
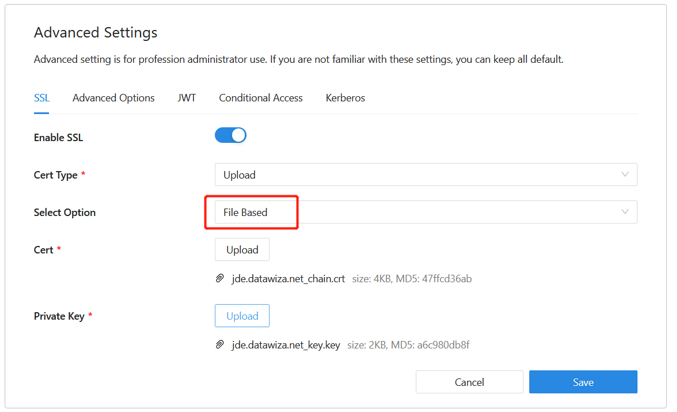
Select Save.
Enable Microsoft Entra multifactor authentication
Tip
Steps in this article might vary slightly based on the portal you start from.
To provide more security for sign-ins, you can enforce Microsoft Entra multifactor authentication.
Learn more: Tutorial: Secure user sign-in events with Microsoft Entra multifactor authentication
- Sign in to the Microsoft Entra admin center as a Global Administrator.
- Browse to Identity > Overview > Properties tab.
- Under Security defaults, select Manage security defaults.
- On the Security defaults pane, toggle the dropdown menu to select Enabled.
- Select Save.
Enable SSO in the Oracle PeopleSoft console
To enable SSO in the Oracle PeopleSoft environment:
Sign in to the PeopleSoft Console
http://{your-peoplesoft-fqdn}:8000/psp/ps/?cmd=startusing Admin credentials, for example, PS/PS.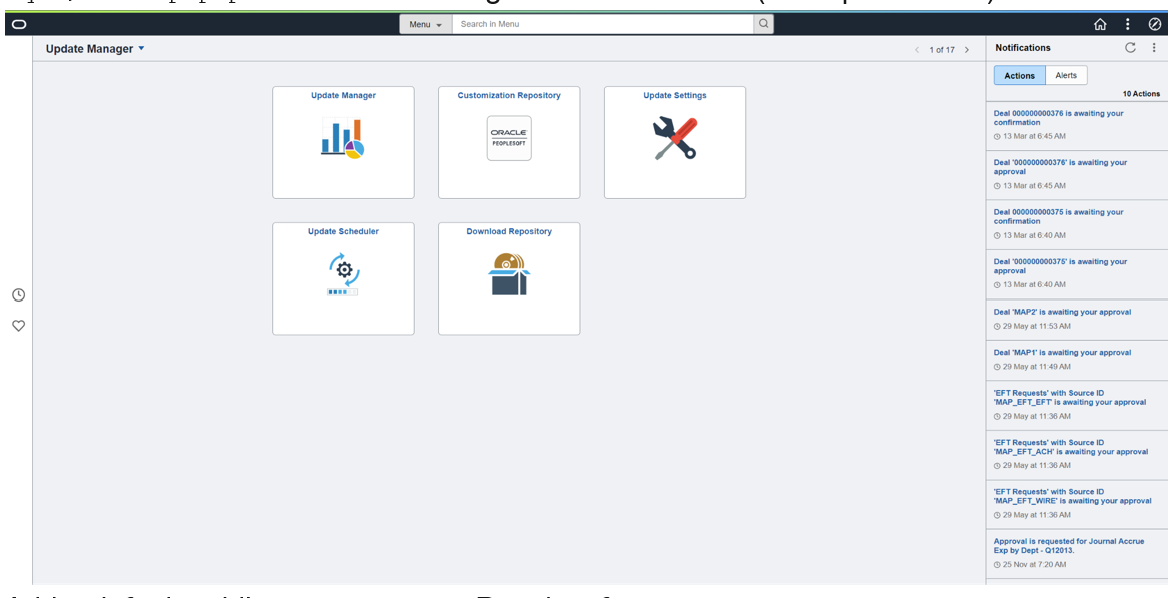
Add a default public access user to PeopleSoft.
From the main menu, navigate to PeopleTools > Security > User Profiles > User Profiles > Add a New Value.
Select Add a new value.
Create user PSPUBUSER.
Enter the password.
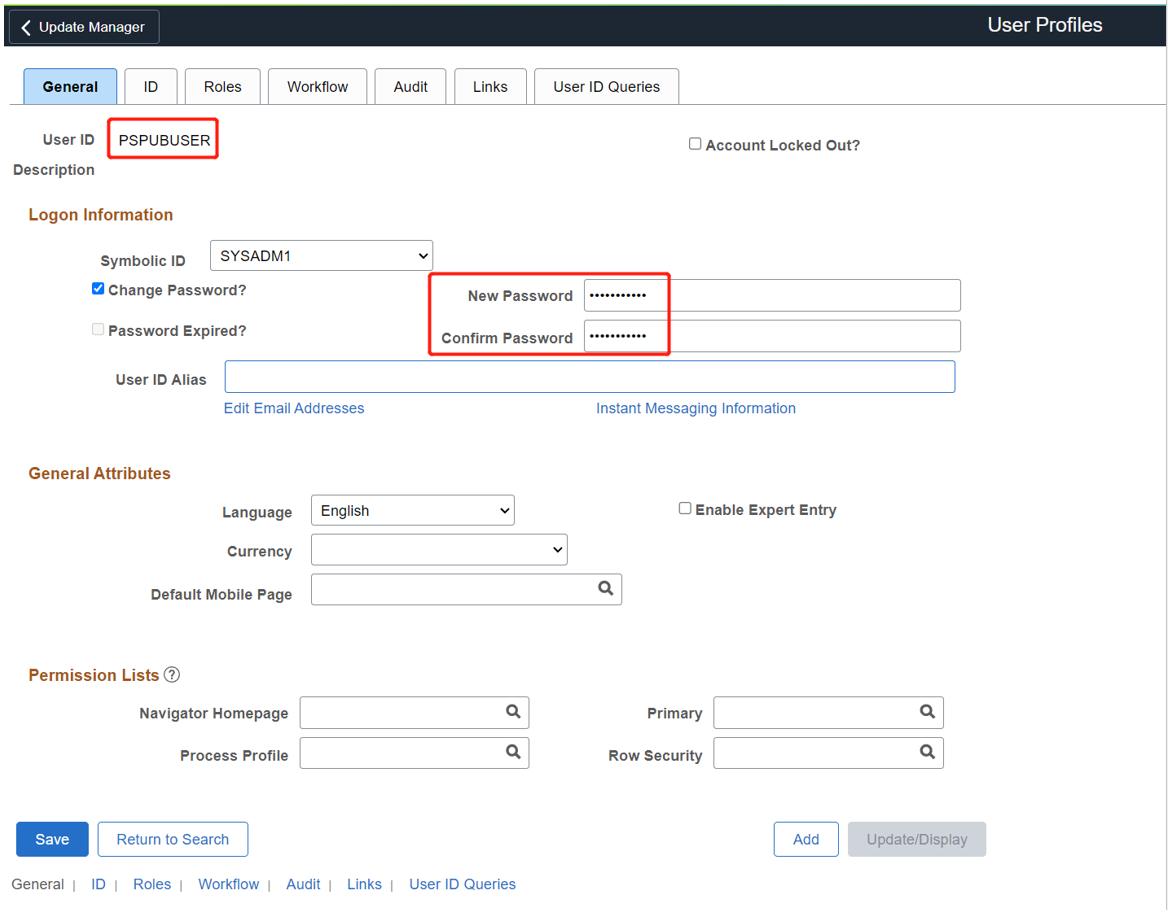
Select the ID tab.
For ID Type, select None.

Navigate to PeopleTools > Web Profile > Web Profile Configuration > Search > PROD > Security.
Under Public Users, select the Allow Public Access box.
For User ID, enter PSPUBUSER.
Enter the password.
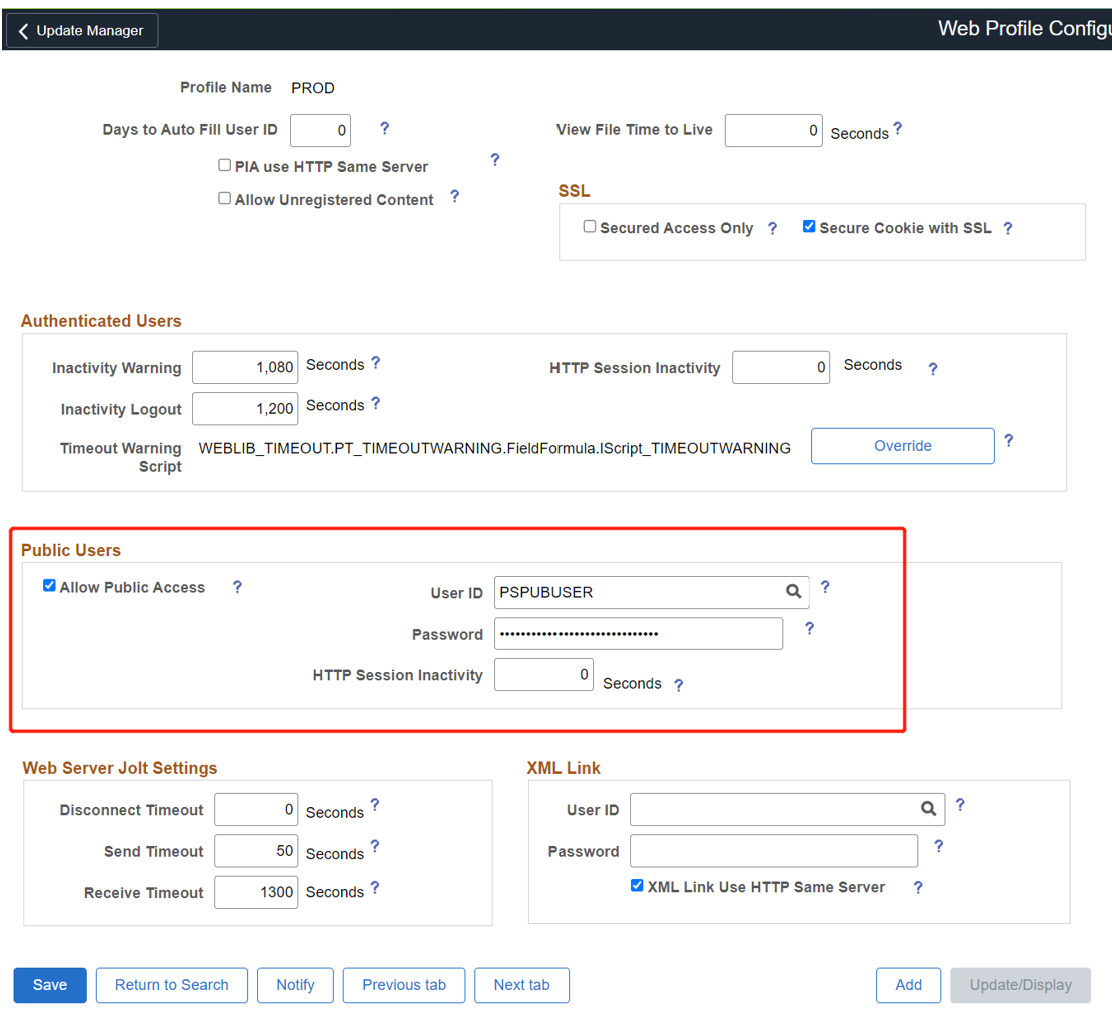
Select Save.
To enable SSO, navigate to PeopleTools > Security > Security Objects > Signon PeopleCode.
Select the Sign on PeopleCode page.
Enable OAMSSO_AUTHENTICATION.
Select Save.
To configure PeopleCode using the PeopleTools application designer, navigate to File > Open > Definition: Record > Name:
FUNCLIB_LDAP.Open FUNCLIB_LDAP.
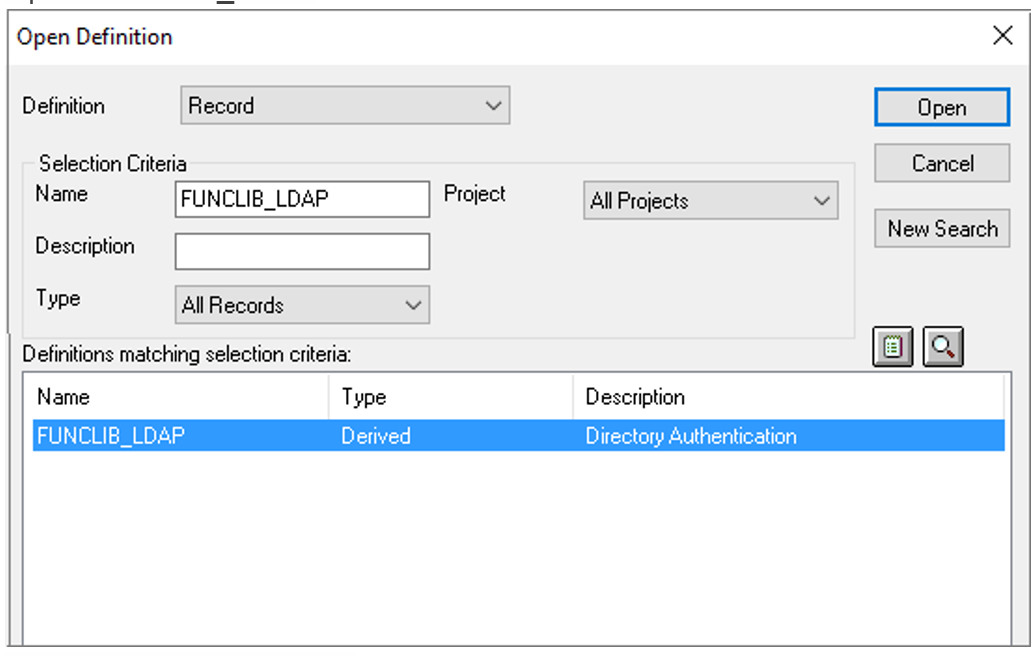
Select the record.
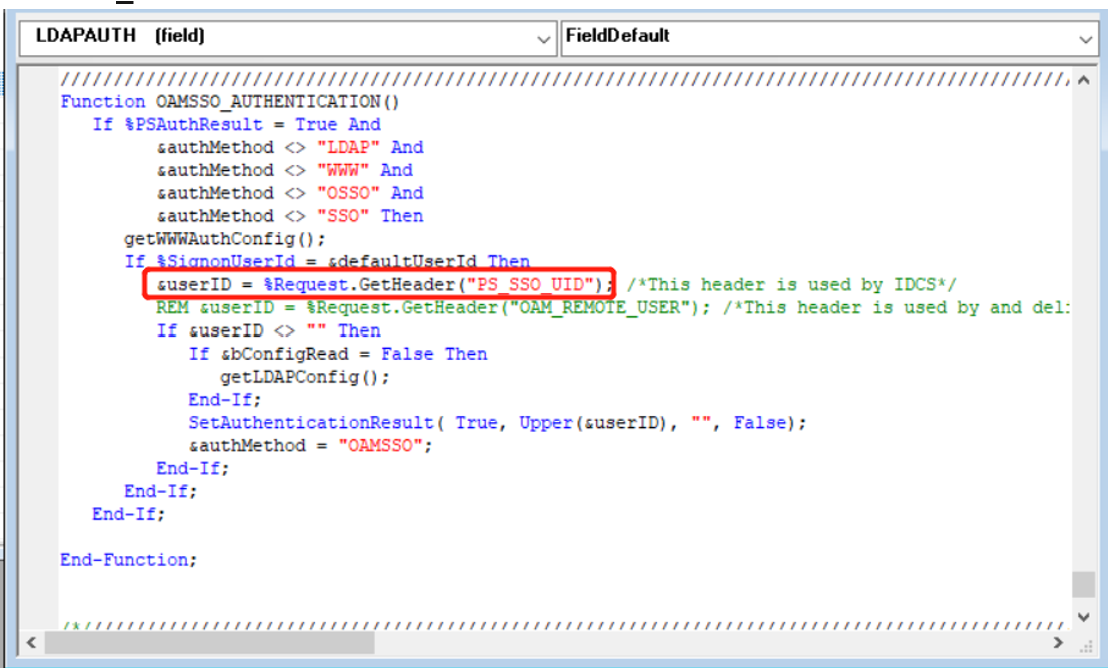
Select LDAPAUTH > View PeopleCode.
Search for the
getWWWAuthConfig()functionChange &defaultUserId = ""; to &defaultUserId = PSPUBUSER.Confirm the user Header is
PS_SSO_UIDforOAMSSO_AUTHENTICATIONfunction.Save the record definition.
Test an Oracle PeopleSoft application
To test an Oracle PeopleSoft application, validate application headers, policy, and overall testing. If needed, use header and policy simulation to validate header fields and policy execution.
To confirm Oracle PeopleSoft application access occurs correctly, a prompt appears to use a Microsoft Entra account for sign-in. Credentials are checked and the Oracle PeopleSoft appears.
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for