Events
Sep 16, 11 PM - Oct 18, 11 PM
Join us on a learning journey combining AI, apps and cloud-scale data to build unique solutions.
Learn moreThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
In some cases, you might have your Azure AKS cluster in one Microsoft Entra tenant and your Azure container registry in a different tenant. This article walks through the steps to enable cross-tenant authentication using the AKS service principal credential to pull from the container registry.
Note
You can't attach the registry and authenticate using an AKS managed identity when the cluster and the container registry are in different tenants.
Assumptions for this example:
You need at least the Contributor role in the AKS cluster's subscription and the Owner role in the container registry's subscription.
You use the following steps to:
Sign in to the Azure portal in Tenant A.
Search for and select Microsoft Entra ID.
Under Manage, select App registrations > + New registration.
In Supported account types, select Accounts in any organizational directory.
In Redirect URI, enter https://www.microsoft.com.
Select Register.
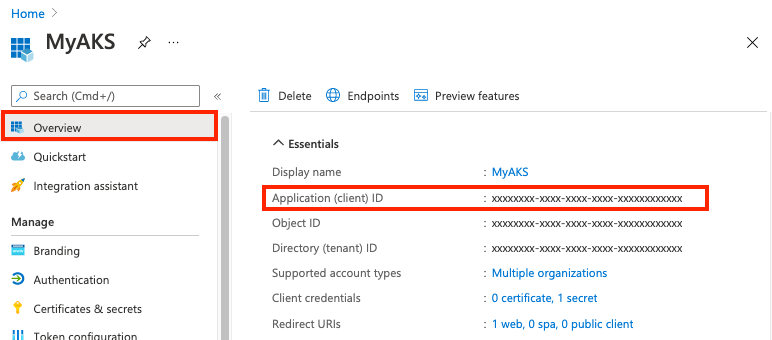
On the Overview page, take note of the Application (client) ID. It will be used in Step 2 and Step 4.
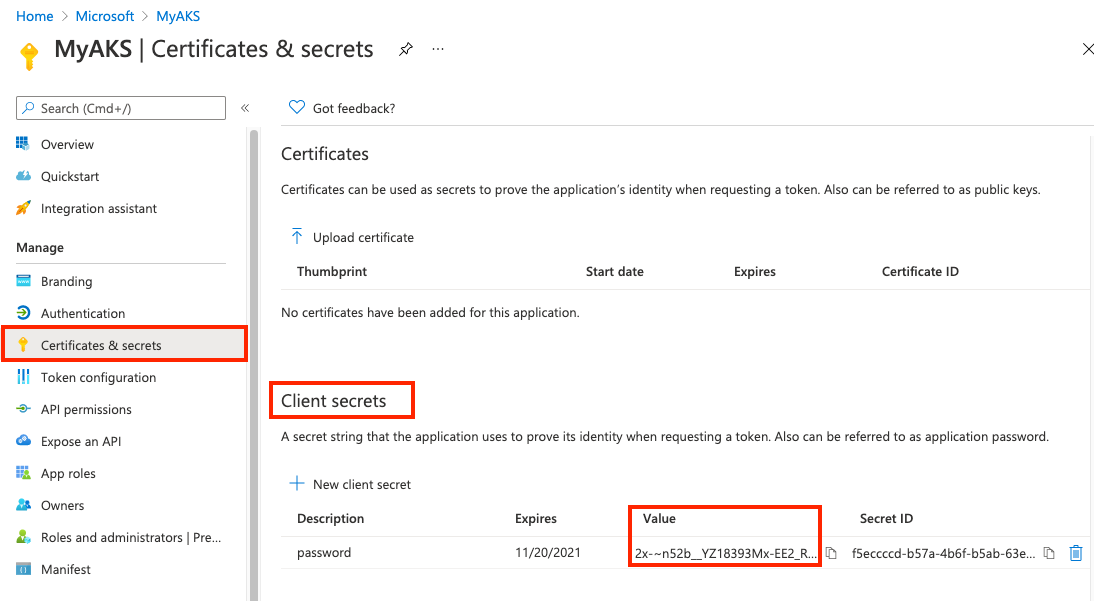
In Certificates & secrets, under Client secrets, select + New client secret.
Enter a Description such as Password and select Add.
In Client secrets, take note of the value of the client secret. You use it to update the AKS cluster's service principal in Step 4.
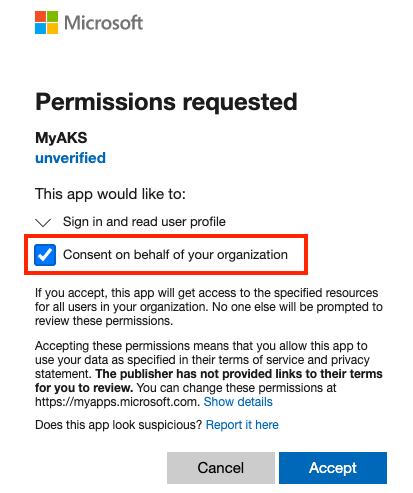
Open the following link using an admin account in Tenant B. Where indicated, insert the ID of Tenant B and the application ID (client ID) of the multitenant app.
https://login.microsoftonline.com/<Tenant B ID>/oauth2/authorize?client_id=<Multitenant application ID>&response_type=code&redirect_uri=<redirect url>
Select Consent on behalf of your organization and then Accept.
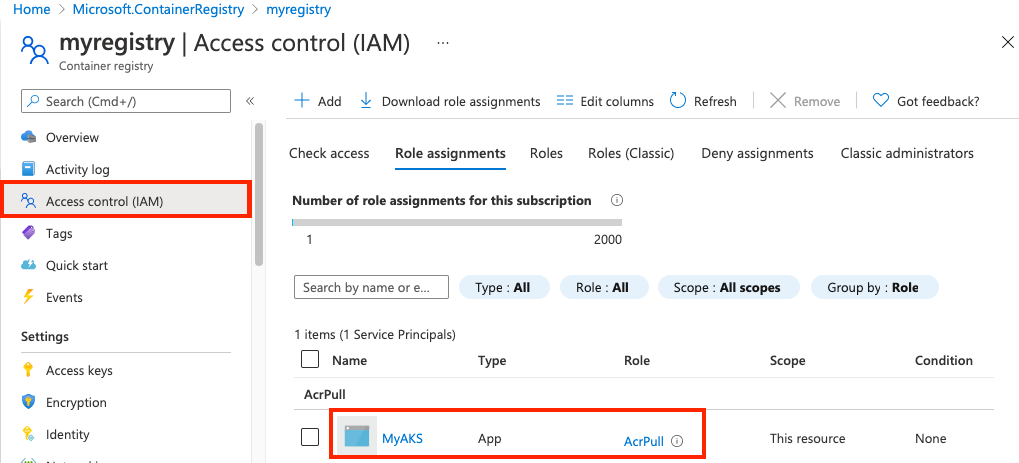
In Tenant B, assign the AcrPull role to the service principal, scoped to the target container registry. You can use the Azure portal or other tools to assign the role. For example steps using the Azure CLI, see Azure Container Registry authentication with service principals.
Use the multitenant application (client) ID and client secret collected in Step 1 to update the AKS service principal credential.
Updating the service principal can take several minutes.
Events
Sep 16, 11 PM - Oct 18, 11 PM
Join us on a learning journey combining AI, apps and cloud-scale data to build unique solutions.
Learn moreTraining
Module
Configure Azure Container Registry for container app deployments - Training
Learn how to create and configure an Azure Container Registry, the process of pushing container images to Azure Container Registry and explore different authentication methods and security features for Azure Container Registry.
Certification
Microsoft Certified: Identity and Access Administrator Associate - Certifications
Demonstrate the features of Microsoft Entra ID to modernize identity solutions, implement hybrid solutions, and implement identity governance.