Deploy linked ARM templates with VSTS
APPLIES TO:  Azure Data Factory
Azure Data Factory  Azure Synapse Analytics
Azure Synapse Analytics
Tip
Try out Data Factory in Microsoft Fabric, an all-in-one analytics solution for enterprises. Microsoft Fabric covers everything from data movement to data science, real-time analytics, business intelligence, and reporting. Learn how to start a new trial for free!
This article describes how to deploy linked Azure Resource Manager (ARM) templates with Azure DevOps Services (formerly Visual Studio Team Services, or VSTS).
Overview
When dealing with deploying many components in Azure, a single ARM template might be challenging to manage and maintain. ARM linked templates allow you to make your deployment more modular and makes the templates easier to manage. When dealing with large deployments, it's highly recommended to consider breaking down your deployment into a main template and multiple linked templates representing different components of your deployment.
Deploying ARM templates can be performed using several different methods such as using PowerShell, Azure CLI, and Azure portal. A recommended approach however is to adopt one of DevOps practices, namely continuous deployment. VSTS is an application lifecycle management tool hosted in the cloud and offered as a service. One of the capabilities VSTS offers is release management.
This article describes how you can deploy linked ARM templates using the release management feature of VSTS. In order for the linked templates to be deployed properly, they need to be stored in a location that can be reached by the Azure Resource Manager, such as Azure Storage; so we show how Azure Storage can be used to stage the ARM template files. We will also show some recommended practices around keeping secrets protected using Azure Key Vault.
The scenario we walk through here's to deploy VNet with a Network Security Group (NSG) structured as linked templates. We use VSTS to show how continuous deployment can be set up to enable teams to continuously update Azure with new changes each time there's a modification to the template.
Create an Azure Storage account
Sign in to the Azure portal and create an Azure Storage account following the steps documented here.
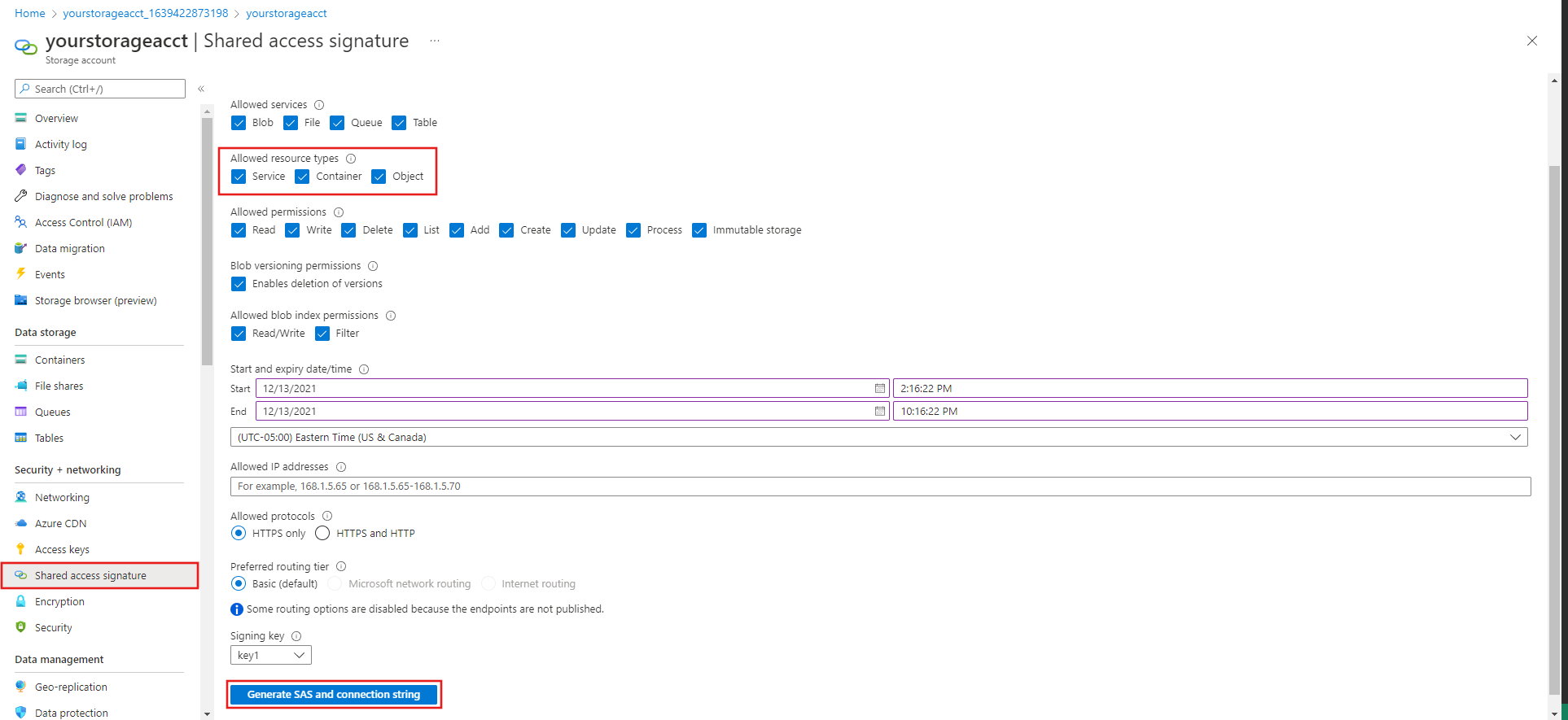
Once deployment is complete, navigate to the storage account and select Shared access signature. Select Service, Container, and Object for the Allowed resource types. Then select Generate SAS and connection string. Copy the SAS token and keep it available since we use it later.
Select the storage account Containers page and create a new Container.
Select the new Container properties.
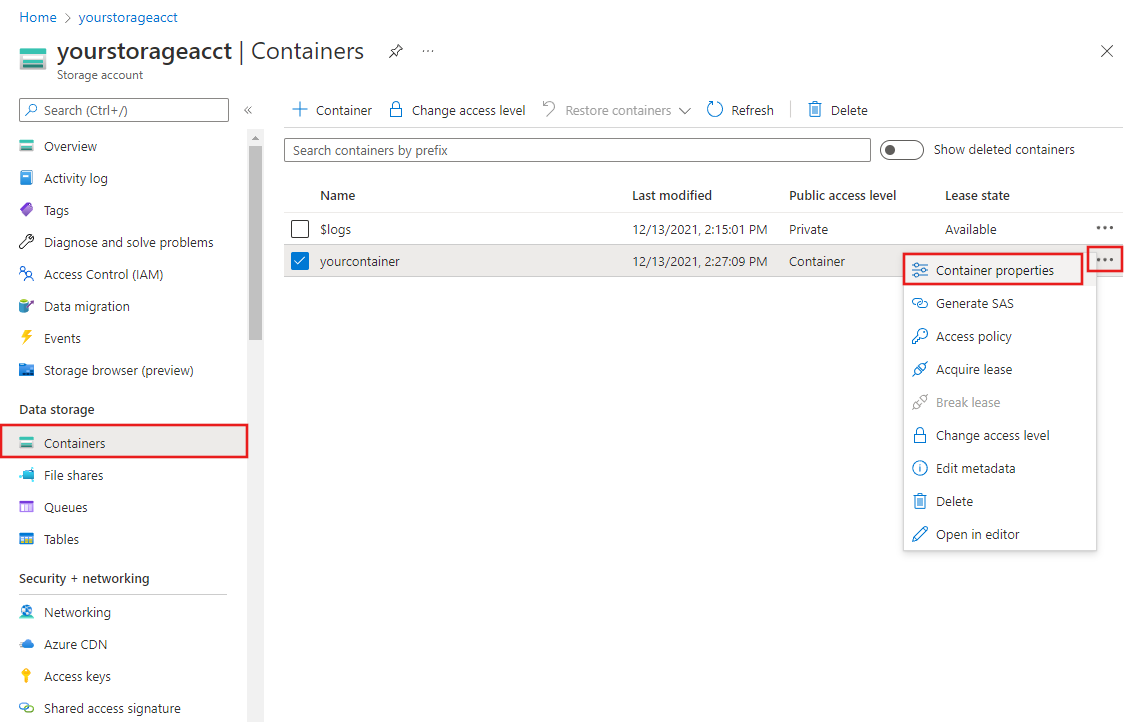
Copy the URL field and keep it handy. We need it later along with the SAS token from the earlier step.
Protect secrets with Azure Key Vault
- In the Azure portal, create an Azure Key Vault resource.
- Select the Azure Key Vault you created in the earlier step and then select Secrets.
- Select Generate/Import to add the SAS Token.
- For the Name property, enter
StorageSASTokenand then provide the Azure Storage shared access signature key you copied in a previous step for the Value. - Select Create.
Link Azure Key Vault to VSTS
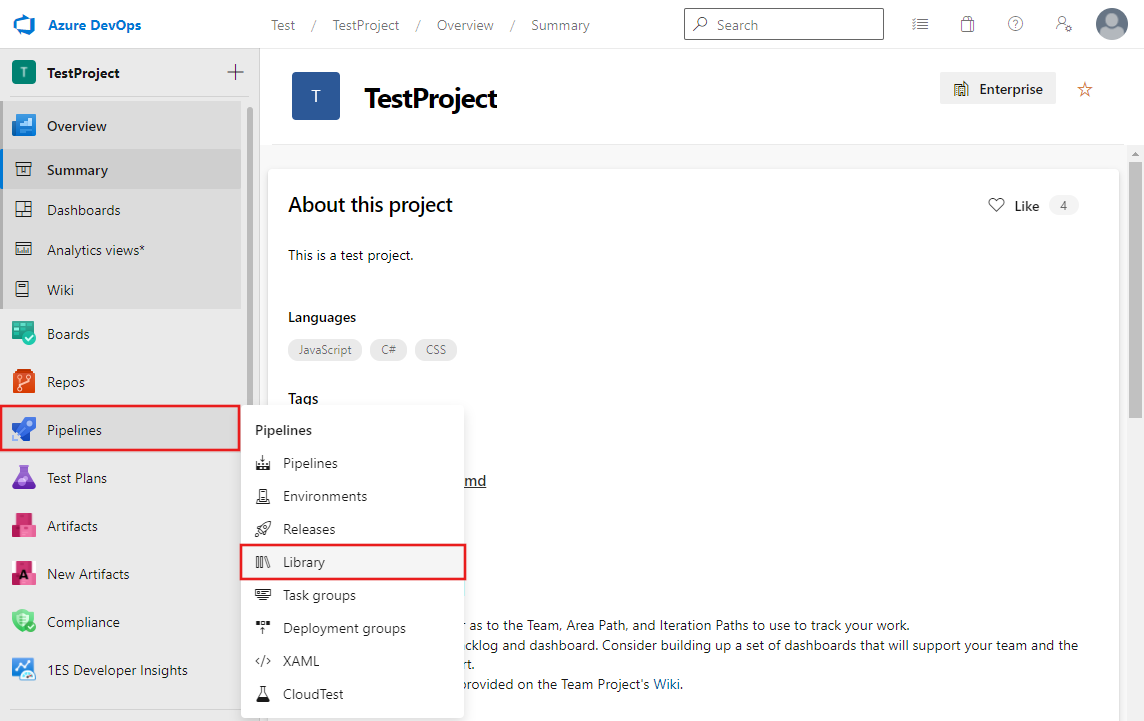
Sign in to your Azure DevOps organization and navigate to your project.
Go to Library under Pipelines in the navigation pane.
Under Variable group, create a new group and for Variable group name enter
AzureKeyVaultSecrets.Toggle Link secrets from an Azure key vault as variables.
Select your Azure subscription and then the Azure Key Vault you created earlier, and then select Authorize.
Once authorization is successful, you can add variables by clicking Add and are presented with the option to add references to the secrets in the Azure Key Vault. Add a reference to the
StorageSASTokencreated in the earlier step, and save it.
Setup continuous deployment using VSTS
Follow steps listed in the article Automate continuous integration using Azure Pipelines releases.
A few changes are required from the above steps in order to use a linked ARM template deployment:
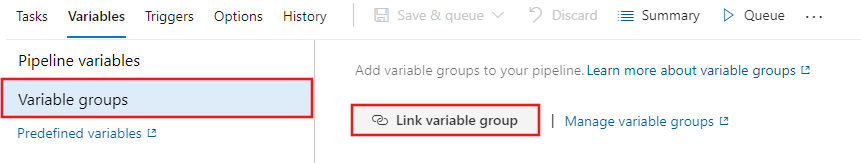
Under the release, link the variable group created earlier:
Linked ARM template:
- For Template, point to ArmTemplate_master.json instead of ArmTemplateForFactory.json
- For Template Parameters, point to 'ArmTemplateParameters_master.json' instead of 'ArmTemplateParametersForFactory.json'
Under override Template parameters update two more parameters
- containerUri - Paste the URL of container created in the earlier step.
- containerSasToken - If the secret's name is 'StorageSASToken', enter '$(StorageSASToken)' for this value.
Save the release pipeline and trigger a release.
Related content
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for