Deny Public Network Access in Azure Database for MySQL using Azure portal
APPLIES TO:  Azure Database for MySQL - Single Server
Azure Database for MySQL - Single Server
Important
Azure Database for MySQL single server is on the retirement path. We strongly recommend that you upgrade to Azure Database for MySQL flexible server. For more information about migrating to Azure Database for MySQL flexible server, see What's happening to Azure Database for MySQL Single Server?
This article describes how you can configure an Azure Database for MySQL server to deny all public configurations and allow only connections through private endpoints to further enhance the network security.
Prerequisites
To complete this how-to guide, you need:
- An Azure Database for MySQL with General Purpose or Memory Optimized pricing tier
Set Deny Public Network Access
Follow these steps to set MySQL server Deny Public Network Access:
In the Azure portal, select your existing Azure Database for MySQL server.
On the MySQL server page, under Settings, click Connection security to open the connection security configuration page.
In Deny Public Network Access, select Yes to enable deny public access for your MySQL server.
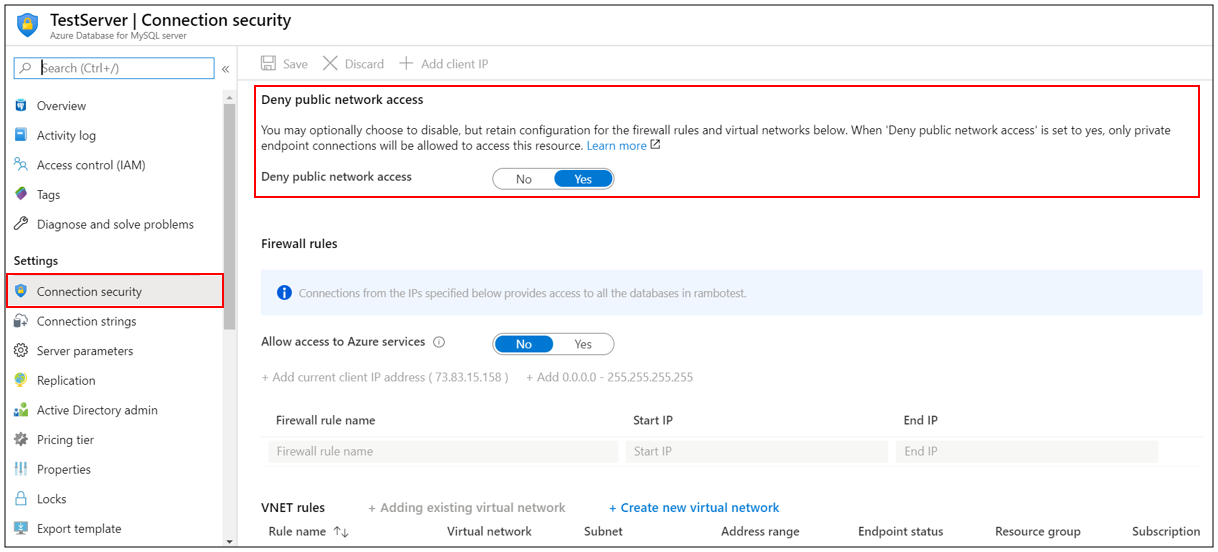
Click Save to save the changes.
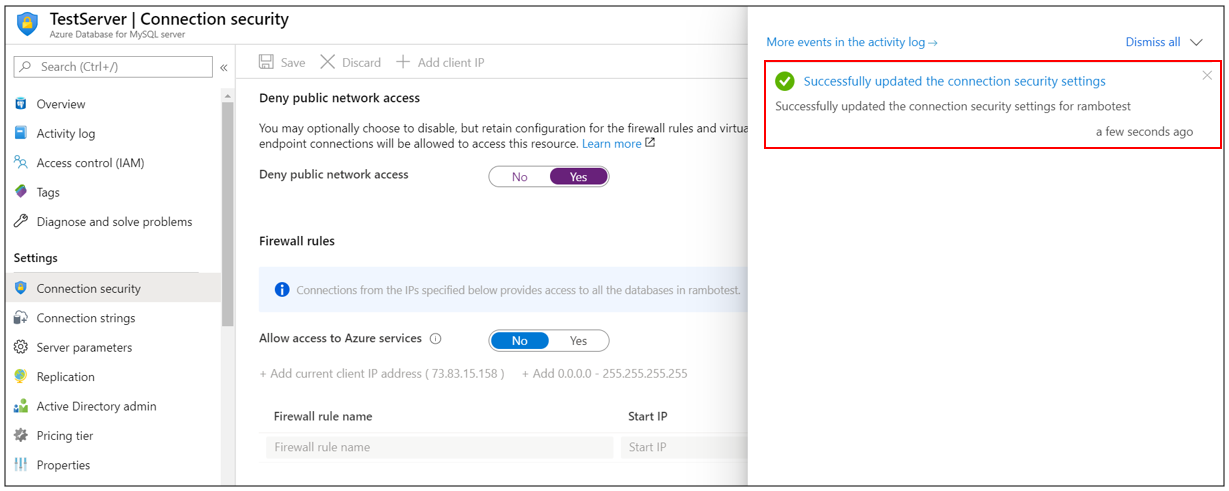
A notification will confirm that connection security setting was successfully enabled.
Next steps
Learn about how to create alerts on metrics.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for