Indexer connections to Azure SQL Managed Instance through a public endpoint
Indexers in Azure AI Search connect to external data sources over a public endpoint. If you're setting up an Azure SQL indexer for a connection to a SQL managed instance, follow the steps in this article to ensure the public endpoint is set up correctly.
Alternatively, if the managed instance is behind a firewall, create a shared private link instead.
Note
Always Encrypted columns are not currently supported by Azure AI Search indexers.
Enable a public endpoint
This article highlights just the steps for an indexer connection in Azure AI Search. If you want more background, see Configure public endpoint in Azure SQL Managed Instance instead.
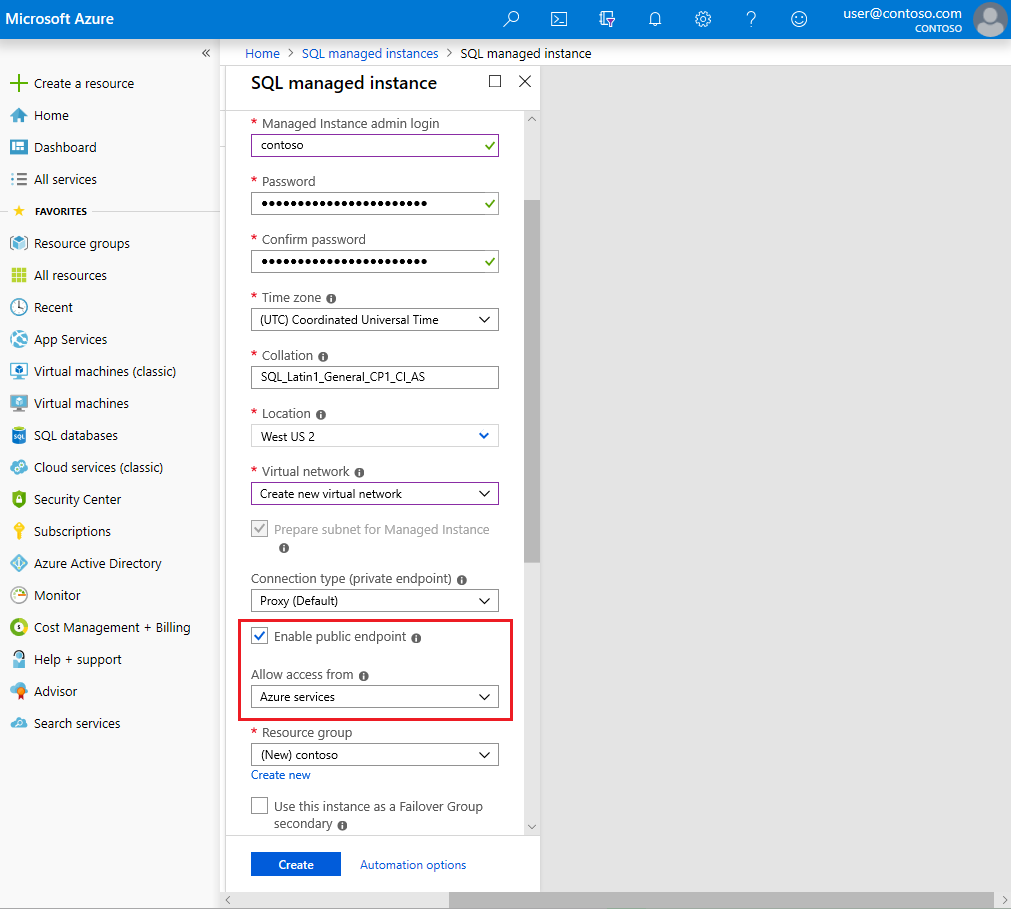
For a new SQL Managed Instance, create the resource with the Enable public endpoint option selected.
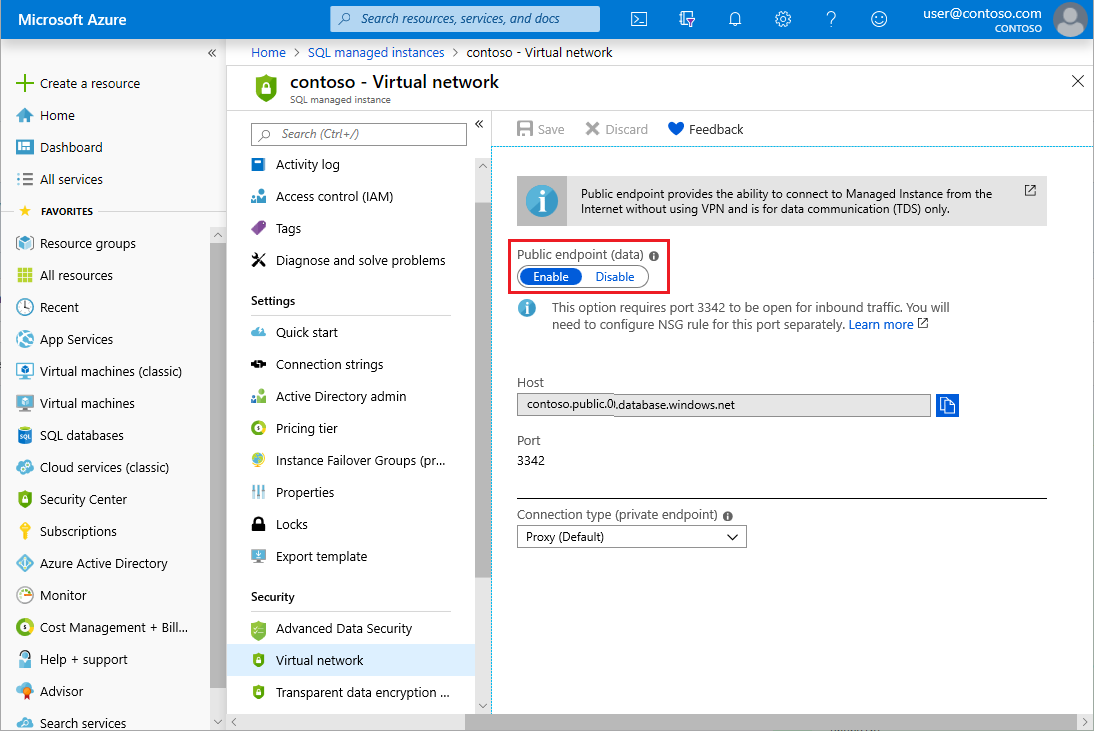
Alternatively, if the instance already exists, you can enable public endpoint on an existing SQL Managed Instance under Security > Virtual network > Public endpoint > Enable.
Verify NSG rules
Check the Network Security Group has the correct Inbound security rules that allow connections from Azure services.
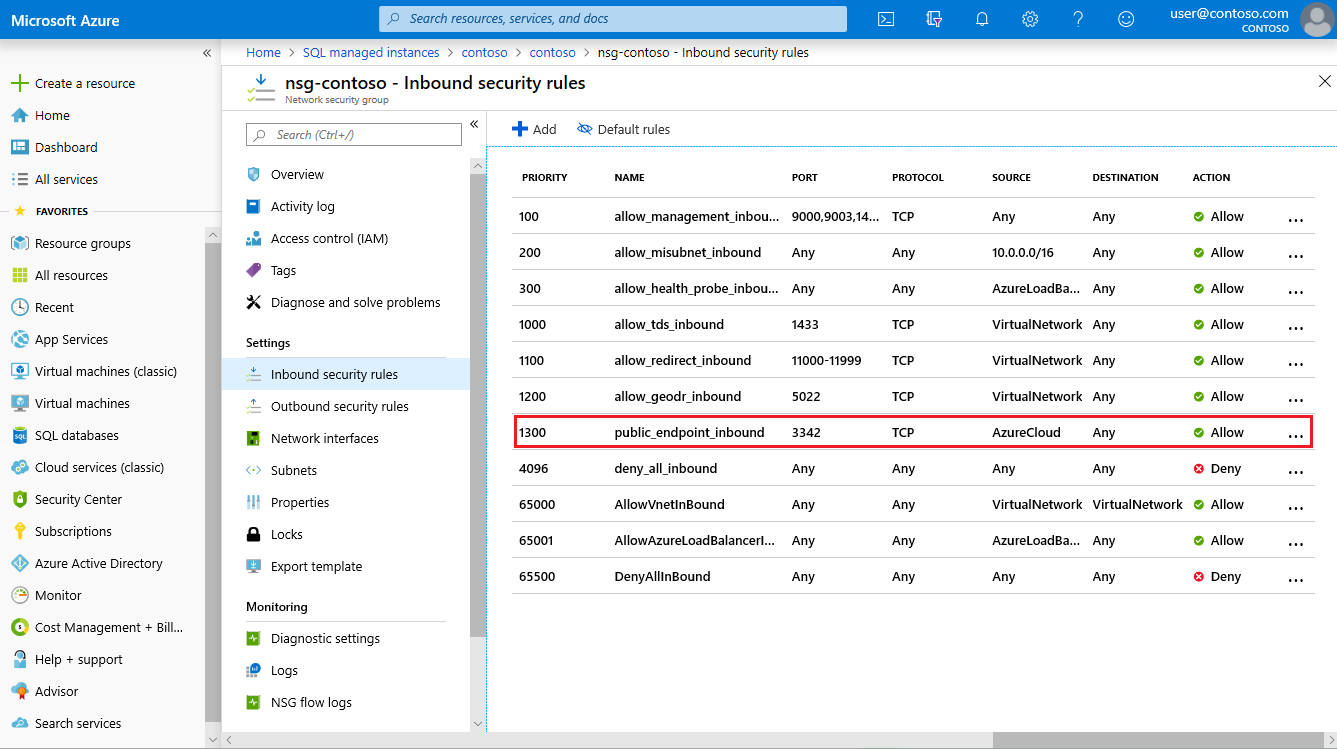
Restrict inbound access to the endpoint
You can restrict inbound access to the public endpoint by replacing the current rule (public_endpoint_inbound) with the following two rules:
Allowing inbound access from the
AzureCognitiveSearchservice tag ("SOURCE" =AzureCognitiveSearch, "NAME" =cognitive_search_inbound)Allowing inbound access from the IP address of the search service, which can be obtained by pinging its fully qualified domain name (for example,
<your-search-service-name>.search.windows.net). ("SOURCE" =IP address, "NAME" =search_service_inbound)
For each rule, set "PORT" = 3342, "PROTOCOL" = TCP, "DESTINATION" = Any, "ACTION" = Allow.
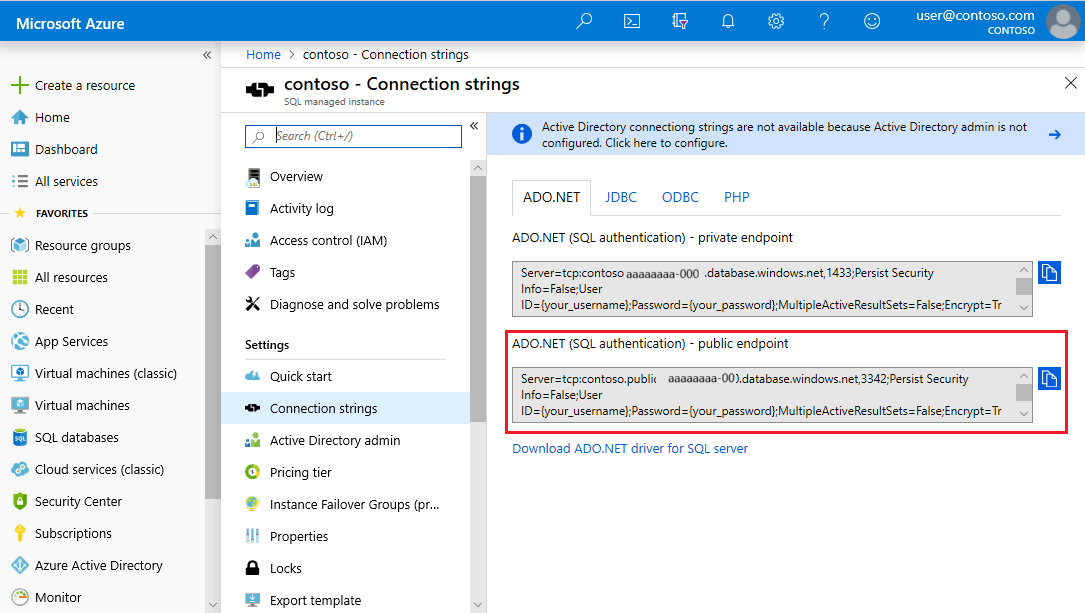
Get public endpoint connection string
Copy the connection string to use in the search indexer's data source connection. Be sure to copy the connection string for the public endpoint (port 3342, not port 1433).
Next steps
With configuration out of the way, you can now specify a SQL managed instance as an indexer data source using the basic instructions for setting up an Azure SQL indexer.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for