Quickstart: Use Azure PowerShell to create a virtual network
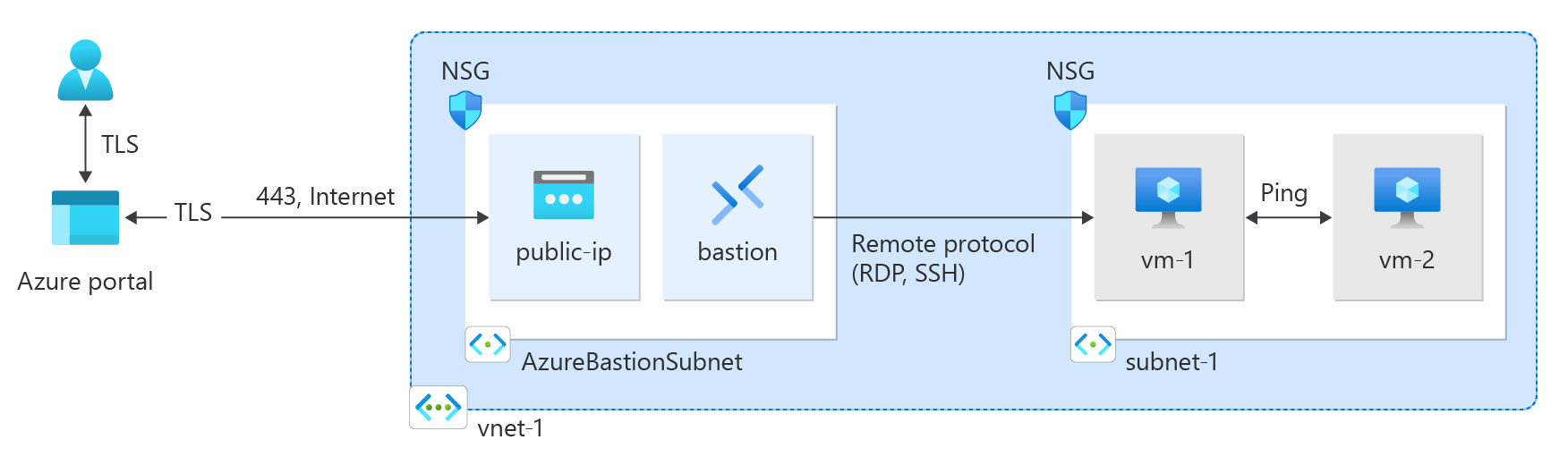
This quickstart shows you how to create a virtual network by using Azure PowerShell. You then create two virtual machines (VMs) in the network, securely connect to the VMs from the internet, and start private communication between the VMs.
A virtual network is the fundamental building block for private networks in Azure. Azure Virtual Network enables Azure resources like VMs to securely communicate with each other and the internet.
Prerequisites
An Azure account with an active subscription. You can create an account for free.
Azure Cloud Shell or Azure PowerShell.
The steps in this quickstart run the Azure PowerShell cmdlets interactively in Azure Cloud Shell. To run the commands in the Cloud Shell, select Open Cloudshell at the upper-right corner of a code block. Select Copy to copy the code, and then paste it into Cloud Shell to run it. You can also run Cloud Shell from within the Azure portal.
You can also install Azure PowerShell locally to run the cmdlets. The steps in this article require Azure PowerShell module version 5.4.1 or later. Run
Get-Module -ListAvailable Azto find your installed version. If you need to upgrade, see Update the Azure PowerShell module.If you run PowerShell locally, run
Connect-AzAccountto connect to Azure.
Create a resource group
Use New-AzResourceGroup to create a resource group to host the virtual network. Run the following code to create a resource group named test-rg in the eastus2 Azure region:
$rg = @{
Name = 'test-rg'
Location = 'eastus2'
}
New-AzResourceGroup @rg
Create a virtual network
Use New-AzVirtualNetwork to create a virtual network named vnet-1 with IP address prefix 10.0.0.0/16 in the test-rg resource group and eastus2 location:
$vnet = @{ Name = 'vnet-1' ResourceGroupName = 'test-rg' Location = 'eastus2' AddressPrefix = '10.0.0.0/16' } $virtualNetwork = New-AzVirtualNetwork @vnetAzure deploys resources to a subnet within a virtual network. Use Add-AzVirtualNetworkSubnetConfig to create a subnet configuration named subnet-1 with address prefix 10.0.0.0/24:
$subnet = @{ Name = 'subnet-1' VirtualNetwork = $virtualNetwork AddressPrefix = '10.0.0.0/24' } $subnetConfig = Add-AzVirtualNetworkSubnetConfig @subnetAssociate the subnet configuration to the virtual network by using Set-AzVirtualNetwork:
$virtualNetwork | Set-AzVirtualNetwork
Deploy Azure Bastion
Azure Bastion uses your browser to connect to VMs in your virtual network over Secure Shell (SSH) or Remote Desktop Protocol (RDP) by using their private IP addresses. The VMs don't need public IP addresses, client software, or special configuration. For more information about Bastion, see What is Azure Bastion?.
Hourly pricing starts from the moment that Bastion is deployed, regardless of outbound data usage. For more information, see Pricing and SKUs. If you're deploying Bastion as part of a tutorial or test, we recommend that you delete this resource after you finish using it.
Configure a Bastion subnet for your virtual network. This subnet is reserved exclusively for Bastion resources and must be named AzureBastionSubnet.
$subnet = @{ Name = 'AzureBastionSubnet' VirtualNetwork = $virtualNetwork AddressPrefix = '10.0.1.0/26' } $subnetConfig = Add-AzVirtualNetworkSubnetConfig @subnetSet the configuration:
$virtualNetwork | Set-AzVirtualNetworkCreate a public IP address for Bastion. The Bastion host uses the public IP to access SSH and RDP over port 443.
$ip = @{ ResourceGroupName = 'test-rg' Name = 'public-ip' Location = 'eastus2' AllocationMethod = 'Static' Sku = 'Standard' Zone = 1,2,3 } New-AzPublicIpAddress @ipUse the New-AzBastion command to create a new Standard SKU Bastion host in AzureBastionSubnet:
$bastion = @{ Name = 'bastion' ResourceGroupName = 'test-rg' PublicIpAddressRgName = 'test-rg' PublicIpAddressName = 'public-ip' VirtualNetworkRgName = 'test-rg' VirtualNetworkName = 'vnet-1' Sku = 'Basic' } New-AzBastion @bastion
It takes about 10 minutes to deploy the Bastion resources. You can create VMs in the next section while Bastion deploys to your virtual network.
Create virtual machines
Use New-AzVM to create two VMs named vm-1 and vm-2 in the subnet-1 subnet of the virtual network. When you're prompted for credentials, enter usernames and passwords for the VMs.
To create the first VM, use the following code:
# Set the administrator and password for the VM. ## $cred = Get-Credential ## Place the virtual network into a variable. ## $vnet = Get-AzVirtualNetwork -Name 'vnet-1' -ResourceGroupName 'test-rg' ## Create a network interface for the VM. ## $nic = @{ Name = "nic-1" ResourceGroupName = 'test-rg' Location = 'eastus2' Subnet = $vnet.Subnets[0] } $nicVM = New-AzNetworkInterface @nic ## Create a virtual machine configuration. ## $vmsz = @{ VMName = "vm-1" VMSize = 'Standard_DS1_v2' } $vmos = @{ ComputerName = "vm-1" Credential = $cred } $vmimage = @{ PublisherName = 'Canonical' Offer = '0001-com-ubuntu-server-jammy' Skus = '22_04-lts-gen2' Version = 'latest' } $vmConfig = New-AzVMConfig @vmsz ` | Set-AzVMOperatingSystem @vmos -Linux ` | Set-AzVMSourceImage @vmimage ` | Add-AzVMNetworkInterface -Id $nicVM.Id ## Create the VM. ## $vm = @{ ResourceGroupName = 'test-rg' Location = 'eastus2' VM = $vmConfig } New-AzVM @vmTo create the second VM, use the following code:
# Set the administrator and password for the VM. ## $cred = Get-Credential ## Place the virtual network into a variable. ## $vnet = Get-AzVirtualNetwork -Name 'vnet-1' -ResourceGroupName 'test-rg' ## Create a network interface for the VM. ## $nic = @{ Name = "nic-2" ResourceGroupName = 'test-rg' Location = 'eastus2' Subnet = $vnet.Subnets[0] } $nicVM = New-AzNetworkInterface @nic ## Create a virtual machine configuration. ## $vmsz = @{ VMName = "vm-2" VMSize = 'Standard_DS1_v2' } $vmos = @{ ComputerName = "vm-2" Credential = $cred } $vmimage = @{ PublisherName = 'Canonical' Offer = '0001-com-ubuntu-server-jammy' Skus = '22_04-lts-gen2' Version = 'latest' } $vmConfig = New-AzVMConfig @vmsz ` | Set-AzVMOperatingSystem @vmos -Linux ` | Set-AzVMSourceImage @vmimage ` | Add-AzVMNetworkInterface -Id $nicVM.Id ## Create the VM. ## $vm = @{ ResourceGroupName = 'test-rg' Location = 'eastus2' VM = $vmConfig } New-AzVM @vm
Tip
You can use the -AsJob option to create a VM in the background while you continue with other tasks. For example, run New-AzVM @vm1 -AsJob. When Azure starts creating the VM in the background, you get something like the following output:
Id Name PSJobTypeName State HasMoreData Location Command
-- ---- ------------- ----- ----------- -------- -------
1 Long Running... AzureLongRun... Running True localhost New-AzVM
Azure takes a few minutes to create the VMs. When Azure finishes creating the VMs, it returns output to PowerShell.
Note
VMs in a virtual network with a Bastion host don't need public IP addresses. Bastion provides the public IP, and the VMs use private IPs to communicate within the network. You can remove the public IPs from any VMs in Bastion-hosted virtual networks. For more information, see Dissociate a public IP address from an Azure VM.
Note
Azure provides a default outbound access IP for VMs that either aren't assigned a public IP address or are in the backend pool of an internal basic Azure load balancer. The default outbound access IP mechanism provides an outbound IP address that isn't configurable.
The default outbound access IP is disabled when one of the following events happens:
- A public IP address is assigned to the VM.
- The VM is placed in the backend pool of a standard load balancer, with or without outbound rules.
- An Azure NAT Gateway resource is assigned to the subnet of the VM.
VMs that you create by using virtual machine scale sets in flexible orchestration mode don't have default outbound access.
For more information about outbound connections in Azure, see Default outbound access in Azure and Use Source Network Address Translation (SNAT) for outbound connections.
Connect to a virtual machine
In the portal, search for and select Virtual machines.
On the Virtual machines page, select vm-1.
In the Overview information for vm-1, select Connect.
On the Connect to virtual machine page, select the Bastion tab.
Select Use Bastion.
Enter the username and password that you created when you created the VM, and then select Connect.
Start communication between VMs
At the bash prompt for vm-1, enter
ping -c 4 vm-2.You get a reply similar to the following message:
azureuser@vm-1:~$ ping -c 4 vm-2 PING vm-2.3bnkevn3313ujpr5l1kqop4n4d.cx.internal.cloudapp.net (10.0.0.5) 56(84) bytes of data. 64 bytes from vm-2.internal.cloudapp.net (10.0.0.5): icmp_seq=1 ttl=64 time=1.83 ms 64 bytes from vm-2.internal.cloudapp.net (10.0.0.5): icmp_seq=2 ttl=64 time=0.987 ms 64 bytes from vm-2.internal.cloudapp.net (10.0.0.5): icmp_seq=3 ttl=64 time=0.864 ms 64 bytes from vm-2.internal.cloudapp.net (10.0.0.5): icmp_seq=4 ttl=64 time=0.890 msClose the Bastion connection to vm-1.
Repeat the steps in Connect to a virtual machine to connect to vm-2.
At the bash prompt for vm-2, enter
ping -c 4 vm-1.You get a reply similar to the following message:
azureuser@vm-2:~$ ping -c 4 vm-1 PING vm-1.3bnkevn3313ujpr5l1kqop4n4d.cx.internal.cloudapp.net (10.0.0.4) 56(84) bytes of data. 64 bytes from vm-1.internal.cloudapp.net (10.0.0.4): icmp_seq=1 ttl=64 time=0.695 ms 64 bytes from vm-1.internal.cloudapp.net (10.0.0.4): icmp_seq=2 ttl=64 time=0.896 ms 64 bytes from vm-1.internal.cloudapp.net (10.0.0.4): icmp_seq=3 ttl=64 time=3.43 ms 64 bytes from vm-1.internal.cloudapp.net (10.0.0.4): icmp_seq=4 ttl=64 time=0.780 msClose the Bastion connection to vm-2.
Clean up resources
When you finish with the virtual network and the VMs, use Remove-AzResourceGroup to remove the resource group and all its resources:
Remove-AzResourceGroup -Name 'test-rg' -Force
Next steps
In this quickstart, you created a virtual network with a default subnet that contains two VMs. You deployed Azure Bastion and used it to connect to the VMs, and securely communicated between the VMs. To learn more about virtual network settings, see Create, change, or delete a virtual network.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for