Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender XDR
Want to experience Defender for Endpoint? Sign up for a free trial.
Defender for Endpoint notifies you of possible malicious events, attributes, and contextual information through alerts. A summary of new alerts is displayed and you can access all alerts in the Alerts queue.
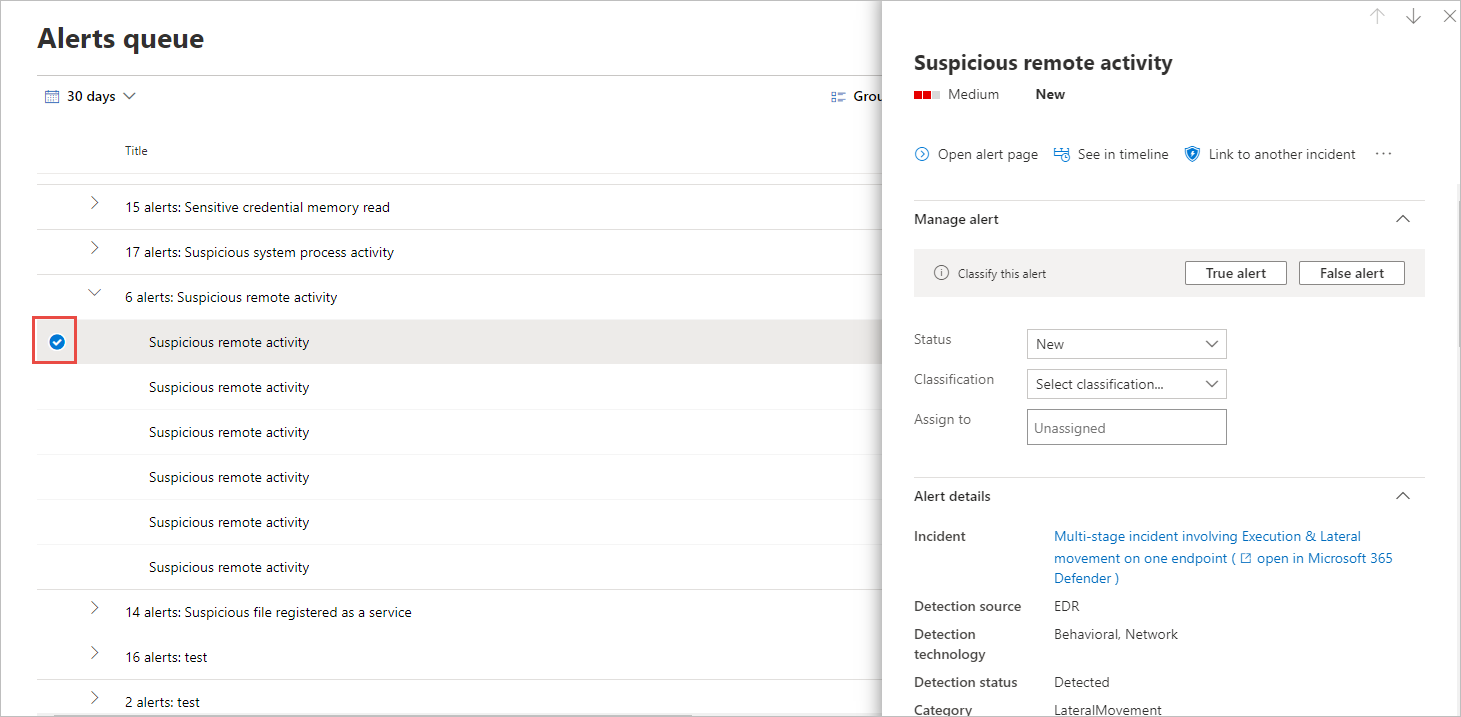
You can manage alerts by selecting an alert in the Alerts queue, or the Alerts tab of the Device page for an individual device.
Selecting an alert in either of those places brings up the Alert management pane.
Watch this video to learn how to use the new Microsoft Defender for Endpoint alert page.
Link to another incident
You can create a new incident from the alert or link to an existing incident.
Assign alerts
If an alert is not yet assigned, you can select Assign to me to assign the alert to yourself.
Suppress alerts
There might be scenarios where you need to suppress alerts from appearing in Microsoft Defender XDR. Defender for Endpoint lets you create suppression rules for specific alerts that are known to be innocuous such as known tools or processes in your organization.
Suppression rules can be created from an existing alert. They can be disabled and reenabled if needed.
When a suppression rule is created, it will take effect from the point when the rule is created. The rule will not affect existing alerts already in the queue, prior to the rule creation. The rule will only be applied on alerts that satisfy the conditions set after the rule is created.
There are two contexts for a suppression rule that you can choose from:
- Suppress alert on this device
- Suppress alert in my organization
The context of the rule lets you tailor what gets surfaced into the portal and ensure that only real security alerts are surfaced into the portal.
You can use the examples in the following table to help you choose the context for a suppression rule:
| Context | Definition | Example scenarios |
|---|---|---|
| Suppress alert on this device | Alerts with the same alert title and on that specific device only will be suppressed. All other alerts on that device will not be suppressed. |
|
| Suppress alert in my organization | Alerts with the same alert title on any device will be suppressed. |
|
Suppress an alert and create a new suppression rule
Create custom rules to control when alerts are suppressed, or resolved. You can control the context for when an alert is suppressed by specifying the alert title, Indicator of compromise, and the conditions. After specifying the context, you'll be able to configure the action and scope on the alert.
Select the alert you'd like to suppress. This brings up the Alert management pane.
Select Create a suppression rule.
You can create a suppression condition using these attributes. An AND operator is applied between each condition, so suppression occurs only if all conditions are met.
- File SHA1
- File name - wildcard supported
- Folder path - wildcard supported
- IP address
- URL - wildcard supported
- Command line - wildcard supported
Select the Triggering IOC.
Specify the action and scope on the alert.
You can automatically resolve an alert or hide it from the portal. Alerts that are automatically resolved will appear in the resolved section of the alerts queue, alert page, and device timeline and will appear as resolved across Defender for Endpoint APIs.
Alerts that are marked as hidden will be suppressed from the entire system, both on the device's associated alerts and from the dashboard and will not be streamed across Defender for Endpoint APIs.
Enter a rule name and a comment.
Click Save.
Note
Alert suppression is not compatible for custom detections. Make sure to fine-tune your custom detections to avoid false positives.
View the list of suppression rules
In the navigation pane, select Settings > Endpoints > Rules > Alert suppression.
The list of suppression rules shows all the rules that users in your organization have created.
For more information on managing suppression rules, see Manage suppression rules
Change the status of an alert
You can categorize alerts (as New, In Progress, or Resolved) by changing their status as your investigation progresses. This helps you organize and manage how your team can respond to alerts.
For example, a team leader can review all New alerts, and decide to assign them to the In Progress queue for further analysis.
Alternatively, the team leader might assign the alert to the Resolved queue if they know the alert is benign, coming from a device that is irrelevant (such as one belonging to a security administrator), or is being dealt with through an earlier alert.
Alert classification
You can choose not to set a classification, or specify whether an alert is a true alert or a false alert. It's important to provide the classification of true positive/false positive. This classification is used to monitor alert quality, and make alerts more accurate. The "determination" field defines additional fidelity for a "true positive" classification.
The steps to classify alerts are included in this video:
Add comments and view the history of an alert
You can add comments and view historical events about an alert to see previous changes made to the alert.
Whenever a change or comment is made to an alert, it is recorded in the Comments and history section.
Added comments instantly appear on the pane.
Related articles
- Exclusions for Microsoft Defender for Endpoint and Microsoft Defender Antivirus
- Manage suppression rules
- View and organize the Microsoft Defender for Endpoint Alerts queue
- Investigate Microsoft Defender for Endpoint alerts
- Investigate a file associated with a Microsoft Defender for Endpoint alert
- Investigate devices in the Microsoft Defender for Endpoint Devices list
- Investigate an IP address associated with a Microsoft Defender for Endpoint alert
- Investigate a domain associated with a Microsoft Defender for Endpoint alert
- Investigate a user account in Microsoft Defender for Endpoint
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.