Implement Microsoft Defender for Cloud Apps
In this module, you'll learn about the seven steps to initiate the use of Microsoft Defender for Cloud Apps.
Before proceeding with any other actions, it's essential to understand how to access the Microsoft Defender for Cloud Apps portal. Access to the portal is necessary for us to take advantage of the various features and functionalities offered by the tool. Therefore, it's imperative to follow the appropriate steps to access the portal before we can utilize Microsoft Defender for Cloud Apps to its fullest potential.
To access the portal
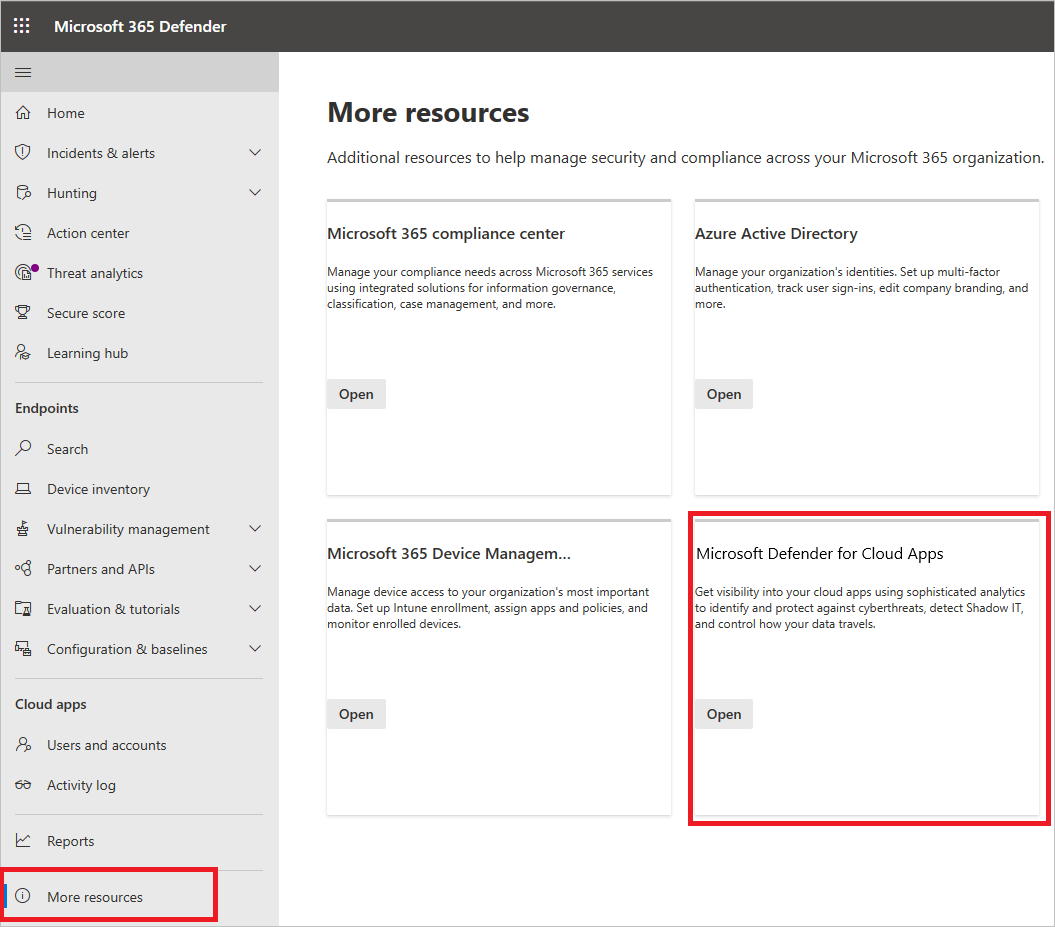
To access the Defender for Cloud Apps portal, go to https://portal.cloudappsecurity.com. You can also access the portal through the Microsoft Defender portal, as follows:
- In the Microsoft Defender portal, select More resources, and then select Defender for Cloud Apps.
Step 1: Set instant visibility, protection, and governance actions for your apps
How to page: Set instant visibility, protection, and governance actions for your apps
Required task: Connect apps
- From the settings cog, select App connectors.
- Select the plus sign (+) to add an app and select an app.
- Follow the configuration steps to connect the app.
Why connect an app? After you connect an app, you can gain deeper visibility so you can investigate activities, files, and accounts for the apps in your cloud environment.
Step 2: Protect sensitive information with DLP policies
How to page: Protect sensitive information with DLP policies Recommended task: Enable file monitoring and create file policies
- Go to Settings, and then under Information Protection, select Files.
- Select Enable file monitoring and then select Save.
- If you use sensitivity labels from Microsoft Purview Information Protection, under Information Protection, select Microsoft Information Protection.
- Select the required settings and then select Save.
- In Step 3, create File policies to meet your organizational requirements.
Tip
You can view files from your connected apps by browsing to Investigate > Files.
Migration recommendation
We recommend using Defender for Cloud Apps sensitive information protection in parallel with your current Cloud Access Security Broker (CASB) solution. Start by connecting the apps you want to protect to Microsoft Defender for Cloud Apps. Since API connectors use out-of-band connectivity, no conflict will occur. Then progressively migrate your policies from your current CASB solution to Defender for Cloud Apps.
Note
For third-party apps, verify that the current load does not exceed the app's maximum number of allowed API calls.
Step 3: Control cloud apps with policies
How to page: Control cloud apps with policies
Required task: Create policies
To create policies
- Go to Control > Templates.
- Select a policy template from the list, and then choose (+) Create policy.
- Customize the policy (select filters, actions, and other settings), and then choose Create.
- On the Policies tab, choose the policy to see the relevant matches (activities, files, alerts).
Tip
To cover all your cloud environment security scenarios, create a policy for each risk category.
How can policies help your organization?
Policies enable you to track trends, identify security threats, and generate tailored reports and alerts. By implementing policies, you can establish governance actions and configure data loss prevention measures and file-sharing controls.
Step 4: Set up Cloud Discovery
How to page: Set up Cloud Discovery
Required task: Enable Defender for Cloud Apps to view your cloud app use.
- Integrate with Microsoft Defender for Endpoint to automatically enable Defender for Cloud Apps to monitor your Windows 10 and Windows 11 devices inside and outside your corporation.
- If you use Zscaler, integrate it with Defender for Cloud Apps.
- To achieve full coverage, create a continuous Cloud Discovery report.
- From the settings cog, select Settings.
- Under Cloud Discovery, choose Automatic log upload.
- On the Data sources tab, add your sources.
- On the Log collectors tab, configure the log collector.
Migration recommendation
We recommend using Defender for Cloud Apps discovery in parallel with your current CASB solution. Start by configuring automatic firewall log upload to Defender for Cloud Apps log collectors. If you use Defender for Endpoint, in Microsoft Defender XDR, make sure you turn on the option to forward signals to Defender for Cloud Apps. Configuring Cloud Discovery won't conflict with the log collection of your current CASB solution.
To create a snapshot Cloud Discovery report
Go to Discover > Create snapshot report and follow the steps shown.
Why should you configure Cloud Discovery reports?
Having visibility into shadow IT in your organization is critical. After your logs are analyzed, you can easily find which cloud apps are being used, by which people, and on which devices.
Step 5: Deploy Conditional Access App Control for catalog apps
How to page: Deploy Conditional Access App Control for catalog apps
Recommended task: Deploy Conditional Access App Control for catalog apps.
- Configure your IdP to work with Defender for Cloud Apps. If you have Microsoft Entra ID, you can use inline controls such as Monitor only and Block downloads, which will work for any catalog app out of the box.
- Onboard apps onto access and session controls.
- Onboard apps onto access and session controls.
- Sign in to each app using a user scoped to the policy.
- Refresh the Conditional Access App Control page and to view the app.
- Verify the apps are configured to use access and session controls.
To configure session controls for custom line-of-business apps, non-featured SaaS apps, and on-premises apps, see Deploy Conditional Access App Control for custom apps using Microsoft Entra ID.
Migration recommendation
Using Conditional Access App Control in parallel with another CASB solution can potentially lead to an app being proxied twice, causing latency or other errors. Therefore, we recommended progressively migrating apps and policies to Conditional Access App Control, creating the relevant session or access policies in Defender for Cloud Apps as you go.
Step 6: Personalize your experience
How to page: Personalize your experience
Recommended task: Add your organization details
To enter email settings
- From the settings cog, select Mail settings.
- Under Email sender identity, enter your organization's email address and display name.
- Under Email design, upload your organization's email template.
To set admin notifications
- in the navigation bar, choose your user name and then go to User settings.
- Under Notifications, configure the method of notification you want to receive.
- Choose Save.
To customize the score metrics
- From the settings cog, select Settings.
- Under Cloud Discovery, select Score metrics.
- Configure the importance of various risk values.
- Choose Save.
Now the risk scores given to discovered apps are configured precisely according to your organization needs and priorities.
Why should you personalize your environment?
Some features work best when they're customized to your needs. Provide a better experience for your users with your own email templates. Decide what notifications you receive and customize your risk score metric to fit your organization's preferences.
Step 7: Organize the data according to your needs
How to page: Working with ip ranges and tags
Recommended task: Configure important settings
To create ip address tags
- From the settings cog, select Settings.
- Under Cloud Discovery, choose Continuous reports.
- Choose Create report.
- Follow the configuration steps.
- Choose Create.
Now you can view discovered data based on your own preferences, such as business units or IP ranges.
To add domains
- From the settings cog, select Settings.
- Under System, choose Organizations details.
- Add your organization's domains.
- Choose Save.
Why should you configure these settings?
These settings help give you better control of features in the console. With IP tags, it's easier to create policies that fit your needs, to accurately filter data, and more. Use Data views to group your data into logical categories.