Tutorial: Protect Exchange Online email on managed devices with Microsoft Intune
This tutorial demonstrates how to use Microsoft device compliance policies with Microsoft Entra conditional access policy, to allow iOS devices access to Exchange only when they're managed by Intune and use an approved email app.
In this tutorial, you'll learn how to:
- Create an Intune iOS device compliance policy to set the conditions that a device must meet to be considered compliant.
- Create a Microsoft Entra Conditional Access policy that requires iOS devices to enroll in Intune, comply with Intune policies, and use the approved Outlook mobile app to access Exchange Online email.
Prerequisites
You need a test tenant with the following subscriptions for this tutorial:
- Microsoft Intune Plan 1 subscription (sign up for a free trial account)
- Microsoft Entra ID P1 (free trial)
- Microsoft 365 Apps for business subscription that includes Exchange (free trial)
Sign in to Intune
Sign in to the Microsoft Intune admin center as a Global administrator or an Intune Service administrator. If you have an Intune Trial subscription, the account you created the subscription with is the Global administrator.
Create an email device profile
This tutorial requires you to create an iOS/iPadOS device Email profile. TO do so, follow the guidance in Step 11 – Create a device profile from the Try Intune tasks area of the Intune documentation. The email profile is used to require iOS/iPad devices to use work email.
When you create the email profile, assign the profile to the same group of devices that you use later for the device compliance policy and Conditional Access policies that you create in subsequent steps of this tutorial.
After you create the email profile, return here to continue.
Create the iOS device compliance policy
Set up an Intune device compliance policy to set the conditions that a device must meet to be considered compliant. For this tutorial, we create a device compliance policy for iOS devices. Compliance policies are platform-specific, so you need a separate compliance policy for each device platform you want to evaluate.
Sign in to the Microsoft Intune admin center.
Select Devices > Compliance.
On the Policies tab, choose Create policy.
On the Create a policy page, for Platform select iOS/iPadOS. Select Create to continue.
On the Basics tab, enter the following properties:
- Name: Enter a descriptive name for the new profile. For this example, enter iOS compliance policy test.
- Description: Optional - Enter iOS compliance policy test.
Select Next to continue.
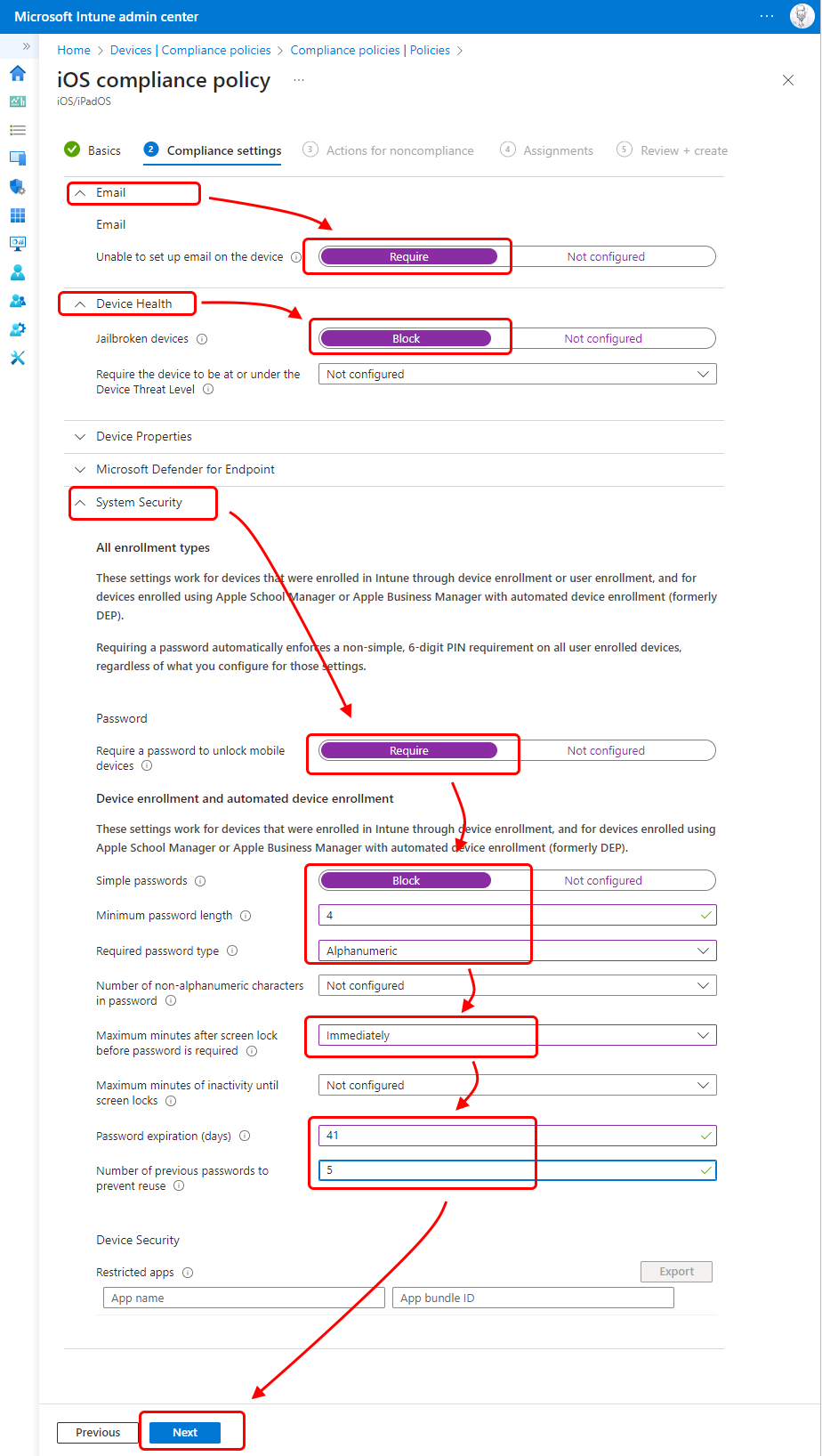
On the Compliance settings tab:
Expand Email, and then set Unable to set up email on the device to Require.
Expand Device Health, and set Jailbroken devices to Block.
Expand System Security, and configure the following settings:
- Require a password to unlock mobile devices to Require
- Simple passwords to Block
- Minimum password length to 4
Tip
Default values that are grayed out and italicized are only recommendations. You must replace values that are recommendations to configure a setting.
- Required password type to Alphanumeric
- Maximum minutes after screen lock before password is required to Immediately
- Password expiration (days) to 41
- Number of previous passwords to prevent reuse to 5
To continue, select Next.
Select Next to skip Actions for noncompliance.
On the Assignments tab, for Included groups, select Add all devices, or select a group that contains only those devices that should receive this policy. Be sure to use the same assignment as you used for the email device profile.
Select Next to continue.
On the Review + create tab, review your settings. When you select Create, your changes are saved, and the profile is assigned.
Create the Conditional Access policy
Next, use the Microsoft Intune admin center to create a Conditional Access policy. You integrate Conditional Access with Intune to help control the devices and apps that can connect to your organizations email and resources.
The Conditional Access policy will:
- Require devices that run any platform to enroll in Intune and to comply with your Intune compliance policy before those devices can be used to access Exchange Online.
- Require devices use the Outlook app for email access.
Conditional Access policies are configurable in either the Microsoft Entra admin center or the Microsoft Intune admin center. Since we're already in the admin center, we can create the policy here.
Sign in to the Microsoft Intune admin center.
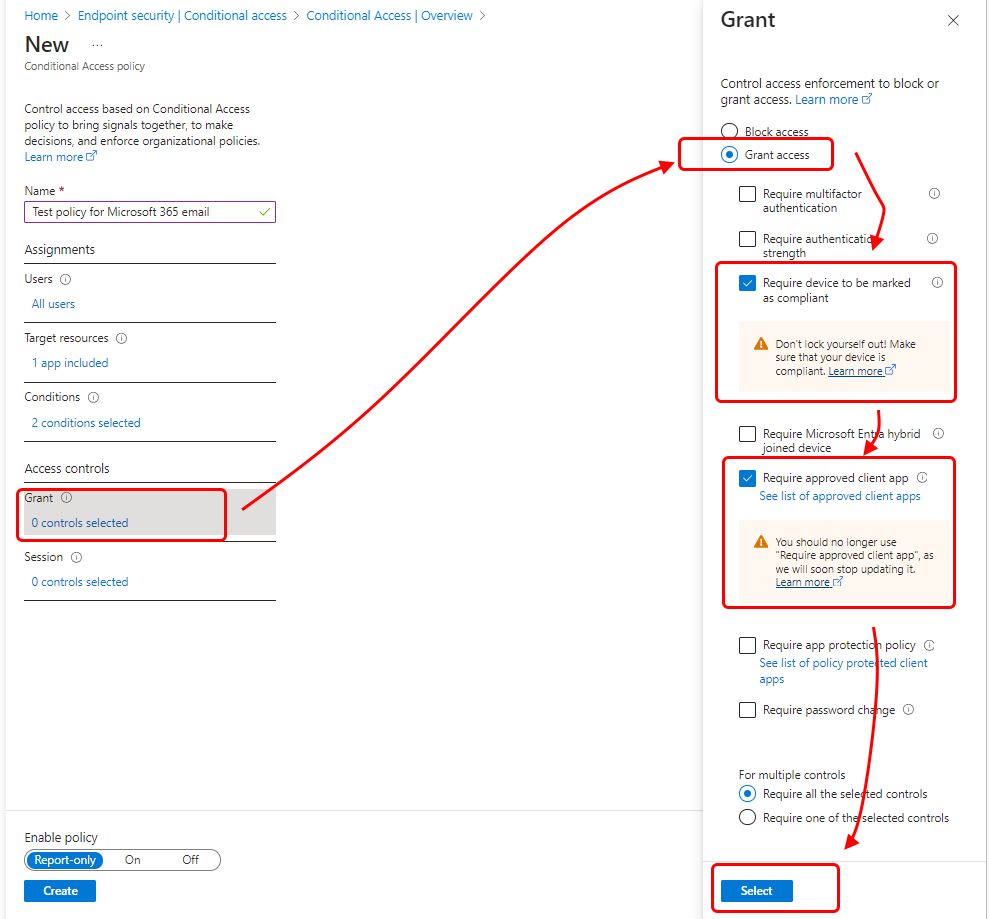
Select Endpoint security > Conditional Access > Create new policy.
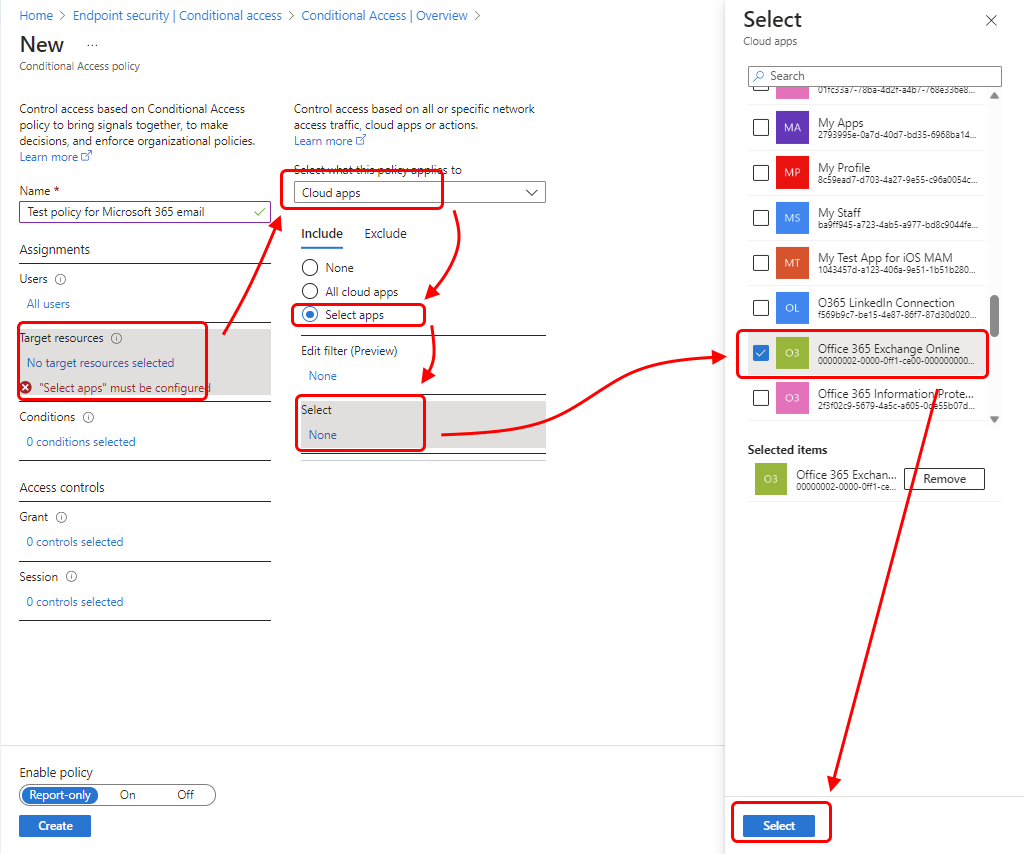
For Name, enter Test policy for Microsoft 365 email.
Under Assignments, for Users, select 0 users and groups selected. On the Include tab, select All users. The value for Users updates to All users.
Also under Assignments, select Target resources. For Select what this policy applies to drop-down, select Cloud apps.
Next, because we want to protect Microsoft 365 Exchange Online email, select that app by following these steps:
- On the Include tab, choose Select apps.
- For the Select category, select None to open the Select pane with its applications list.
- From the applications list, select the checkbox for Office 365 Exchange Online, and then choose Select.
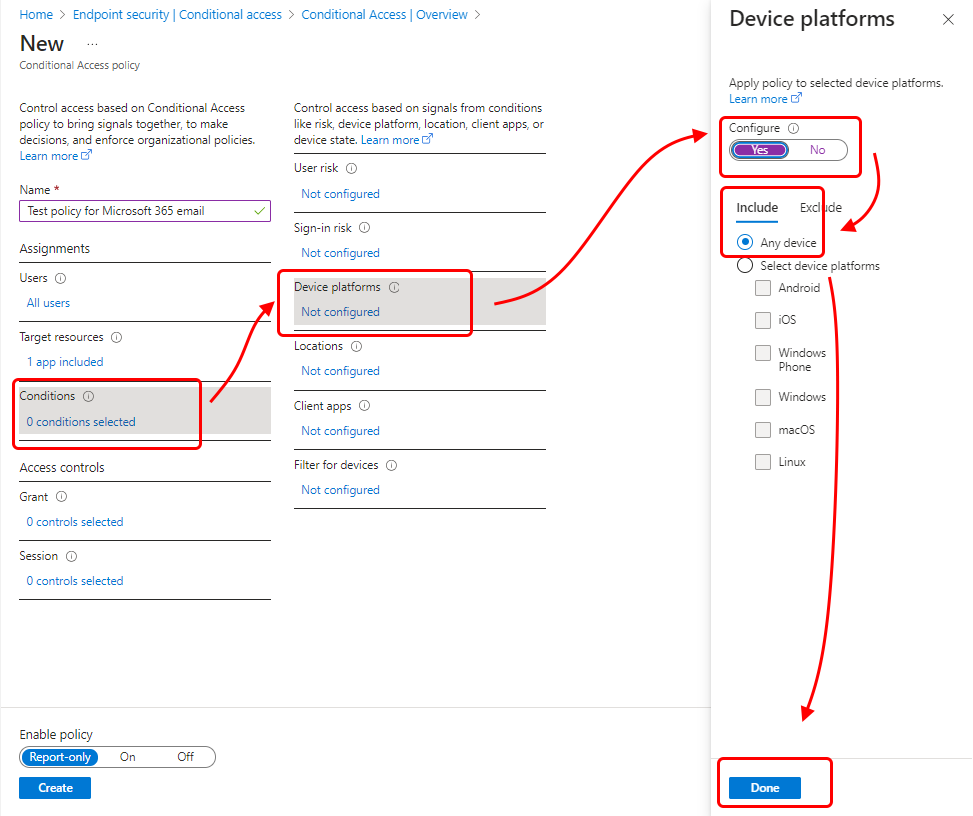
Also under Assignments, select Conditions > Device platforms to open the Device platforms pane.
- Set Configure to Yes.
- On the Include tab, select Any device, and then select Done.
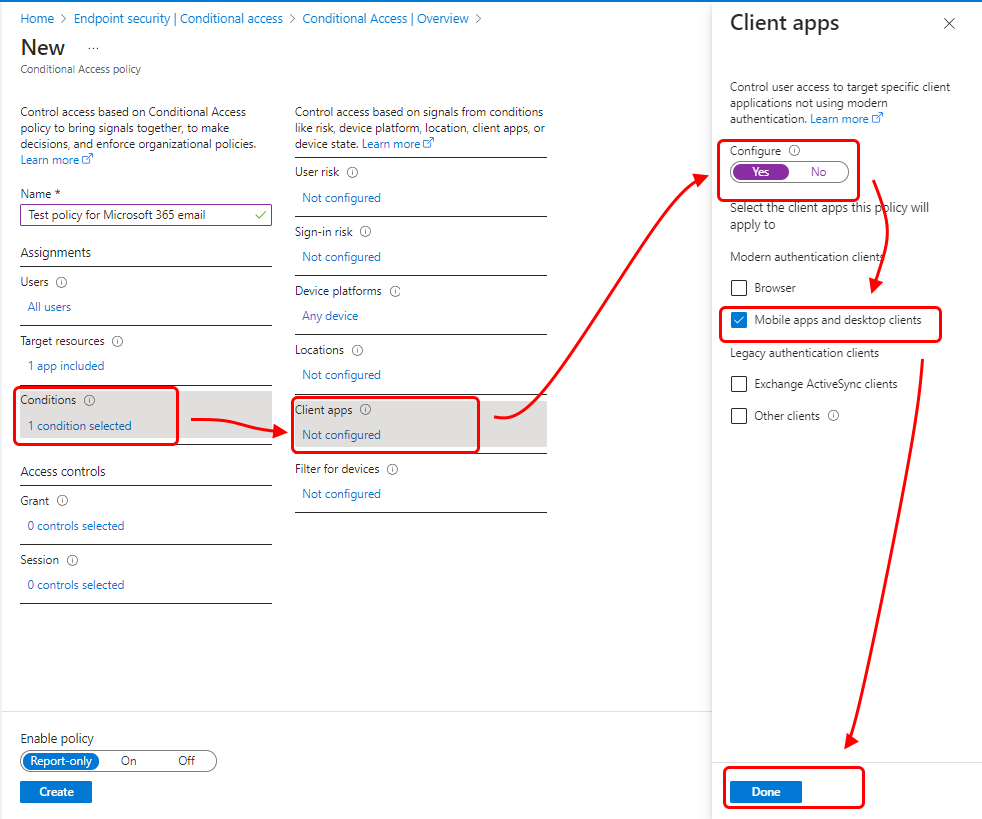
Once again, under Assignments, select Conditions > Client apps.
Set Configure to Yes.
For this tutorial, select Mobile apps and desktop clients, part of Modern authentication clients (which refers to apps like Outlook for iOS and Outlook for Android). Clear all other check boxes.
Select Done, and then select Done again.
Under Access controls, select Grant.
On the Grant pane, select Grant access.
Select Require device to be marked as compliant.
Select Require approved client app.
Under For multiple controls, select Require all the selected controls. This setting ensures that both requirements you selected are enforced when a device tries to access email.
Choose Select.
Under Enable policy, select On.
Select Create to save your changes. The profile is assigned.
Try it out
With the policies you've created, any iOS device that attempts to sign in to Microsoft 365 email must enroll in Intune and use the Outlook mobile app for iOS/iPadOS. To test this scenario on an iOS device, try signing in to Exchange Online using credentials for a user in your test tenant. You're prompted to enroll the device and install the Outlook mobile app.
To test on an iPhone, go to Settings > Passwords & Accounts > Add Account > Exchange.
Enter the email address for a user in your test tenant, and then press Next.
Press Sign In.
Enter the test user's password, and press Sign in.
A message appears that says your device must be managed to access the resource, along with an option to enroll.
Clean up resources
When the test policies are no longer needed, you can remove them.
Sign in to the Microsoft Intune admin center as a Global Administrator or an Intune Service Administrator.
Select Devices > Compliance.
In the Policy name list, select the context menu (...) for your test policy, and then select Delete. Select OK to confirm.
Select Endpoint security > Conditional access > policies.
In the Policy name list, select the context menu (...) for your test policy, and then select Delete. Select Yes to confirm.
Next steps
In this tutorial, you created policies that require iOS devices to enroll in Intune and use the Outlook app to access Exchange Online email. To learn about using Intune with Conditional Access to protect other apps and services, including Exchange ActiveSync clients for Microsoft 365 Exchange Online, see Set up Conditional Access.
Palaute
Tulossa pian: Vuoden 2024 aikana poistamme asteittain GitHub Issuesin käytöstä sisällön palautemekanismina ja korvaamme sen uudella palautejärjestelmällä. Lisätietoja on täällä: https://aka.ms/ContentUserFeedback.
Lähetä ja näytä palaute kohteelle