אירוע
9 באפר׳, 15 - 10 באפר׳, 12
קוד העתיד עם בינה מלאכותית והתחברות לעמיתים ומומחים של Java ב- JDConf 2025.
הירשם כעתהדפדפן הזה אינו נתמך עוד.
שדרג ל- Microsoft Edge כדי לנצל את התכונות, עדכוני האבטחה והתמיכה הטכנית העדכניים ביותר.
In this article, you'll learn how to integrate Trakstar with Microsoft Entra ID. When you integrate Trakstar with Microsoft Entra ID, you can:
To configure Microsoft Entra integration with Trakstar, you need the following items:
In this article, you configure and test Microsoft Entra single sign-on in a test environment.
הערה
Identifier of this application is a fixed string value so only one instance can be configured in one tenant.
To configure the integration of Trakstar into Microsoft Entra ID, you need to add Trakstar from the gallery to your list of managed SaaS apps.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, as well as walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO with Trakstar using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in Trakstar.
To configure and test Microsoft Entra SSO with Trakstar, perform the following steps:
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Trakstar > Single sign-on.
On the Select a single sign-on method page, select SAML.
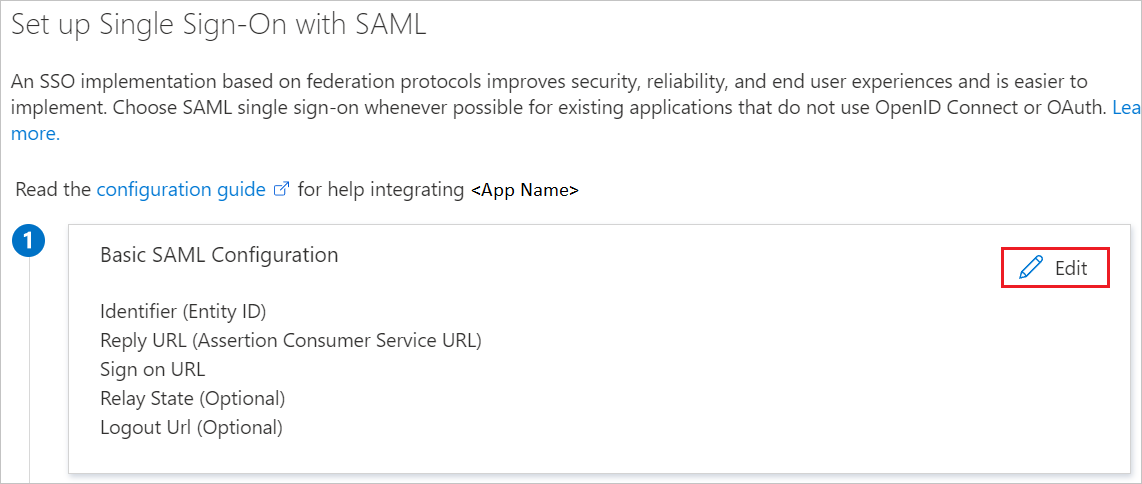
On the Set up single sign-on with SAML page, click the pencil icon for Basic SAML Configuration to edit the settings.
In the Basic SAML Configuration section, enter the following values in the corresponding input fields:
| Field name | Value | Note |
|---|---|---|
| Reply URL (Assertion Consumer Service URL) | https://perform.trakstar.com/auth/saml/callback?namespace=<YOUR_NAMESPACE> |
Replace <YOUR_NAMESPACE> with a real value, which is visible in the ACS (Consumer) URL field in Trakstar Perform. See the note that appears after this table. |
| Sign on URL | https://perform.trakstar.com/auth/saml/?namespace=<YOUR_NAMESPACE> |
This URL is similar to the preceding URL, but it doesn't have the /callback portion. |
| Identifier (Entity ID) | https://perform.trakstar.com |
הערה
These values are only examples. You must use the values that are specific to your namespace in Trakstar Perform, which are visible by signing into the application and going to Settings > Authentication & SSO > SAML 2.0 > Configure.
If you don't see the Authentication & SSO tab in Settings, you might not have the feature, and you should contact Trakstar customer support. You can also refer to the patterns shown in the Basic SAML Configuration section.
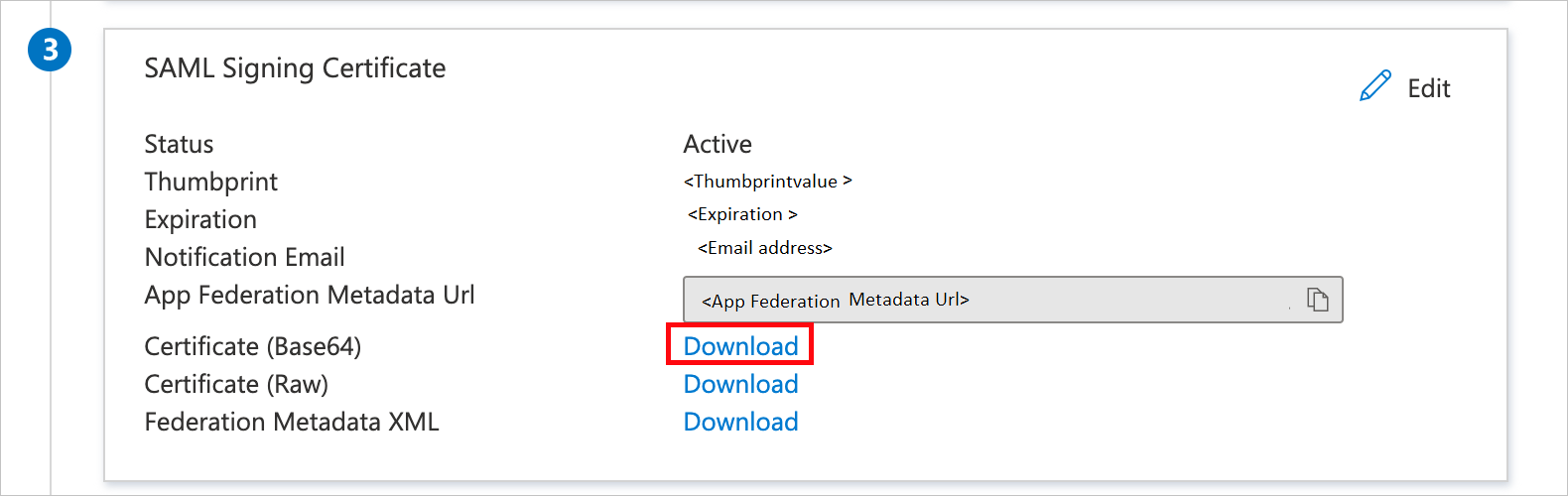
On the Set up Single Sign-On with SAML page, in the SAML Signing Certificate section, click Download to download the Certificate (Base64) from the given options as per your requirement and save it on your computer.
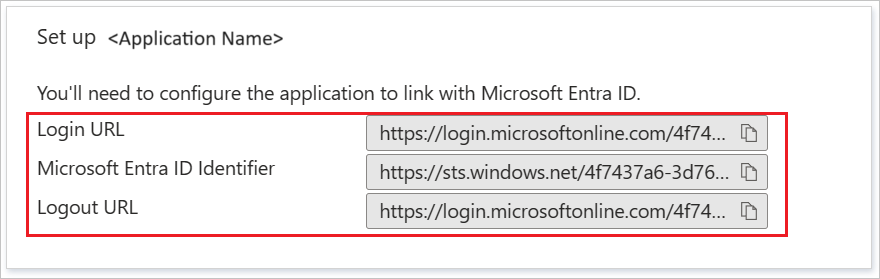
On the Set up Trakstar section, copy the appropriate URL(s) as per your requirement.
In this section, you'll create a test user called B.Simon.
B.Simon.B.Simon@contoso.com.In this section, you'll enable B.Simon to use single sign-on by granting access to Trakstar.
To configure single sign-on on Trakstar side, you need to sign in as an Administrator and enter the content of downloaded Certificate (Base64) and appropriate copied URLs from Azure portal. They set this setting to have the SAML SSO connection set properly on both sides.
In this section, you create a user called Britta Simon in Trakstar. Work with Trakstar Administrator to add the users in the Trakstar platform. Users must be created and activated before you use single sign-on.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Click on Test this application, this will redirect to Trakstar Sign-on URL where you can initiate the login flow.
Go to Trakstar Sign-on URL directly and initiate the login flow from there.
You can use Microsoft My Apps. When you click the Trakstar tile in the My Apps, this will redirect to Trakstar Sign-on URL. For more information about the My Apps, see Introduction to the My Apps.
Once you configure Trakstar you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
אירוע
9 באפר׳, 15 - 10 באפר׳, 12
קוד העתיד עם בינה מלאכותית והתחברות לעמיתים ומומחים של Java ב- JDConf 2025.
הירשם כעתהדרכה
מודול
Monitor and maintain Microsoft Entra ID - Training
Audit and diagnostic logs within Microsoft Entra ID provide a rich view into how users are accessing your Azure solution. Learn to monitor, troubleshoot, and analyze sign-in data.
אישור
Microsoft Certified: Identity and Access Administrator Associate - Certifications
להדגים את התכונות של Microsoft Entra ID כדי לבצע מודרניזציה של פתרונות זהות, ליישם פתרונות היברידיים וליישם פיקוח על זהות.