Događaj
9. tra 15 - 10. tra 12
Programirajte budućnost s umjetnom inteligencijom i povežite se s Java kolegama i stručnjacima na JDConfu 2025.
Registrirajte se odmahOvaj preglednik više nije podržan.
Prijeđite na Microsoft Edge, gdje vas čekaju najnovije značajke, sigurnosna ažuriranja i tehnička podrška.
In this article, you'll learn how to integrate Visit.org with Microsoft Entra ID. When you integrate Visit.org with Microsoft Entra ID, you can:
To get started, you need the following items:
In this article, you configure and test Microsoft Entra SSO in a test environment.
Napomena
Identifier of this application is a fixed string value so only one instance can be configured in one tenant.
To configure the integration of Visit.org into Microsoft Entra ID, you need to add Visit.org from the gallery to your list of managed SaaS apps.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, as well as walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO with Visit.org using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in Visit.org.
To configure and test Microsoft Entra SSO with Visit.org, perform the following steps:
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Visit.org > Single sign-on.
On the Select a single sign-on method page, select SAML.
On the Set up single sign-on with SAML page, click the pencil icon for Basic SAML Configuration to edit the settings.
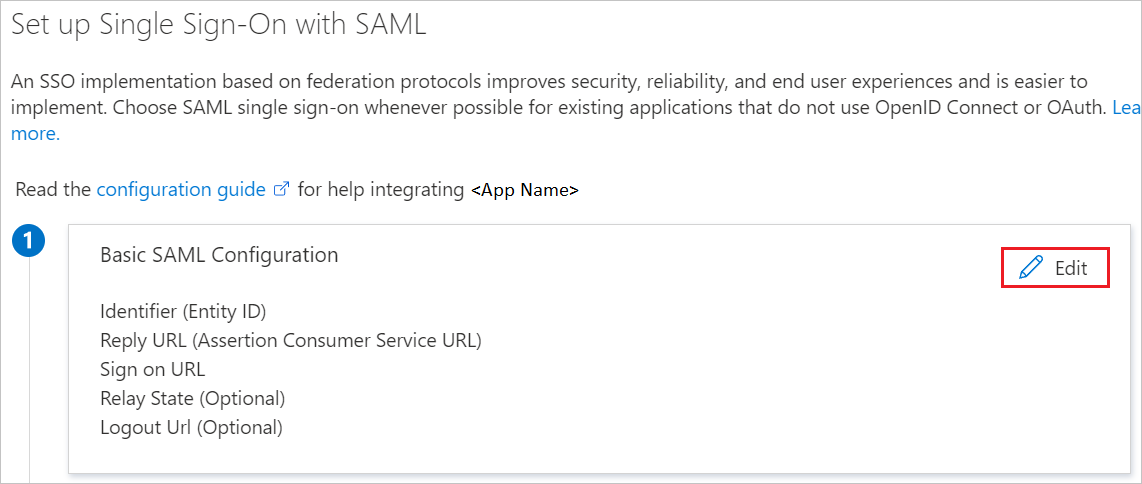
On the Basic SAML Configuration section, the application is pre-configured and the necessary URLs are already pre-populated with Azure. The user needs to save the configuration by clicking the Save button.
Visit.org application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows the list of default attributes.
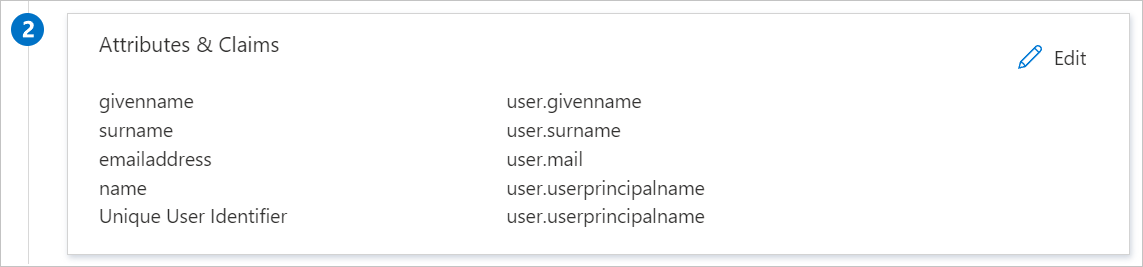
In addition to above, Visit.org application expects few more attributes to be passed back in SAML response which are shown below. These attributes are also pre populated but you can review them as per your requirements.
| Name | Source Attribute |
|---|---|
| user.emailaddress | |
| first_name | user.givenname |
| last_name | user.surname |
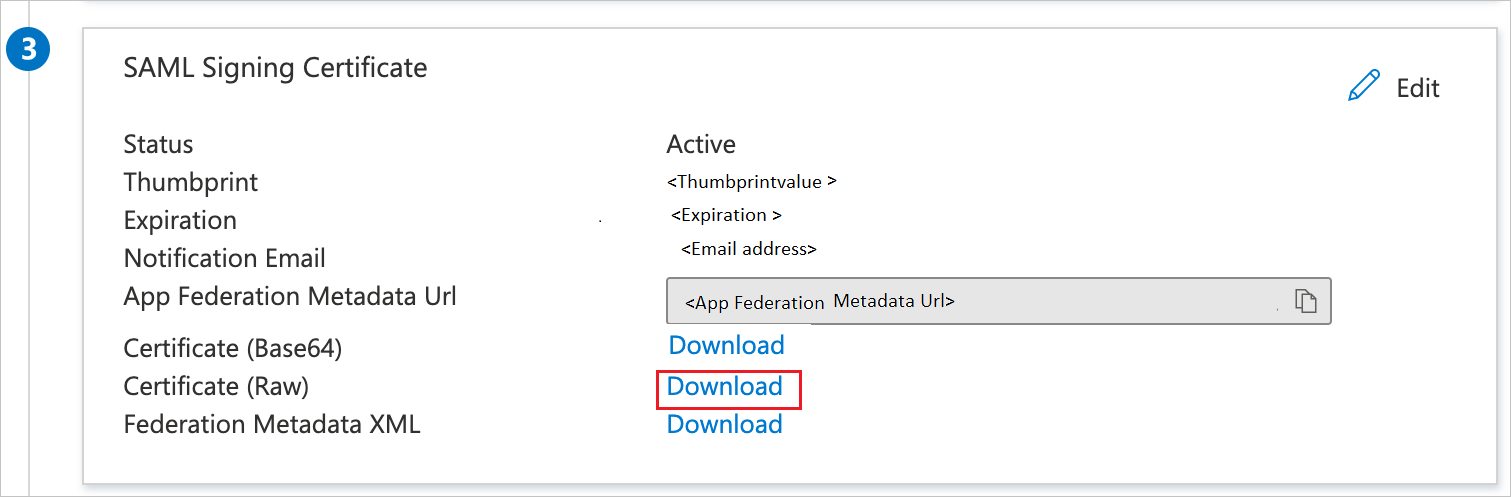
On the Set up single sign-on with SAML page, in the SAML Signing Certificate section, find Certificate (Raw) and select Download to download the certificate and save it on your computer.
On the Set up Visit.org section, copy the appropriate URL(s) based on your requirement.

In this section, you'll create a test user called B.Simon.
B.Simon.B.Simon@contoso.com.In this section, you'll enable B.Simon to use single sign-on by granting access to Visit.org.
To configure single sign-on on Visit.org side, you need to send the downloaded Certificate (Raw) and appropriate copied URLs from the application configuration to Visit.org support team. They set this setting to have the SAML SSO connection set properly on both sides.
In this section, you create a user called B.Simon in Visit.org. Work with Visit.org support team to add the users in the [Application Name] platform. Users must be created and activated before you use single sign-on.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Click on Test this application, and you should be automatically signed in to the Visit.org for which you set up the SSO.
You can use Microsoft My Apps. When you click the Visit.org tile in the My Apps, you should be automatically signed in to the Visit.org for which you set up the SSO. For more information, see Microsoft Entra My Apps.
Once you configure Visit.org you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Cloud App Security.
Događaj
9. tra 15 - 10. tra 12
Programirajte budućnost s umjetnom inteligencijom i povežite se s Java kolegama i stručnjacima na JDConfu 2025.
Registrirajte se odmahObuka
Modul
Discover how Microsoft Entra External ID can provide secure, seamless sign-in experiences for your consumers and business customers. Explore tenant creation, app registration, flow customization, and account security.
Certifikacija
Microsoft Certified: Identity and Access Administrator Associate - Certifications
Demonstrate the features of Microsoft Entra ID to modernize identity solutions, implement hybrid solutions, and implement identity governance.
Dokumentacija
Microsoft Entra SSO integration with 23 Video - Microsoft Entra ID
Learn how to configure single sign-on between Microsoft Entra ID and 23 Video.