Evenimente
9 apr., 15 - 10 apr., 12
Codificați viitorul cu AI și conectați-vă cu colegii și experții Java la JDConf 2025.
Înregistrați-vă acumAcest browser nu mai este acceptat.
Faceți upgrade la Microsoft Edge pentru a profita de cele mai noi funcții, actualizări de securitate și asistență tehnică.
In this article, you'll learn how to integrate Tripwire Enterprise with Microsoft Entra ID. Tripwire Enterprise is the leading compliance monitoring solution, using file integrity monitoring (FIM) and security configuration management (SCM). When you integrate Tripwire Enterprise with Microsoft Entra ID, you can:
You'll configure and test Microsoft Entra single sign-on for Tripwire Enterprise in a test environment. Tripwire Enterprise supports IDP initiated single sign-on.
To integrate Microsoft Entra ID with Tripwire Enterprise, you need:
Before you begin the process of configuring single sign-on, you need to add the Tripwire Enterprise application from the Microsoft Entra gallery. You need a test user account to assign to the application and test the single sign-on configuration.
Add Tripwire Enterprise from the Microsoft Entra application gallery to configure single sign-on with Tripwire Enterprise. For more information on how to add application from the gallery, see the Quickstart: Add application from the gallery.
Follow the guidelines in the create and assign a user account article to create a test user account called B.Simon.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, and assign roles. The wizard also provides a link to the single sign-on configuration pane. Learn more about Microsoft 365 wizards..
Complete the following steps to enable Microsoft Entra single sign-on.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Tripwire Enterprise > Single sign-on.
On the Select a single sign-on method page, select SAML.
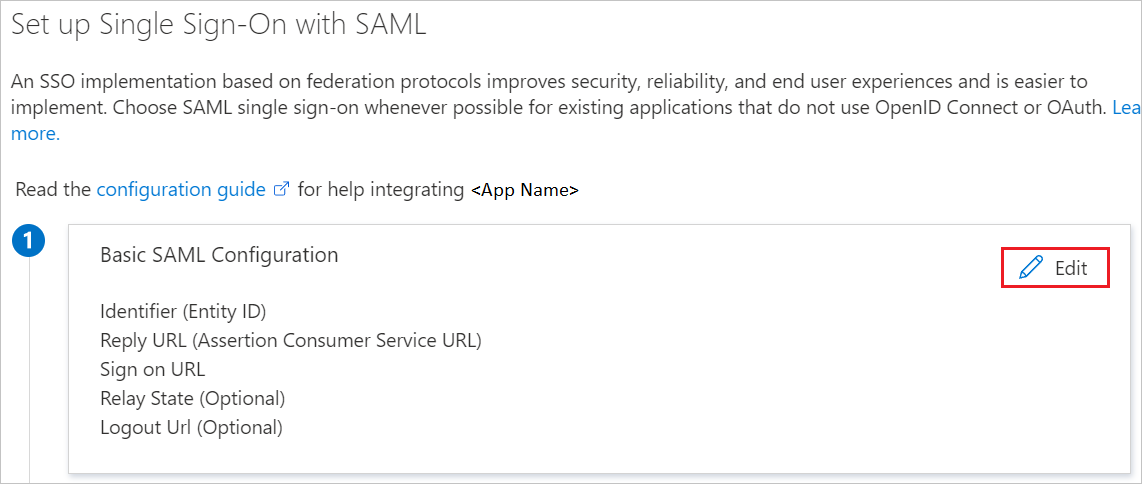
On the Set up single sign-on with SAML page, select the pencil icon for Basic SAML Configuration to edit the settings.
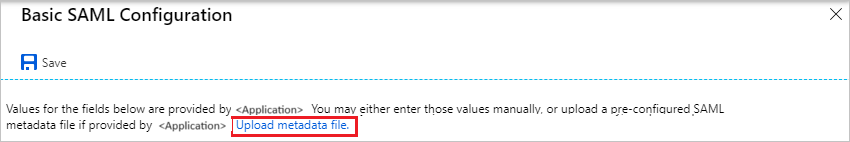
On the Basic SAML Configuration section, if you have Service Provider metadata file then perform the following steps:
a. Click Upload metadata file.
b. Click on folder logo to select the metadata file and click Upload.
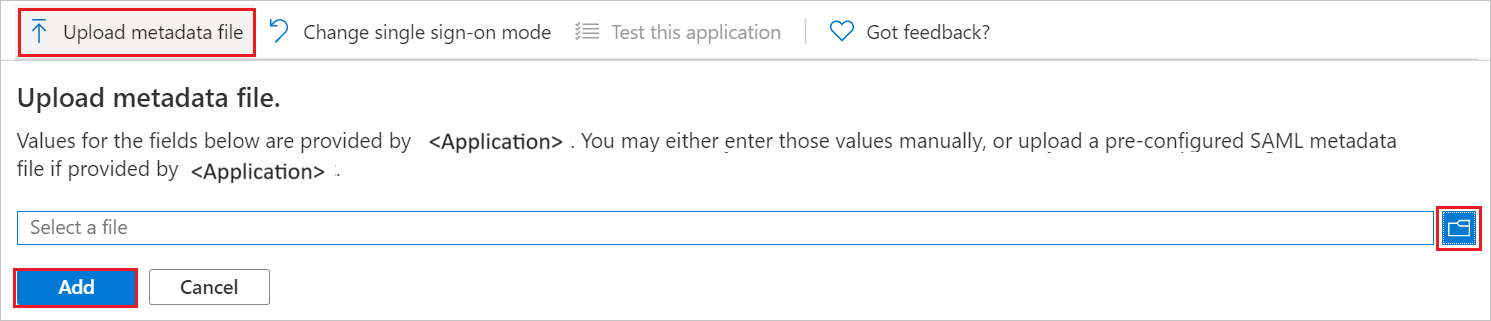
c. After the metadata file is successfully uploaded, the Identifier and Reply URL values get auto populated in Basic SAML Configuration section.
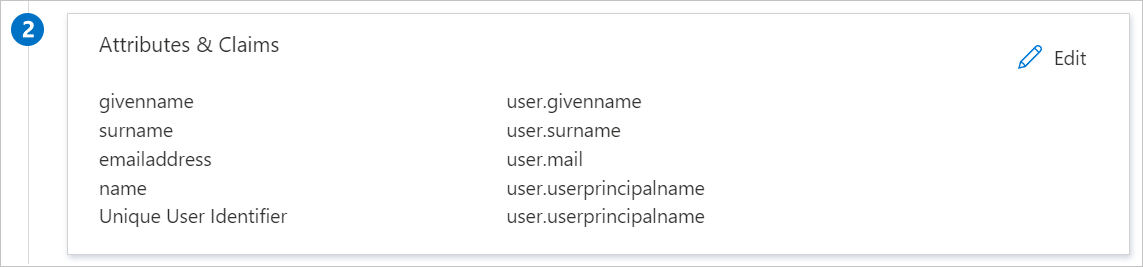
Your Tripwire Enterprise application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows an example for this. The default value of Unique User Identifier is user.userprincipalname but Tripwire Enterprise expects this to be mapped with the user's email address. For that you can use user.mailnickname attribute from the list or use the appropriate attribute value based on your organization configuration.
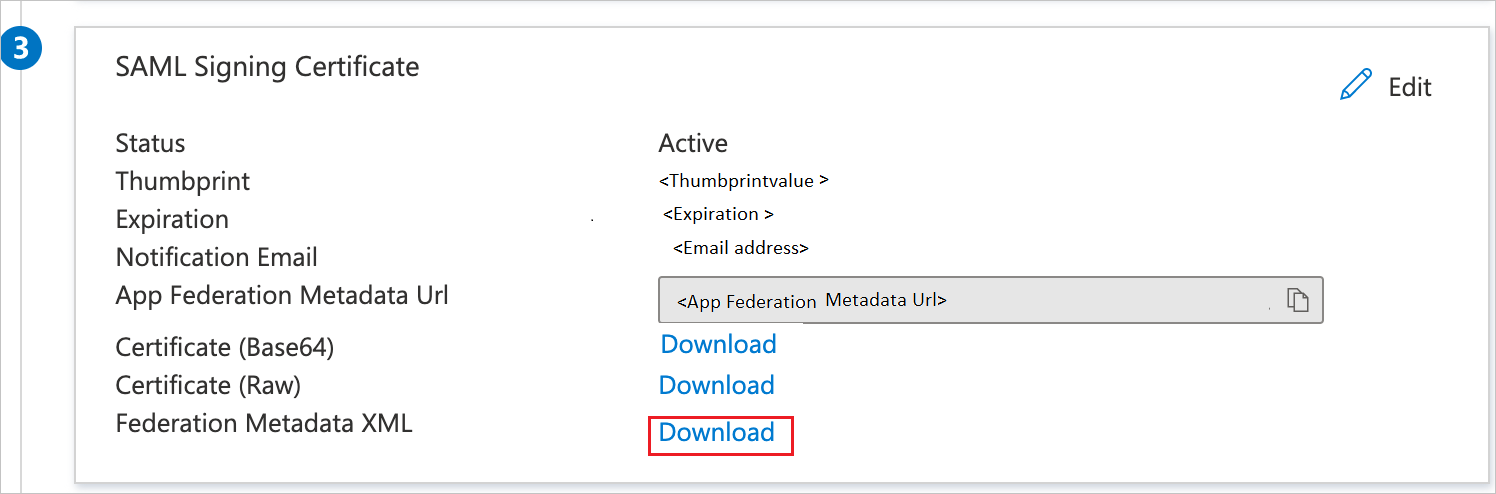
On the Set-up single sign-on with SAML page, in the SAML Signing Certificate section, find Federation Metadata XML and select Download to download the certificate and save it on your computer.
To configure single sign-on in Tripwire Enterprise, please see Using Tripwire Enterprise with SAML Authentication section in the Tripwire Enterprise Hardening Guide, available for download on the Tripwire Customer Center. If you require assistance, contact Tripwire Enterprise support team.
To create a Tripwire Enterprise user, please see Creating a User Account section in the Tripwire Enterprise User Guide, available for download on the Tripwire Customer Center. If you require assistance, contact Tripwire Enterprise support team.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Click on Test this application, and you should be automatically signed in to the Tripwire Enterprise for which you set up the SSO.
You can use Microsoft My Apps. When you click the Tripwire Enterprise tile in the My Apps, you should be automatically signed in to the Tripwire Enterprise for which you set up the SSO. For more information, see Microsoft Entra My Apps.
Once you configure Tripwire Enterprise you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Cloud App Security.
Evenimente
9 apr., 15 - 10 apr., 12
Codificați viitorul cu AI și conectați-vă cu colegii și experții Java la JDConf 2025.
Înregistrați-vă acumInstruire
Modul
Implement and monitor the integration of enterprise apps for SSO - Training
Deploying and monitoring enterprise applications to Azure solutions can ensure security. Explore how to deploy on-premises and cloud based apps to users.
Certificare
Certificat Microsoft: asociat de administrator de identitate și acces - Certifications
Demonstrează caracteristicile Microsoft Entra ID pentru a moderniza soluțiile de identitate, a implementa soluții hibride și a implementa guvernanța identității.