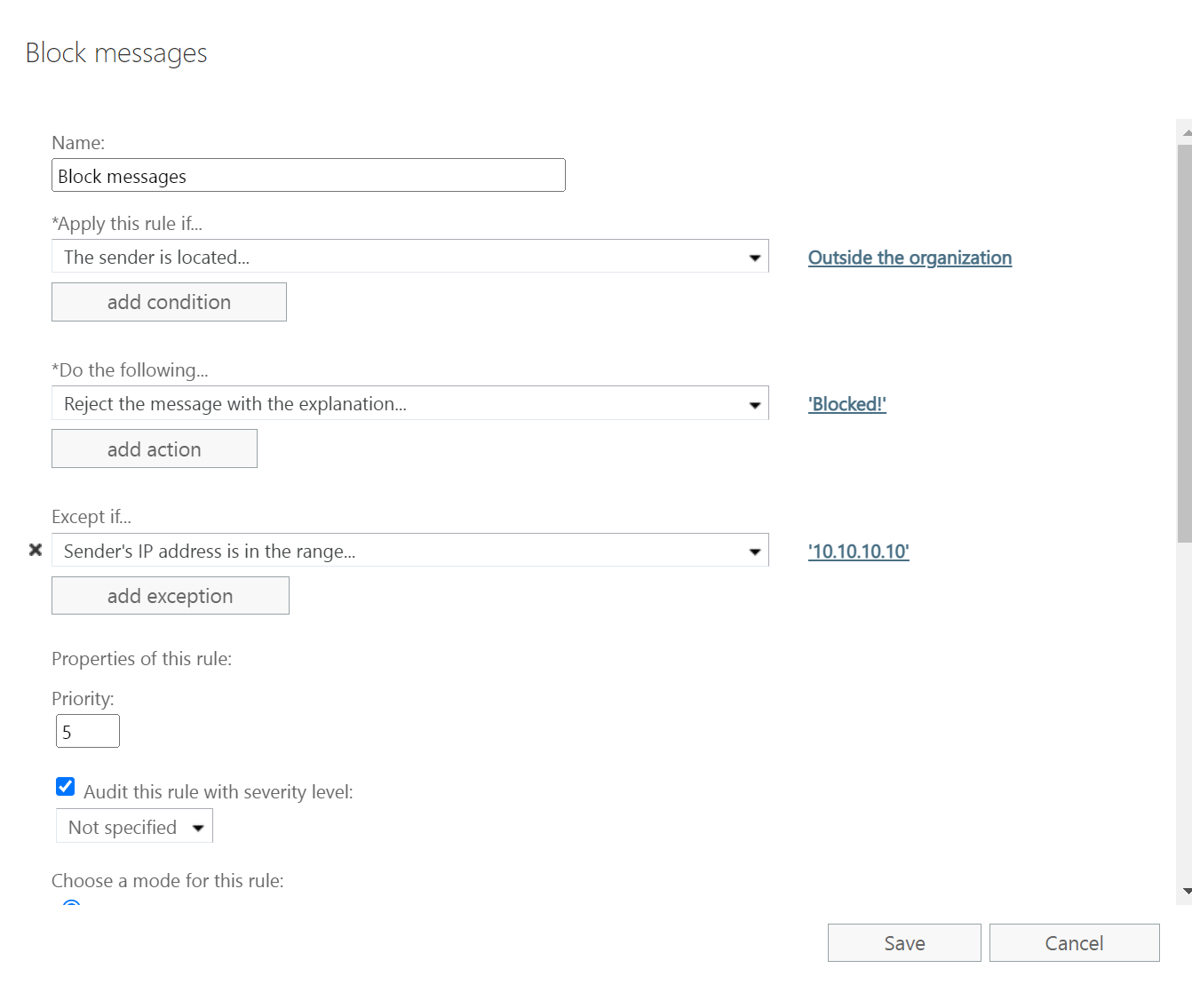
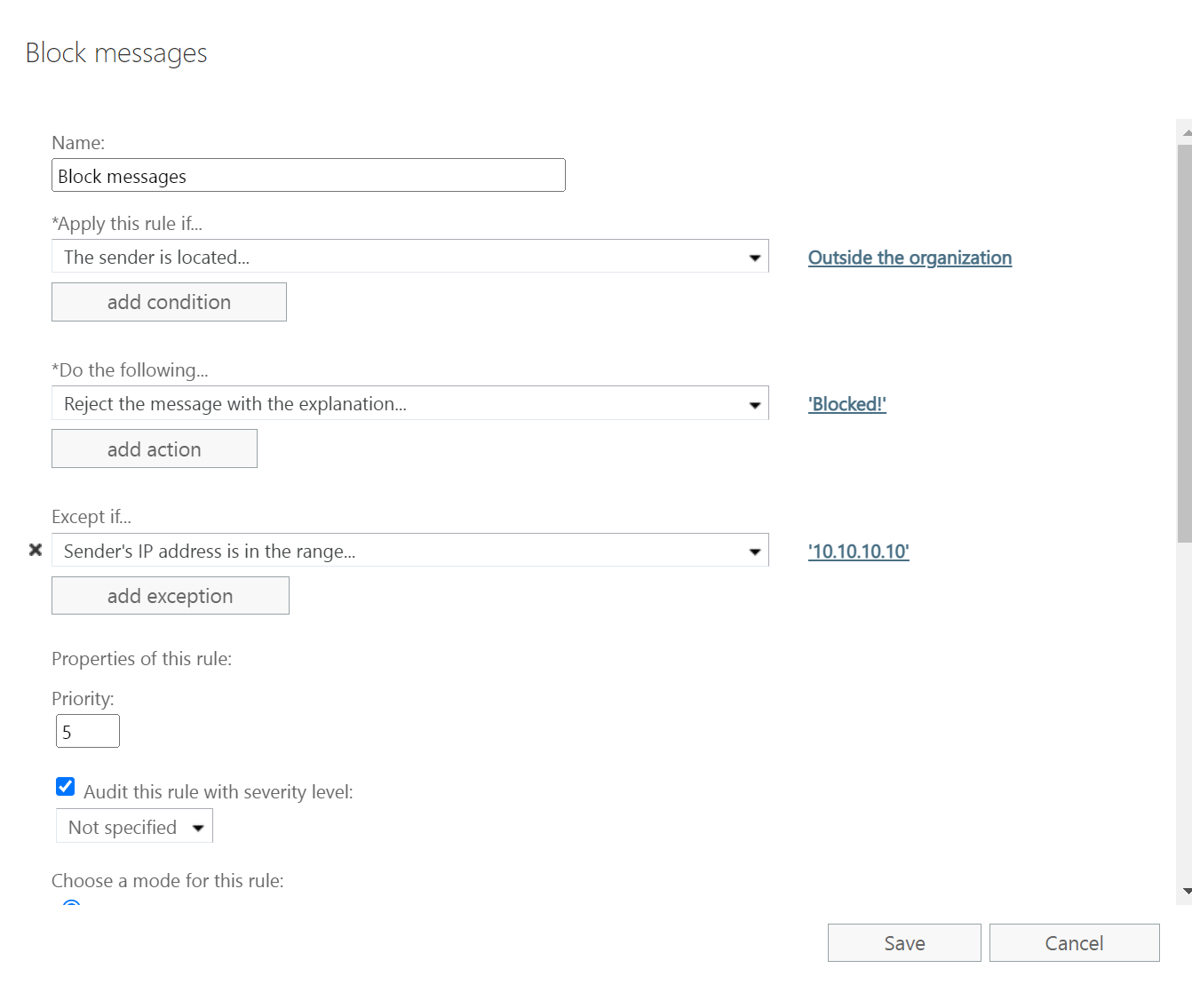
Use a transport rule and drop all messages from external users unless they come from the External IPs you allow
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.

Hi,
One of the clients uses Exchange hybrid with Exchange Server 2016. All mailboxes are in the cloud. Exchange Server 2016 basically runs in the default configuration. Only an additional anonymous relay has been created to allow a couple of local and few external IP addresses to send anonymous mail.
But recently we found out that anyone from the internet can connect to port 25 via telnet and send anonymous mail to our only accepted domain. Mail cannot be sent to unaccepted domain. We have SPF, DKIM, and DMARC configured for our domain, but these anonymous emails still gets through. After examining one of the mails we received, we found that the client_hostname shows the name of our Exchange server, but the original_client_ip shows the original IP address from which the connection to port 25 was made.
How can we deny these anonymous connections from the internet to port 25, but continue to allow from those IP addresses specified in the anonymous relay connector? Our domain MX records points to Microsoft servers.
Thanks!

Use a transport rule and drop all messages from external users unless they come from the External IPs you allow
I have similar issue our users are 50% o365 and 50% on-prem in hybrid setup with exchange 2016+edge server. pentesting guys found out that they can send emails via telnet our public ip. Shall i follow same steps to block it?