AZure web apps disable remote debugging ports
Hi everybody,
I'm searching for disabling remote debugging ports (nmap discover that 4022/4024 opened ports : Discovered open port 4024/tcp on x.x.x.x ... )
I've already disabled that with 'Remote debugging' as disabled in my web apps, so how could I really closes these ports?
Is it a bug from Azure administration?
Thank you.
Azure App Service
-
 VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee
VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee2022-09-12T11:19:50.843+00:00 @Jeff@KPS Thank you for reaching out to Microsoft Q&A. If your App Service is hosted on shared tenant environment, it is not possible to block specific ports because of the nature of the infrastructure. TCP ports 4022,4024 also might be open for Visual Studio remote debugging.
In [App Service Environment] (https://learn.microsoft.com/en-us/azure/app-service/environment/app-service-app-service-environment-control-inbound-traffic), you have full control over inbound and outbound traffic. You can use Network Security Groups to restrict or block specific ports.
You can refer to similar discussion on MSDN here
Feel free to reach back to me if you have any further questions on this,
-
Jeff@KPS 11 Reputation points
2022-09-12T15:04:11.553+00:00 @VenkateshDodda-MSFT thank you for the replie.
In fact yes I would like get some help from the App Service Environment inbound / outboud controlling trafic.
Here my needs and actual configuration :
1 - Initially a web app (api), directly expose to web (I would like to close all remote debugging ports)
2 - I've created a Network_Security_Group
3 - I've created a VNet with a subnet, linked to the NSG above
4 - I've associated my webapp with the virtual network
5 - I've partially (for a moment) block the access to the web app with an error : SqlException No such host ... So I added DNS outbound rule, it worked but after I realized this rule was not used, and evrything was fine .... Stange6 - Finally, I've created App Service Environment since I read some stuff on it (trough your link : app-service-app-service-environment-control-inbound-traffic but actually 'App Service Management ' still in process
In background, I always trying to check if these ports are closed but always the same : Discovered open port 4022+4024/tcp on x.x.x.x ...
What I'm doing wrong, in the wrong way to keep web access ...? Does the virtual network is built to do this?
How resume easily the thing to do in order to block these ports and keep same access, eventually filtering some incoming ip's ?Thanks.
-
 VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee
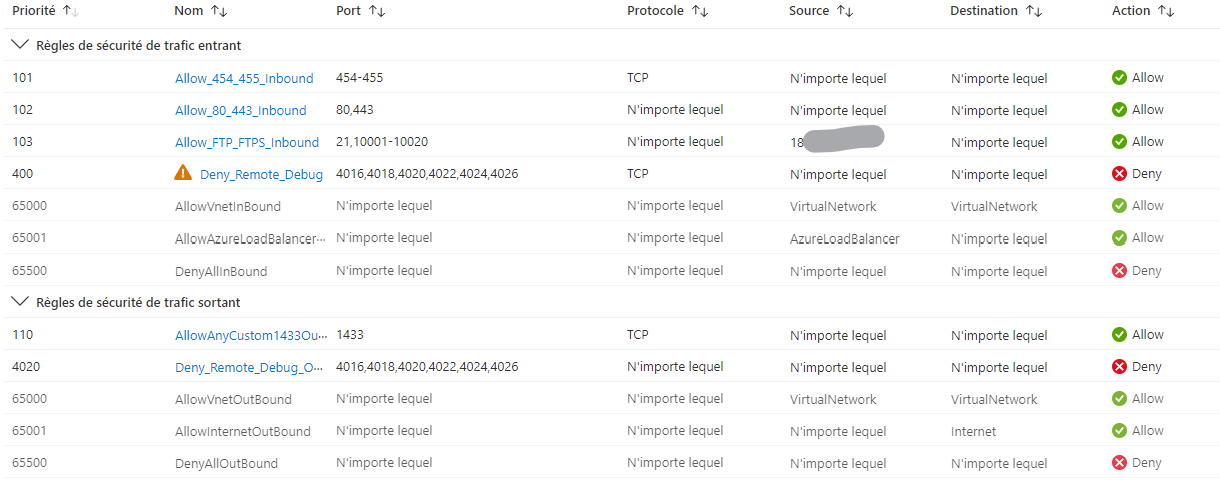
VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee2022-09-13T11:41:41.723+00:00 @Jeff@KPS Thanks for your response. Based on the above shared information I understood that you have created an ASE with webapp and NSG rule to ASE subnet Is that NSG rule created for inbound direction to block those ports 4022 and 4024? and also help us with NSG rules that were created.
How resume easily the thing to do in order to block these ports and keep same access, eventually filtering some incoming ip's ? --> Could you please let us know what exactly you are trying to accomplish/describe more about your requirement.
-
Jeff@KPS 11 Reputation points
2022-09-14T11:09:29.7+00:00 To resume the requirement : our goal is to close opened port (4022,4024..) found with a free testing tool like 'NMap':
I want to do this with a deployed web application on our Azure Tenant, but I read in your response and here that we cannot close these ports as Azure Web Apps are multi tenant environment by design.
So, in your mind, you was talking about App Service Environment, and rules managed by NSG.
From my side, I created some things like :
- VNet : I'm not sure we need this because, we need to give web access trough the xxxx.azurewebsites.net to our customer
- Network_Security_Group :
- App Service Environment : how affect an application to this ?
I don't really know how assemble all of these...
Could you provide me each steps or a link to a tutorial ?
Also, I'm seeing ASE deployments need to be done in a isolated plan (expensive), so what could best value for money between ASE or Azure WAF to block 2 opened ports for a public web application?
Thank you very much.
-
 VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee
VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee2022-09-15T12:07:14.65+00:00 @Jeff@KPS Thanks for your response. In your earlier response you have mentioned even remote debugging on the app service is disabled your NMAP results are showing that particular ports 4022 or 4024 are discovered can you check whether are you able to connect to those discovered ports? and also are you running the NMAP from local machine.
To test this behavior, I have created a webapp and disabled the remote debugging and tried running the NMAP scan from the local machine even the remote debugging is enabled or disabled i am not able to see those ports are getting discovered in the NMAP.
-
Jeff@KPS 11 Reputation points
2022-09-15T12:57:07.67+00:00 @VenkateshDodda-MSFT yes I'm running NMap from my local machine, and whatever if I check 'Disable Remote Debugging' from my webApp, these ports are getting discovered...
I'have not trie to connect really, my problem is for a pentest, where report list showing these port as 'opened' and may be a potential problem, the reason why I need to close these ones. -
 VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee
VenkateshDodda-MSFT 18,771 Reputation points • Microsoft Employee2022-09-16T09:48:52.41+00:00 @Jeff@KPS Thanks for your reply. This would need one on one offline support, for deeper investigations and might need to engage product team as well and I will suggest you open a support ticket to assist further and to investigate as well.
Sign in to comment