Hi @Liam Jones ,
You can set up a group for this kind of accounts that create a Conditional Access policy that block access to all cloud apps for that group:
And then you can add the needed account(s) to that group.
Hope this helps!
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.

Hi all,
I work for an MSSP and we have clients whereby we cannot access their on-premises infrastructure.
When we lock accounts out via Azure Active Directory, the Azure AD-Connect sync enables them after it syncs from the on-premises Active Directory. As I mentioned we have no access to their on-prem to block the accounts in AD and going through their internal IT team would be a nightmare.
I am just wondering what would the best solution to this problem be? I've read up on filtering but I think I am correct in thinkning that doesn't filter what attributes to sync but what accounts to sync.
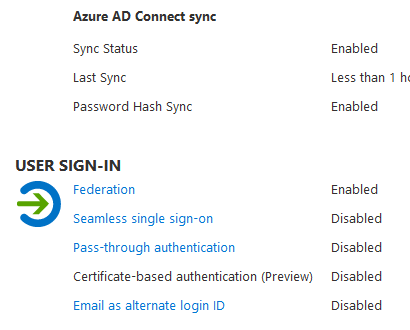
Here are the current settings for AD Connect:
Any help greatly appreciated. Thank you in advance!
Hi @Liam Jones ,
You can set up a group for this kind of accounts that create a Conditional Access policy that block access to all cloud apps for that group:
And then you can add the needed account(s) to that group.
Hope this helps!
Hello there,
There is no bi-directional sync, you will have to block in on-premises. This is by design.
For example if an account is disabled on-premise, the status will be synced to AAD to prevent logins, but if an account is disabled in AAD, the next sync between on-premise and cloud will re-enable to account in AAD, restoring sign-in access for the account.
-------------------------------------------------------------------------------------------------------------------------
--If the reply is helpful, please Upvote and Accept it as an answer--