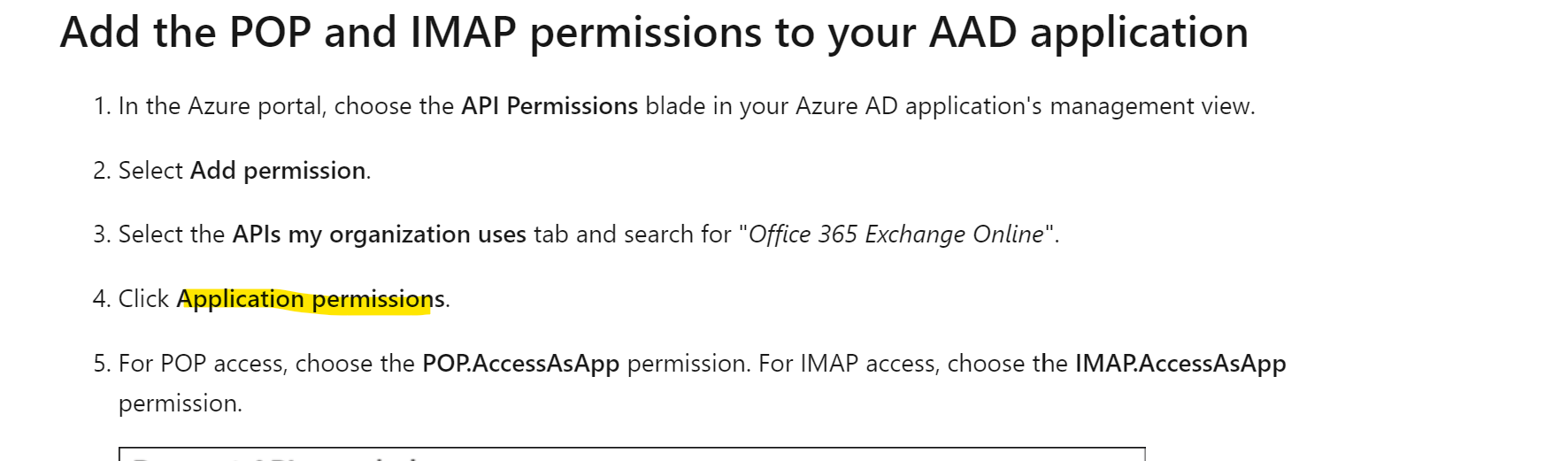
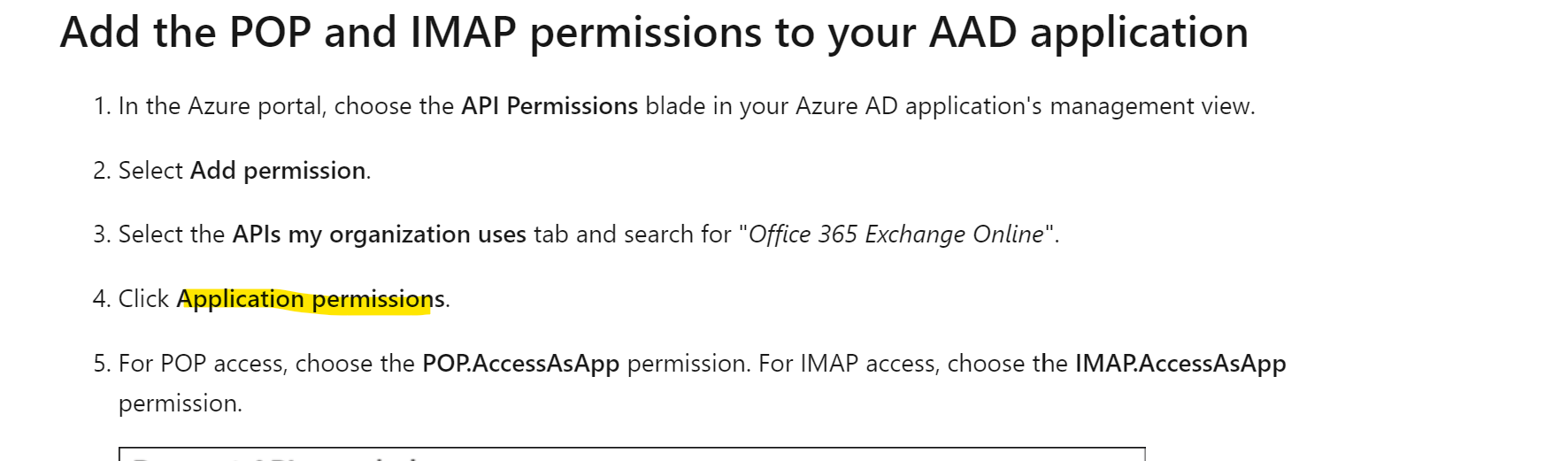
Per that doc, perms are application, not delegated as in your picture:
Also make sure you register it as service principal in Exo:
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Hi.
I have a windows service application (it irrelevant) which access user email box (for sending and receiving mails - IMAP/POP3 + SMTP).
To make it work with MS email account (Exchange, Outlook) I have created "App registrations" with "API permissions" from "Microsoft Graph":
IMAP.AccessAsUser.All POP.AccessAsUser.All SMTP.Send 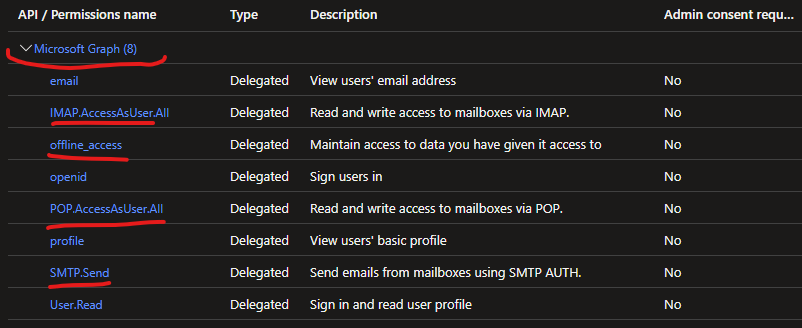
Authentication is done by "OAuth2 authorization code flow" https://learn.microsoft.com/en-us/exchange/client-developer/legacy-protocols/how-to-authenticate-an-imap-pop-smtp-application-by-using-oauth
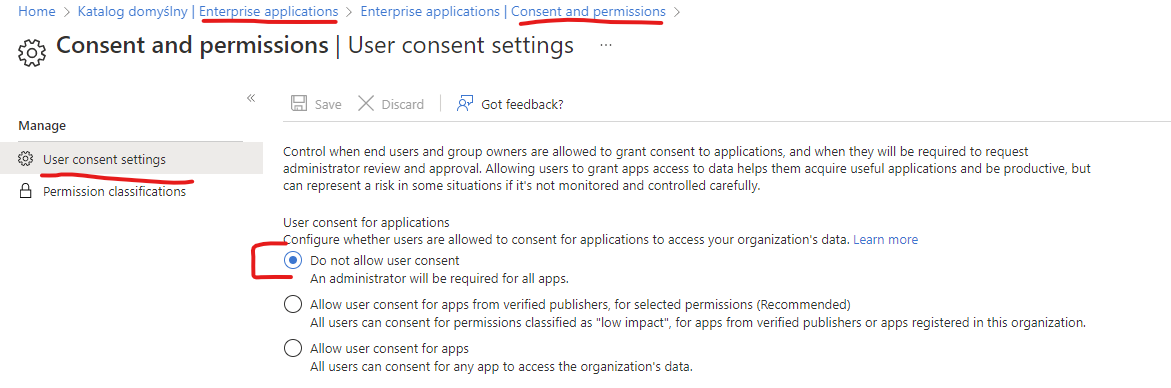
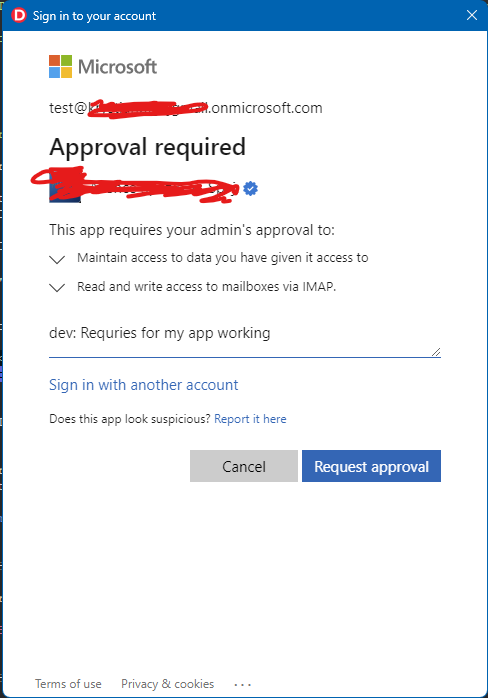
and work fine unless end-user tenant have change option to "Do not allow user consent":
Even when administrator approves consent:
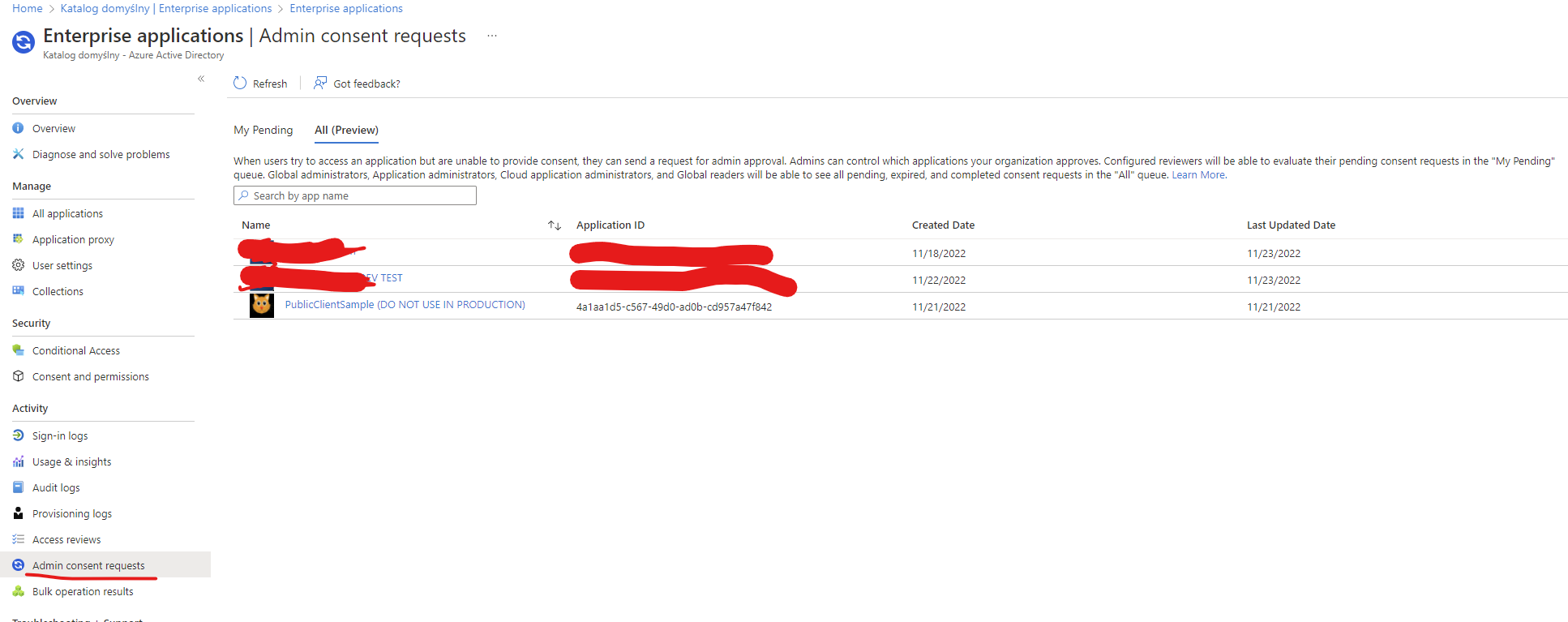
user every time backs to that admin consent window:
Scope for authorization is: offline_access https://outlook.office365.com/IMAP.AccessAsUser.All
If the scope is: offline_access https://graph.microsoft.com/IMAP.AccessAsUser.All the there is no admin-consent-loop (once tenant admin approves application, then authorization doesn't ask for admin approve), however then IMAP/POP/SMTP connection fails with authentication errors (like NO AUTHENTICATE failed.)
Any hint or ideas? Thanks.

Per that doc, perms are application, not delegated as in your picture:
Also make sure you register it as service principal in Exo: