It sounds like you might be having this problem because you are using the personal account. Even though the personal account is present in your AAD tenant, it still remains a personal account only and there are some limitations around it. You may need to use a work or school account instead.
A brief description of the difference between Work & School accounts (Organizational accounts) and Microsoft Accounts (Personal Accounts):
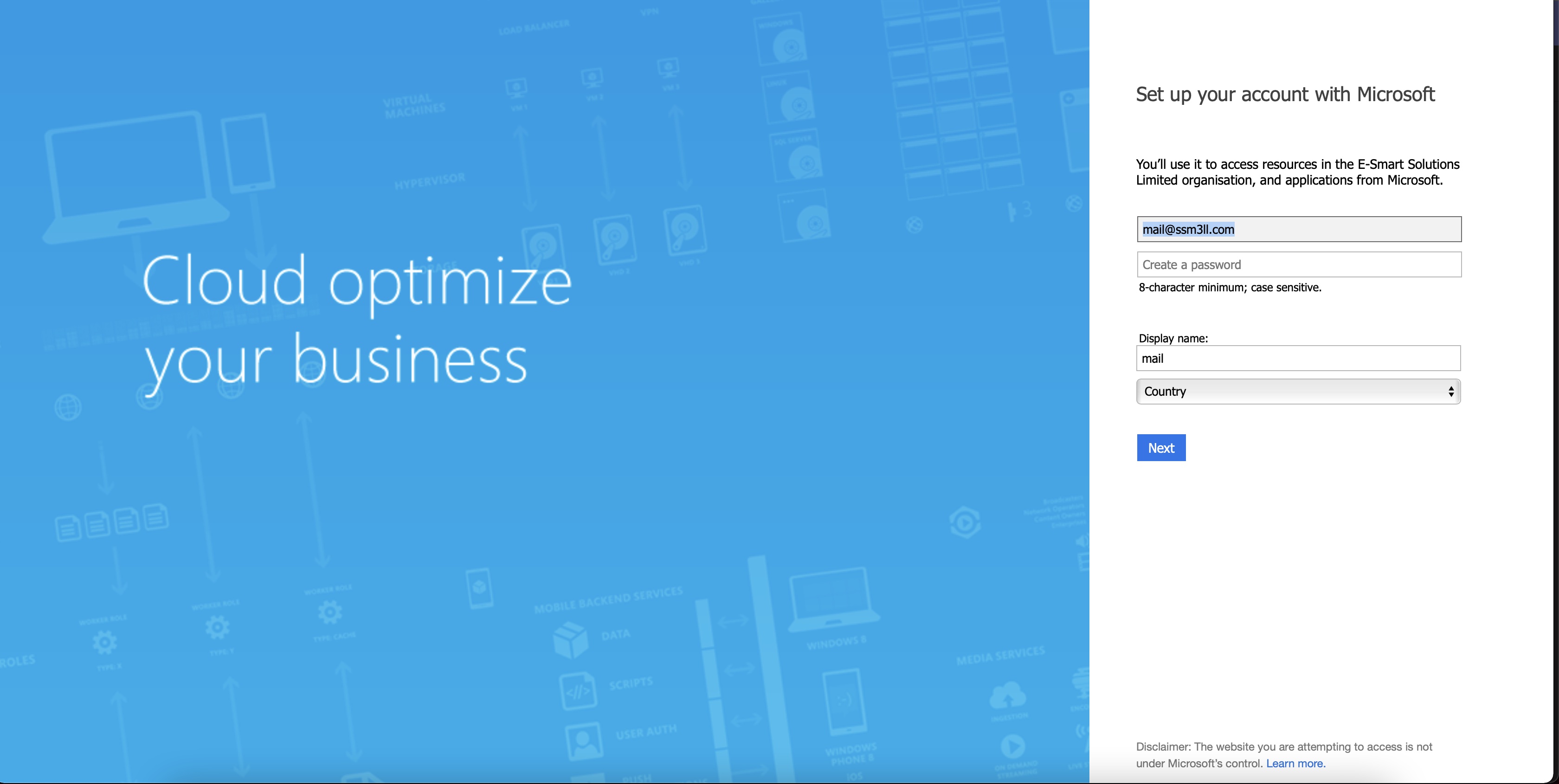
A work or school account is an identity created through Azure Active Directory or another Microsoft cloud service, such as Microsoft 365. A work account typically uses an organization’s custom domain name or company name, such as jon@Company portal .com. These are created by an organization’s administrator to enable a member of the organisation access to Microsoft cloud services such as Microsoft Azure, Microsoft Intune or Microsoft 365.
A Microsoft account (MSA) is an account created by a user for personal use and is the new name for what used to be called “Windows Live ID”. The Microsoft account is the combination of an email address and a password that a user uses to sign in to all consumer-oriented Microsoft products and cloud services such as Outlook (Hotmail), Messenger, OneDrive, MSN or Xbox LIVE. Your Microsoft account is created and stored in the Microsoft consumer identity account system that is run by Microsoft.
Several AAD Services strictly require work or school account (aka Organizational Accounts) to work with, and it's possible that this is the case here. I would suggest that the admin creates a user in the AAD Tenant and once the user gets created, you will find that you have the userPrincipalName set as "user1@yourTenantName.onmicrosoft.com" and can access the tenant.