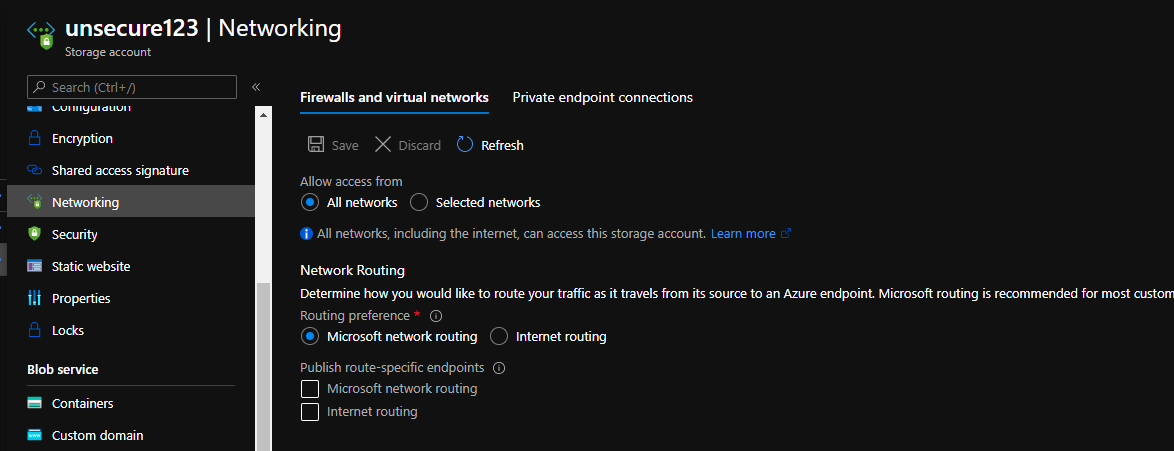
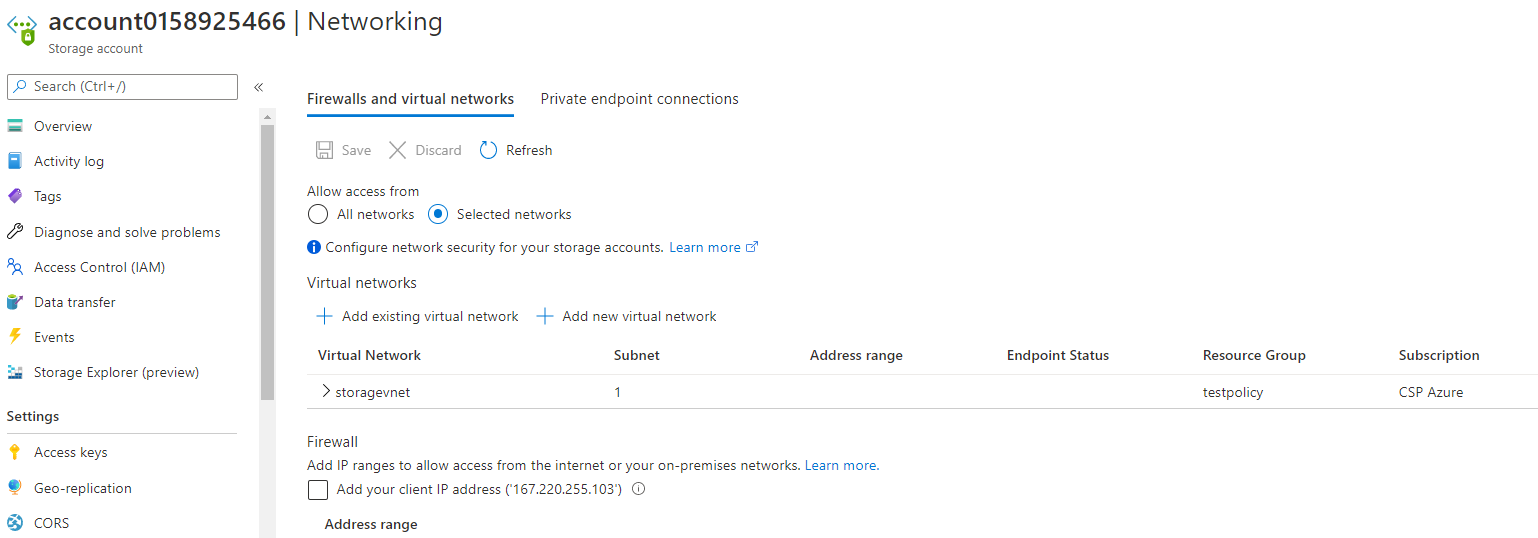
So I made some progress, but what is happening now is the unsecure storage accounts I am trying to remediate are being marked as compliant by the remeidation policy but its not changing anything but saying its secure. So I am thinking something could be backwards not quite sure yet. Below is my updated code:
{
"properties": {
"displayName": "2nd Attempt At STG Remediation",
"policyType": "Custom",
"mode": "All",
"metadata": {
"category": "Storage",
"createdBy": "0ab1a11f-97b1-4515-937b-0714f36c5bfe",
"createdOn": "2021-02-09T17:58:39.5407427Z",
"updatedBy": null,
"updatedOn": null
},
"parameters": {
"effect": {
"type": "String",
"metadata": {
"displayName": "Effect",
"description": "Enable or disable the execution of the policy"
},
"allowedValues": [
"DeployIfNotExists",
"Disabled"
],
"defaultValue": "DeployIfNotExists"
},
"subnetRssId": {
"type": "String",
"metadata": {
"displayName": "Azure Subnet Resource Id",
"description": "The subnet resource id to add to access rules"
}
}
},
"policyRule": {
"if": {
"allOf": [
{
"field": "type",
"equals": "Microsoft.Storage/storageAccounts"
},
{
"field": "Microsoft.Storage/storageAccounts/networkAcls.defaultAction",
"notEquals": "Deny"
}
]
},
"then": {
"effect": "[parameters('effect')]",
"details": {
"type": "Microsoft.Storage/storageAccounts",
"roleDefinitionIds": [
"/providers/Microsoft.Authorization/roleDefinitions/b24988ac-6180-42a0-ab88-20f7382dd24c"
],
"existenceCondition": {
"field": "Microsoft.Storage/storageAccounts/networkAcls.defaultAction",
"equals": "Deny"
},
"deployment": {
"properties": {
"mode": "incremental",
"template": {
"$schema": "https://schema.management.azure.com/schemas/2019-04-01/deploymentTemplate.json#",
"contentVersion": "1.0.0.0",
"parameters": {
"name": {
"type": "string"
},
"sku": {
"type": "string"
},
"kind": {
"type": "string"
},
"location": {
"type": "string"
},
"subnetRssId": {
"type": "string"
}
},
"resources": [
{
"name": "[parameters('name')]",
"type": "Microsoft.Storage/storageAccounts",
"apiVersion": "2019-06-01",
"location": "[parameters('location')]",
"properties": {
"networkAcls": {
"bypass": "AzureServices",
"virtualNetworkRules": [
{
"id": "[parameters('subnetRssId')]",
"action": "Allow"
}
],
"ipRules": [],
"defaultAction": "Deny"
}
},
"dependsOn": [],
"sku": {
"name": "[parameters('sku')]"
},
"kind": "[parameters('kind')]"
}
]
},
"parameters": {
"name": {
"value": "[field('name')]"
},
"sku": {
"value": "[field('Microsoft.Storage/storageAccounts/sku.name')]"
},
"location": {
"value": "[field('location')]"
},
"kind": {
"value": "[field('kind')]"
},
"subnetRssId": {
"value": "[parameters('subnetRssId')]"
}
}
}
}
}
}
}
},
"id": "/subscriptions/58ea3f61-3761-430f-8b7b-5869717c74e8/providers/Microsoft.Authorization/policyDefinitions/3426f245-86db-4ea7-935f-30b5011df9cd",
"type": "Microsoft.Authorization/policyDefinitions",
"name": "3426f245-86db-4ea7-935f-30b5011df9cd"
}