I have an internal ASEv3 provisioned into my VNet. An App Service deployed in the ASEv3 needs to pull the container-image from an ACR in the same VNet. The ACR has disabled all public network access and uses a private endpoint for communication. The App Service tries to pull the docker-image over the public outbound IP address of the ASE which results in the following error-message inside the "Deployment Center - Logs" of my App Service:
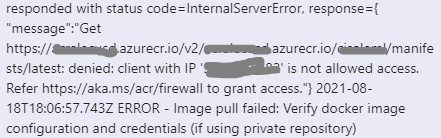
ERROR - DockerApiException: Docker API responded with status code=InternalServerError, response={"message":"Get https://myregistryxxxyyy.azurecr.io/v2/my-app/manifests/2021.1.7-appinsightsx: denied: client with IP '20.xx.xxx.xx' is not allowed access. Refer https://aka.ms/acr/firewall to grant access."}
My current workaround is to allow this public IP inside the firewall settings of the ACR.
But how can I tell the App Service to communicate over my VNet only? I already set the env-variables WEBSITE_VNET_ROUTE_ALL=1 and WEBSITE_PULL_IMAGE_OVER_VNET=true.