Do you have any web developers on your team?
At my former employer, I developed several web sites to allow "plain old users" to perform administrative tasks. These were VB.Net ASPX pages. The site was set to authenticate, but NOT impersonate the client to get the user's ID. It then checked to see if the user was a member of other Active Directory groups (like a ServiceDesk group). Based on their group membership, they were presented with a menu of functions that they were allowed to do.
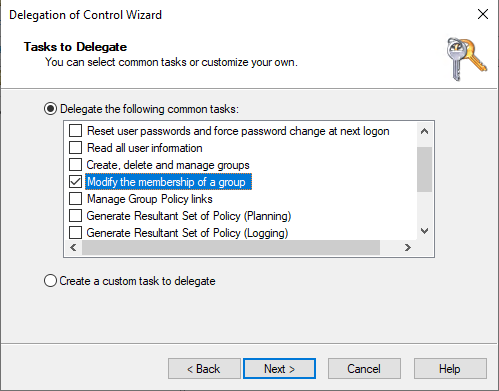
The trick is to set the IIS worker process to run as some AD account that has rights to add/remove users from groups. The code in the ASPX page manages which groups can be manipulated. In this manner you could have users listed in ServiceDesk-East manage one set of AD groups, and users listed in ServiceDesk-West to manage another set.
The ServiceDesk users themselves have no right within AD, the IIS application pool serves as a proxy and it has the right to manage any group.
In another case I had application developers that needed to stop and start Windows services. But I could not give them administrative access to the server. In that instance I used local groups on the app server, and set the IIS worker process to run as SYSTEM.
You'll have the pain of doing the initial development and testing, but once you have it working, you can clone it and "front end" other administrative functions.