Hi @Jack Grub ,
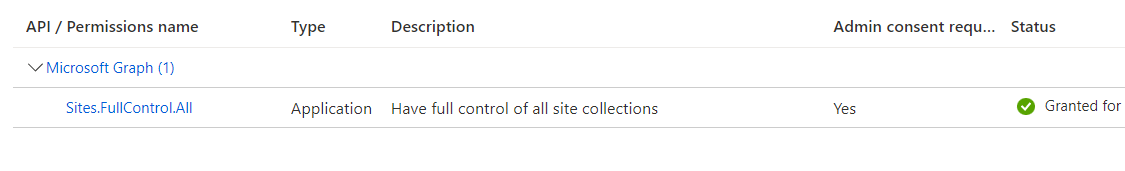
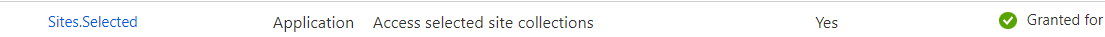
Microsoft Graph exposes application permissions for apps that call Microsoft Graph under their own identity. Application permissions are used by apps that run without a signed-in user present. Hence it is not possible to restrict Microsoft Graph application permission to one specific user account only. Please note that application permisions are full level permisions are granted to you app registred in Azure AD.
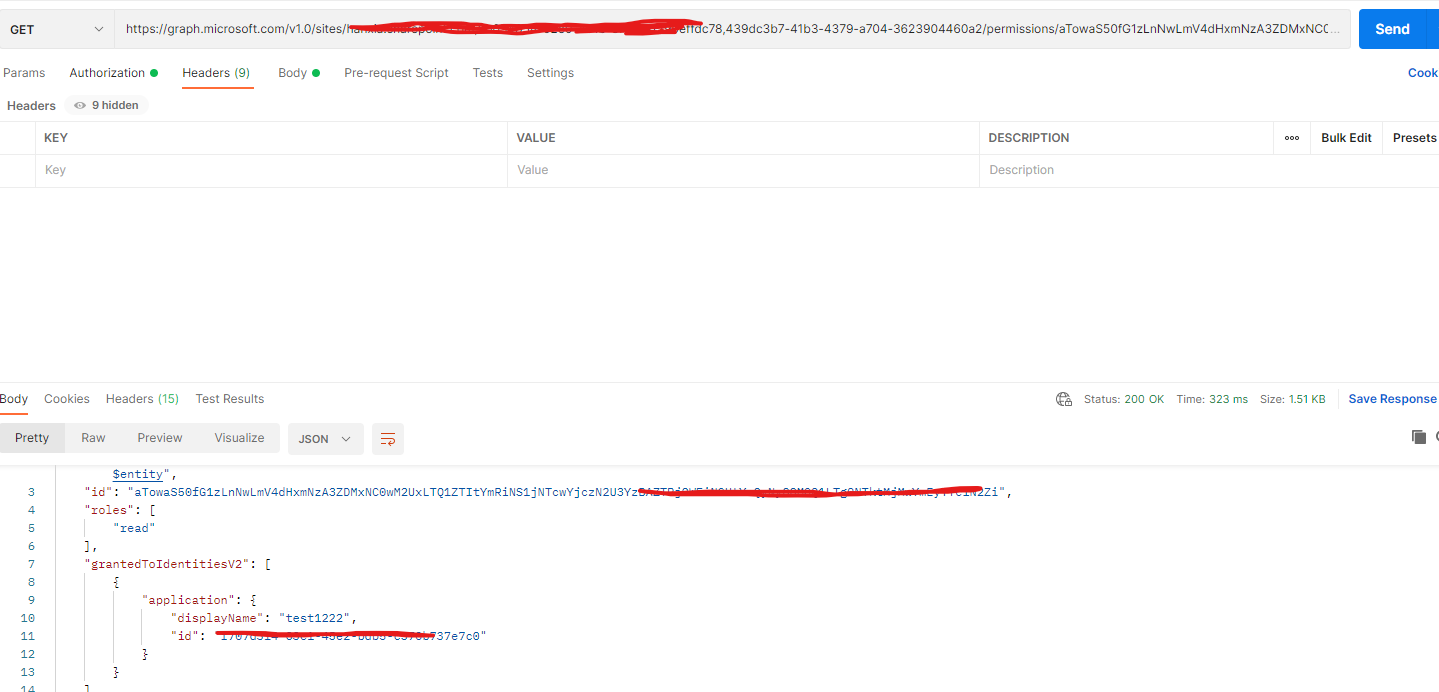
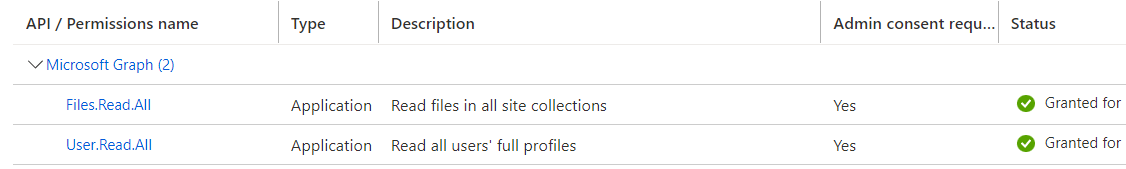
For application permissions, the effective permissions of your app are the full level of privileges implied by the permission. For example, an app that has the Files.Read.All application permission can gets the files from any user's OneDrive files in the organization.
For delegated permissions, the effective permissions of your app are the least-privileged intersection of the delegated permissions the app has been granted (by consent) and the privileges of the currently signed-in user. Your app can never have more privileges than the signed-in user. For example, an app that has the Files.Read.All delegated permission only can read all files the signed-in user have access to.
References :
https://learn.microsoft.com/en-us/graph/auth/auth-concepts#effective-permissions-in-delegated-vs-application-only-permission-scenarios
Hope this helps.
If the answer is helpful to you, please click "Accept Answer" and kindly upvote it. If you have additional questions about this answer, please click "Comment".