إشعار
يتطلب الوصول إلى هذه الصفحة تخويلاً. يمكنك محاولة تسجيل الدخول أو تغيير الدلائل.
يتطلب الوصول إلى هذه الصفحة تخويلاً. يمكنك محاولة تغيير الدلائل.
This article explains how to migrate from traditional authentication methods to more secure, passwordless connections with Azure SQL Database.
Application requests to Azure SQL Database must be authenticated. Azure SQL Database provides several different ways for apps to connect securely. One of the ways is to use passwords. However, you should prioritize passwordless connections in your applications when possible.
Compare authentication options
When the application authenticates with Azure SQL Database, it provides a username and password pair to connect to the database. Depending on where the identities are stored, there are two types of authentication: Microsoft Entra authentication and Azure SQL Database authentication.
Microsoft Entra authentication
Microsoft Entra authentication is a mechanism for connecting to Azure SQL Database using identities defined in Microsoft Entra ID. With Microsoft Entra authentication, you can manage database user identities and other Microsoft services in a central location, which simplifies permission management.
Using Microsoft Entra ID for authentication provides the following benefits:
- Authentication of users across Azure Services in a uniform way.
- Management of password policies and password rotation in a single place.
- Multiple forms of authentication supported by Microsoft Entra ID, which can eliminate the need to store passwords.
- Customers can manage database permissions using external (Microsoft Entra ID) groups.
- Microsoft Entra authentication uses Azure SQL database users to authenticate identities at the database level.
- Support of token-based authentication for applications connecting to Azure SQL Database.
Azure SQL Database authentication
You can create accounts in Azure SQL Database. If you choose to use passwords as credentials for the accounts, these credentials will be stored in the sys.database_principals table. Because these passwords are stored in Azure SQL Database, you need to manage the rotation of the passwords by yourself.
Although it's possible to connect to Azure SQL Database with passwords, you should use them with caution. You must be diligent to never expose the passwords in an unsecure location. Anyone who gains access to the passwords is able to authenticate. For example, there's a risk that a malicious user can access the application if a connection string is accidentally checked into source control, sent through an unsecure email, pasted into the wrong chat, or viewed by someone who shouldn't have permission. Instead, consider updating your application to use passwordless connections.
Introducing passwordless connections
With a passwordless connection, you can connect to Azure services without storing any credentials in the application code, its configuration files, or in environment variables.
Many Azure services support passwordless connections, for example via Azure Managed Identity. These techniques provide robust security features that you can implement using DefaultAzureCredential from the Azure Identity client libraries. In this tutorial, you'll learn how to update an existing application to use DefaultAzureCredential instead of alternatives such as connection strings.
DefaultAzureCredential supports multiple authentication methods and automatically determines which should be used at runtime. This approach enables your app to use different authentication methods in different environments (local dev vs. production) without implementing environment-specific code.
The order and locations in which DefaultAzureCredential searches for credentials can be found in the Azure Identity library overview. For example, when working locally, DefaultAzureCredential will generally authenticate using the account the developer used to sign in to Visual Studio. When the app is deployed to Azure, DefaultAzureCredential will automatically switch to use a managed identity. No code changes are required for this transition.
To ensure that connections are passwordless, you must take into consideration both local development and the production environment. If a connection string is required in either place, then the application isn't passwordless.
In your local development environment, you can authenticate with Azure CLI, Azure PowerShell, Visual Studio, or Azure plugins for Visual Studio Code or IntelliJ. In this case, you can use that credential in your application instead of configuring properties.
When you deploy applications to an Azure hosting environment, such as a virtual machine, you can assign managed identity in that environment. Then, you won't need to provide credentials to connect to Azure services.
Note
A managed identity provides a security identity to represent an app or service. The identity is managed by the Azure platform and does not require you to provision or rotate any secrets. You can read more about managed identities in the overview documentation.
Note
Since the JDBC driver for Azure SQL Database doesn't support passwordless connections from local environments yet, this article will focus only on applications deployed to Azure hosting environments and how to migrate them to use passwordless connections.
Migrate an existing application to use passwordless connections
The following steps explain how to migrate an existing application to use passwordless connections instead of a password-based solution.
0) Prepare the working environment
First, use the following command to set up some environment variables.
export AZ_RESOURCE_GROUP=<YOUR_RESOURCE_GROUP>
export AZ_DATABASE_SERVER_NAME=<YOUR_DATABASE_SERVER_NAME>
export AZ_DATABASE_NAME=demo
export CURRENT_USERNAME=$(az ad signed-in-user show --query userPrincipalName --output tsv)
export CURRENT_USER_OBJECTID=$(az ad signed-in-user show --query id --output tsv)
Replace the placeholders with the following values, which are used throughout this article:
<YOUR_RESOURCE_GROUP>: The name of the resource group your resources are in.<YOUR_DATABASE_SERVER_NAME>: The name of your Azure SQL Database server. It should be unique across Azure.
1) Configure Azure SQL Database
1.1) Enable Microsoft Entra ID-based authentication
To use Microsoft Entra ID access with Azure SQL Database, you should set the Microsoft Entra admin user first. Only a Microsoft Entra Admin user can create/enable users for Microsoft Entra ID-based authentication.
If you're using Azure CLI, run the following command to make sure it has sufficient permission:
az login --scope https://graph.microsoft.com/.default
Then, run following command to set the Microsoft Entra admin:
az sql server ad-admin create \
--resource-group $AZ_RESOURCE_GROUP \
--server $AZ_DATABASE_SERVER_NAME \
--display-name $CURRENT_USERNAME \
--object-id $CURRENT_USER_OBJECTID
This command will set the Microsoft Entra admin to the current signed-in user.
Note
You can only create one Microsoft Entra admin per Azure SQL Database server. Selection of another one will overwrite the existing Microsoft Entra admin configured for the server.
2) Migrate the app code to use passwordless connections
Next, use the following steps to update your code to use passwordless connections. Although conceptually similar, each language uses different implementation details.
Inside your project, add the following reference to the
azure-identitypackage. This library contains all of the entities necessary to implement passwordless connections.<dependency> <groupId>com.azure</groupId> <artifactId>azure-identity</artifactId> <version>1.5.4</version> </dependency>Enable the Microsoft Entra managed identity authentication in the JDBC URL.v Identify the locations in your code that currently create a
java.sql.Connectionto connect to Azure SQL Database. Update your code to match the following example:String url = "jdbc:sqlserver://$AZ_DATABASE_SERVER_NAME.database.windows.net:1433;databaseName=$AZ_DATABASE_NAME;authentication=ActiveDirectoryMSI;" Connection con = DriverManager.getConnection(url);Replace the two
$AZ_DATABASE_SERVER_NAMEvariables and one$AZ_DATABASE_NAMEvariable with the values that you configured at the beginning of this article.Remove the
userandpasswordfrom the JDBC URL.
3) Configure the Azure hosting environment
After your application is configured to use passwordless connections, the same code can authenticate to Azure services after it's deployed to Azure. For example, an application deployed to an Azure App Service instance that has a managed identity assigned can connect to Azure Storage.
In this section, you'll execute two steps to enable your application to run in an Azure hosting environment in a passwordless way:
- Assign the managed identity for your Azure hosting environment.
- Assign roles to the managed identity.
Note
Azure also provides Service Connector, which can help you connect your hosting service with SQL server. With Service Connector to configure your hosting environment, you can omit the step of assigning roles to your managed identity because Service Connector will do it for you. The following section describes how to configure your Azure hosting environment in two ways: one via Service Connector and the other by configuring each hosting environment directly.
Important
Service Connector's commands require Azure CLI 2.41.0 or higher.
Assign the managed identity using the Azure portal
The following steps show you how to assign a system-assigned managed identity for various web hosting services. The managed identity can securely connect to other Azure services using the app configurations you set up previously.
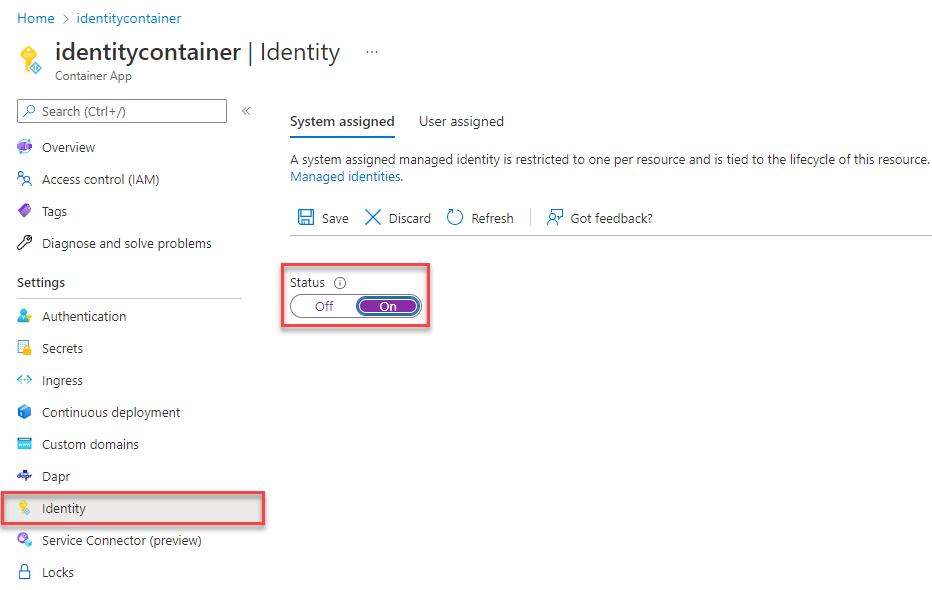
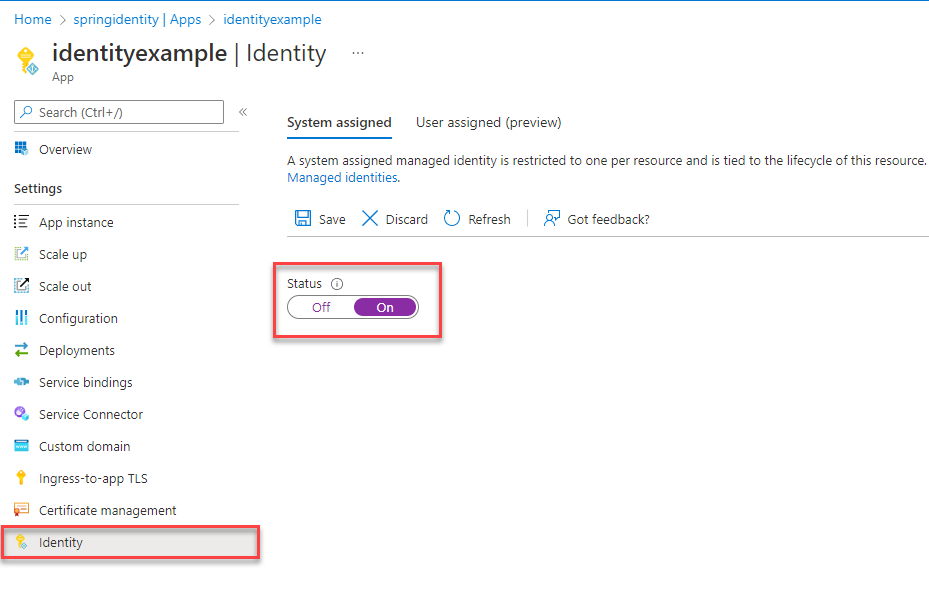
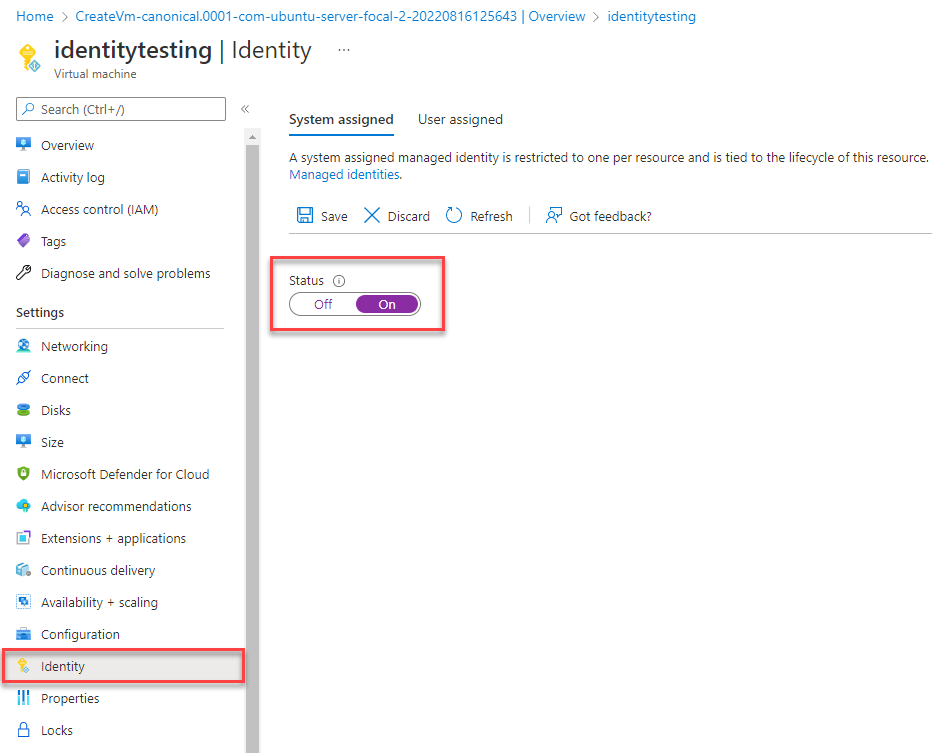
On the main overview page of your Azure App Service instance, select Identity from the navigation pane.
On the System assigned tab, make sure to set the Status field to on. A system assigned identity is managed by Azure internally and handles administrative tasks for you. The details and IDs of the identity are never exposed in your code.
You can also assign managed identity on an Azure hosting environment using the Azure CLI.
You can assign a managed identity to an Azure App Service instance with the az webapp identity assign command, as shown in the following example:
export AZ_MI_OBJECT_ID=$(az webapp identity assign \
--resource-group $AZ_RESOURCE_GROUP \
--name <service-instance-name> \
--query principalId \
--output tsv)
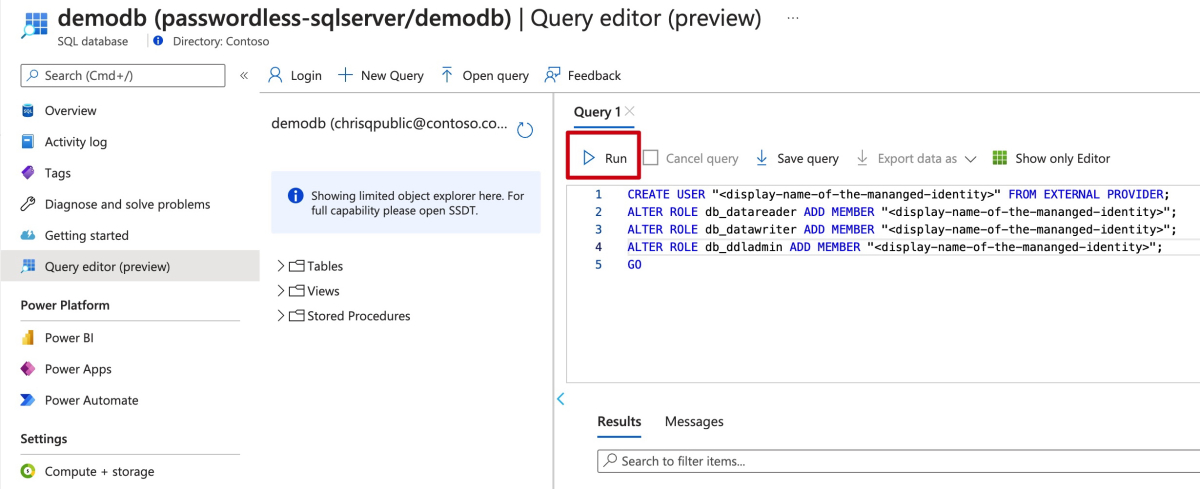
Assign roles to the managed identity
Next, grant permissions to the managed identity you created to access your SQL database.
If you connected your services using Service Connector, the previous step's commands already assigned the role, so you can skip this step.
Test the app
After making these code changes, you can build and redeploy the application. Then, browse to your hosted application in the browser. Your app should be able to connect to the Azure SQL database successfully. Keep in mind that it may take several minutes for the role assignments to propagate through your Azure environment. Your application is now configured to run both locally and in a production environment without the developers having to manage secrets in the application itself.
Next steps
In this tutorial, you learned how to migrate an application to passwordless connections.
You can read the following resources to explore the concepts discussed in this article in more depth: