Scenario - Using directory extensions with group provisioning to Active Directory
Scenario: You have hundreds of groups in Microsoft Entra ID. You want to provision some of these groups but not all back to Active Directory. You would like a quick filter that can be applied to groups without having to make a more complicated scoping filter.
You can use the environment you create in this scenario for testing or for getting more familiar with cloud sync.
Assumptions
- This scenario assumes that you already have a working environment that is synchronizing users to Microsoft Entra ID.
- We have 4 users that are synchronized. Britta Simon, Lola Jacobson, Anna Ringdahl, and John Smith.
- Three organizational Units have been created in Active Directory - Sales, Marketing, and Groups
- The Britta Simon and Anna Ringdahl user accounts reside in the Sales OU.
- The Lola Jacobson and John Smith user accounts reside in the Marketing OU.
- The Groups OU is where our groups from Microsoft Entra ID are provisioned.
Tip
For a better experience executing Microsoft Graph PowerShell SDK cmdlets, use Visual Studio Code with ms-vscode.powershell extension in ISE Mode.
Create two groups in Microsoft Entra ID
To begin, create two groups in Microsoft Entra ID. One group is Sales and the Other is Marketing.
To create two groups, follow these steps.
- Sign in to the Microsoft Entra admin center as at least a Hybrid Identity Administrator.
- Browse to Identity > Groups > All groups.
- At the top, click New group.
- Make sure the Group type is set to security.
- For the Group Name enter Sales
- For Membership type keep it at assigned.
- Click Create.
- Repeat this process using Marketing as the Group Name.
Add users to the newly created groups
- Sign in to the Microsoft Entra admin center as at least a Hybrid Identity Administrator.
- Browse to Identity > Groups > All groups.
- At the top, in the search box, enter Sales.
- Click on the new Sales group.
- On the left, click Members
- At the top, click Add members.
- At the top, in the search box, enter Britta Simon.
- Put a check next to Britta Simon and Anna Ringdahl and click Select
- It should successfully add her to the group.
- On the far left, click All groups and repeat this process using the Marketing group and adding Lola Jacobson and John Smith to that group.
Note
When adding users to the Marketing group, make note of the group ID on the overview page. This ID is used later to add our newly created property to the group.
Install and connect Microsoft Graph PowerShell SDK
If not yet installed, follow Microsoft Graph PowerShell SDK documentation to install the main modules of Microsoft Graph PowerShell SDK:
Microsoft.Graph.Open PowerShell with Administrative privileges
To set the execution policy, run (press [A] Yes to all when prompted):
Set-ExecutionPolicy -ExecutionPolicy RemoteSigned -Scope CurrentUserConnect to your tenant (Be sure to accept on-behalf of when signing in):
Connect-MgGraph -Scopes "Directory.ReadWrite.All", "Application.ReadWrite.All", "User.ReadWrite.All, Group.ReadWrite.All"
Create our CloudSyncCustomExtensionApp application and service principal
Important
Directory extension for Microsoft Entra Cloud Sync is only supported for applications with the identifier URI “api://<tenantId>/CloudSyncCustomExtensionsApp” and the Tenant Schema Extension App created by Microsoft Entra Connect.
Get the Tenant ID:
$tenantId = (Get-MgOrganization).Id $tenantId
Note
This will output our current Tenant ID. You can confirm this Tenant ID by navigating to Microsoft Entra admin center > Identity > Overview.
Using the
$tenantIdvariable from the previous step, check to see if the CloudSyncCustomExtensionApp exists.$cloudSyncCustomExtApp = Get-MgApplication -Filter "identifierUris/any(uri:uri eq 'api://$tenantId/CloudSyncCustomExtensionsApp')" $cloudSyncCustomExtAppIf a CloudSyncCustomExtensionApp exists, skip to the next step. Otherwise, create the new CloudSyncCustomExtensionApp app:
$cloudSyncCustomExtApp = New-MgApplication -DisplayName "CloudSyncCustomExtensionsApp" -IdentifierUris "api://$tenantId/CloudSyncCustomExtensionsApp" $cloudSyncCustomExtAppCheck if CloudSyncCustomExtensionsApp application has a security principal associated. If you just created a new app, skip to the next step.
Get-MgServicePrincipal -Filter "AppId eq '$($cloudSyncCustomExtApp.AppId)'"If you just created a new app or a security principal is not returned, create a security principal for CloudSyncCustomExtensionsApp:
New-MgServicePrincipal -AppId $cloudSyncCustomExtApp.AppId
Create our custom extension attribute
Tip
In this scenario we are going to create a custom extension attribute called WritebackEnabled to be used in Microsoft Entra Cloud Sync scoping filter, so that only groups with WritebackEnabled set to True are written back to On-premises Active Directory, similarly to the Writeback enabled flag in Microsoft Entra admin center.
Get the Tenant ID:
$tenantId = (Get-MgOrganization).Id $tenantIdGet the CloudSyncCustomExtensionsApp application:
$cloudSyncCustomExtApp = Get-MgApplication -Filter "identifierUris/any(uri:uri eq 'api://$tenantId/CloudSyncCustomExtensionsApp')"Now, under the CloudSyncCustomExtensionApp, create the custom extension attribute called "WritebackEnabled" and assign it to Group objects:
New-MgApplicationExtensionProperty -ApplicationId $cloudSyncCustomExtApp.Id -Name 'WritebackEnabled' -DataType 'Boolean' -TargetObjects 'Group'This cmdlet creates an extension attribute that looks like extension_<guid>_WritebackEnabled.
Create our cloud sync configuration
Sign in to the Microsoft Entra admin center as at least a Hybrid Identity Administrator.
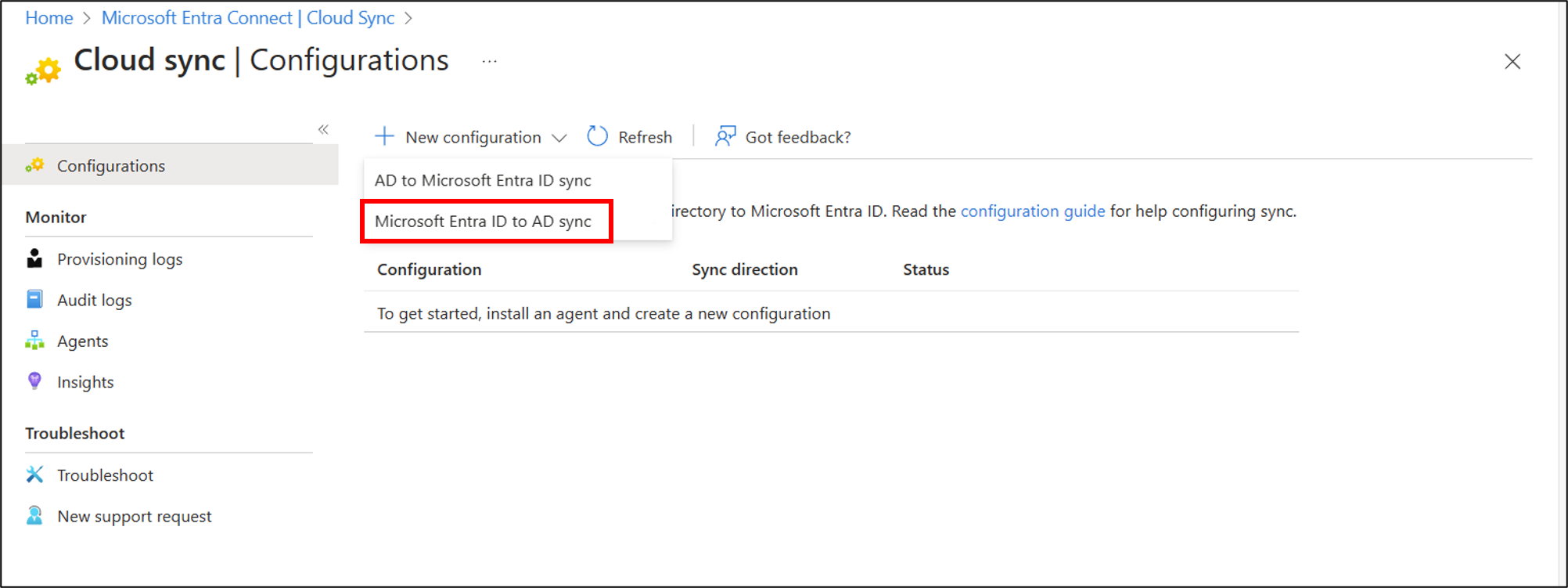
Browse to Identity > Hybrid Management > Microsoft Entra Connect > Cloud sync.
Select New configuration.
Select Microsoft Entra ID to AD sync.
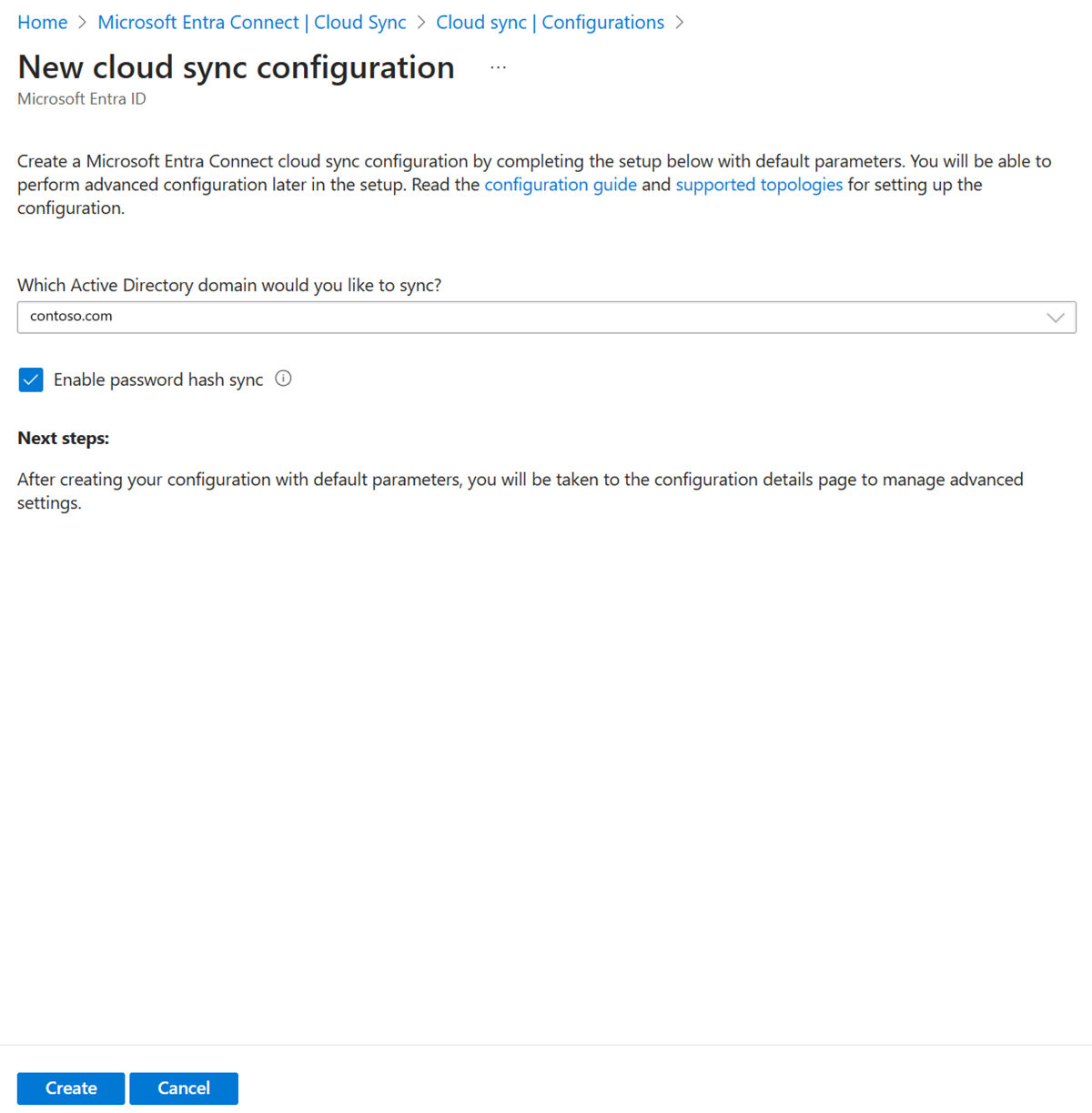
- On the configuration screen, select your domain and whether to enable password hash sync. Click Create.
The Get started screen opens. From here, you can continue configuring cloud sync
On the left, click Scoping filters select Group scope - All groups
Click Edit attribute mapping and change the Target Container to
OU=Groups,DC=Contoso,DC=com. Click Save.Click Add Attribute scoping filter
Type a name for the scoping filter:
Filter groups with Writeback EnabledUnder Target Attribute select the newly created attribute that looks like extension_<guid>_WritebackEnabled.
Important
Some of the target attributes displayed in the dropdown list might not be usable as a scoping filter because not all properties can be managed in Entra ID, for example extensionAttribute[1-15], hence the recommendation is to create a custom extension property for this specific purpose.

- Under Operator select IS TRUE
- Click Save. And click Save.
- Leave the configuration disabled and come back to it.
Add new extension property to one of our groups
For this portion, we're going add a value on our newly created property to one of our existing groups, Marketing.
Set the extension property value using Microsoft Graph PowerShell SDK
Get the Tenant ID:
$tenantId = (Get-MgOrganization).Id $tenantIdGet the CloudSyncCustomExtensionsApp application:
$cloudSyncCustomExtApp = Get-MgApplication -Filter "identifierUris/any(uri:uri eq 'api://$tenantId/CloudSyncCustomExtensionsApp')"Get our extension property:
$gwbEnabledExtAttrib = Get-MgApplicationExtensionProperty -ApplicationId $cloudSyncCustomExtApp.Id | Where-Object {$_.Name -Like '*WritebackEnabled'} | Select-Object -First 1 $gwbEnabledExtAttrib $gwbEnabledExtName = $gwbEnabledExtAttrib.NameNow, get the
Marketinggroup:$marketingGrp = Get-MgGroup -ConsistencyLevel eventual -Filter "DisplayName eq 'Marketing'" $marketingGrpThen, with the variable
$gwbEnabledExtNamecontainingextension_<guid>_WritebackEnabled, set the valueTruefor the Marketing group:Update-MgGroup -GroupId $marketingGrp.Id -AdditionalProperties @{$gwbEnabledExtName = $true}To confirm, you can read the
extension_<guid>_WritebackEnabledproperty value with:$marketingGrp = Get-MgGroup -ConsistencyLevel eventual -Filter "DisplayName eq 'Marketing'" -Property Id,$gwbEnabledExtName $marketingGrp.AdditionalProperties.$gwbEnabledExtName
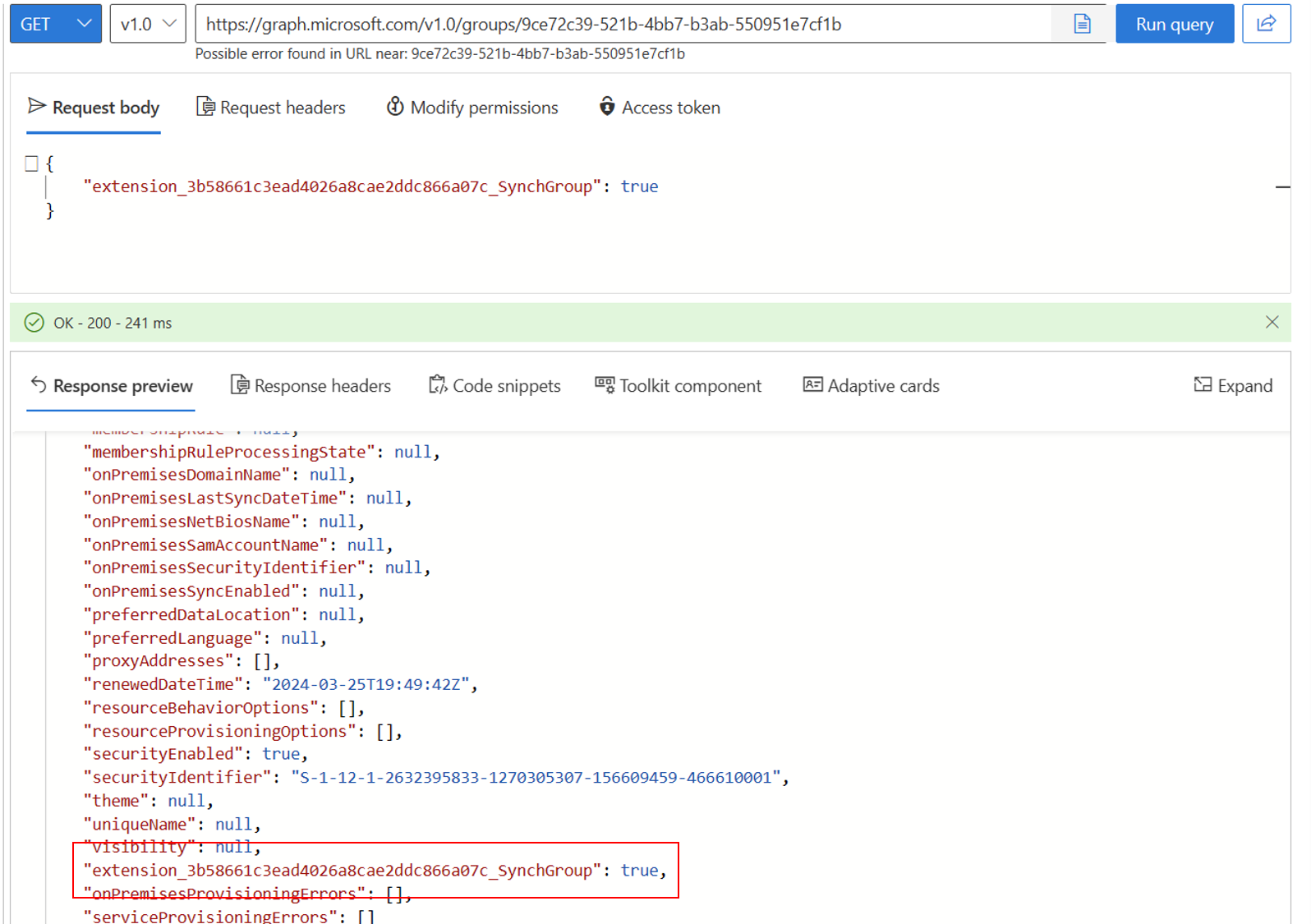
Set the extension property value using Microsoft Graph Explorer
You need to make sure that you have consented to Group.ReadWrite.All. You can do this by selecting Modify permissions.
Navigate to Microsoft Graph Explorer
Sign-in using your tenant administrator account. This may need to be a Hybrid Identity Administrator account. A Hybrid Identity Administrator account was used in creating this scenario. A Hybrid Identity Administrator account may be sufficient.
At the top, change the GET to PATCH
In the address box enter:
https://graph.microsoft.com/v1.0/groups/<Group Id>In the Request body enter:
{ extension_<guid>_WritebackEnabled: true }If done correctly, you see [].
Now at the top, change PATCH to GET and look at the properties of the marketing group.
Click Run query. You should see the newly created attribute.
Test our configuration
Note
When using on-demand provisioning, members aren't automatically provisioned. You need to select which members you wish to test on and there's a 5 member limit.
- Sign in to the Microsoft Entra admin center as at least a Hybrid Administrator.
- Browse to Identity > Hybrid management > Microsoft Entra Connect > Cloud sync.
- Under Configuration, select your configuration.
- On the left, select Provision on demand.
- Enter Marketing in the Selected group box
- From the Selected users section, select some users to test. Select Lola Jacobson and John Smith.
- Click Provision. It should successfully provision.

- Now try with the Sales group and add Britta Simon and Anna Ringdahl. This shouldn't provision.

- In Active Directory, you should see the newly created Marketing group.

- You can now browse to Identity > Hybrid Management > Microsoft Entra Connect > Cloud sync > Overview page to Review and Enable our configuration to start synchronizing.