Import, export, and deploy exploit protection configurations
Applies to:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender XDR
Want to experience Defender for Endpoint? Sign up for a free trial.
Exploit protection helps protect devices from malware that use exploits to spread and infect. It consists of a number of mitigations that can be applied at either the operating system level, or at the individual app level.
You use the Windows Security app or PowerShell to create a set of mitigations (known as a configuration). You can then export this configuration as an XML file and share it with multiple devices on your network. Then, they all have the same set of mitigation settings.
Create and export a configuration file
Before you export a configuration file, you need to ensure you have the correct settings. First, configure exploit protection on a single, dedicated device. See Customize exploit protection for more information about configuring mitigations.
When you've configured exploit protection to your desired state (including both system-level and app-level mitigations), you can export the file using either the Windows Security app or PowerShell.
Use the Windows Security app to export a configuration file
Open the Windows Security app by selecting the shield icon in the task bar. Or, search the start menu for Windows Security.
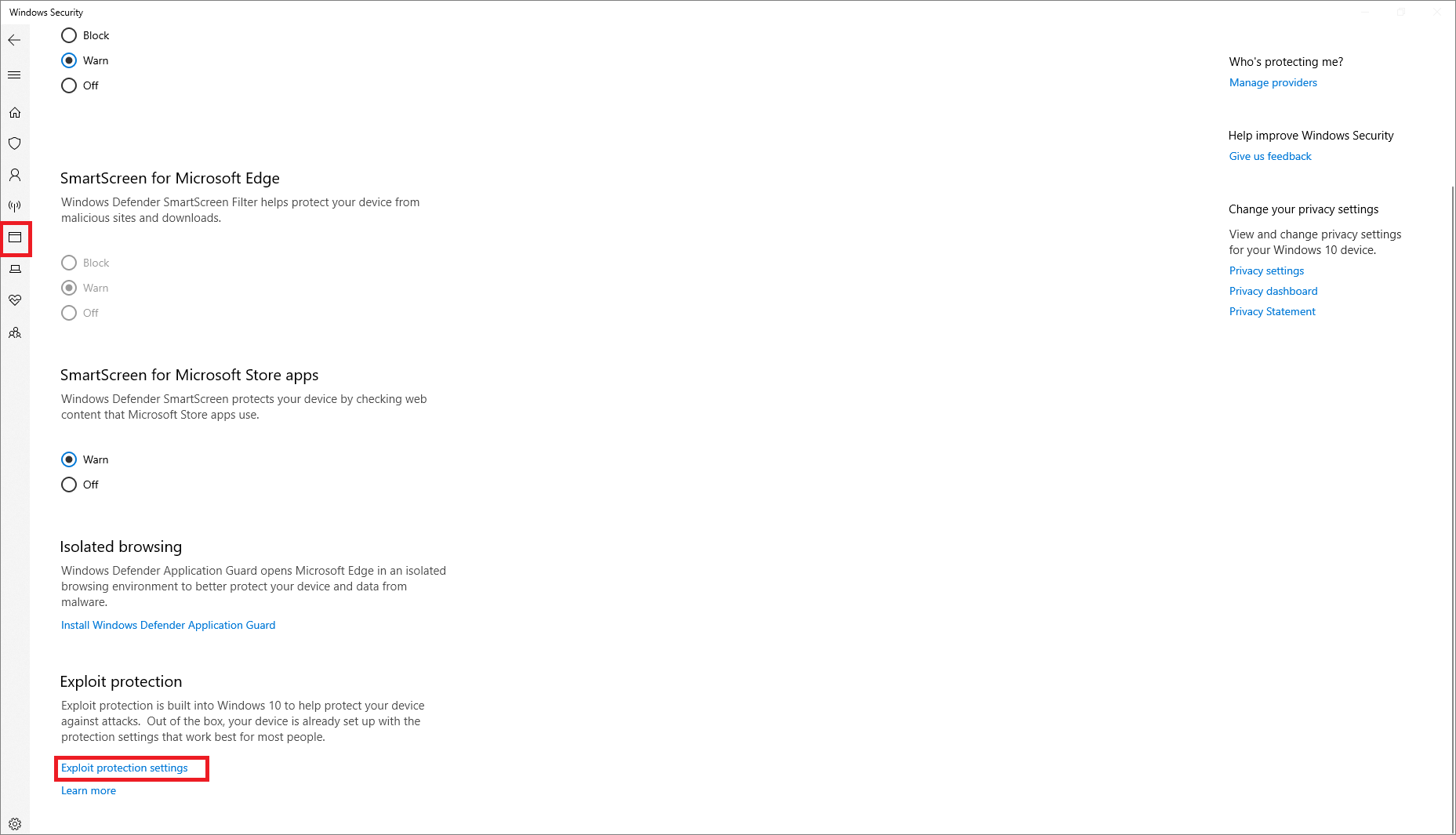
Select the App & browser control tile (or the app icon on the left menu bar) and then select Exploit protection settings:
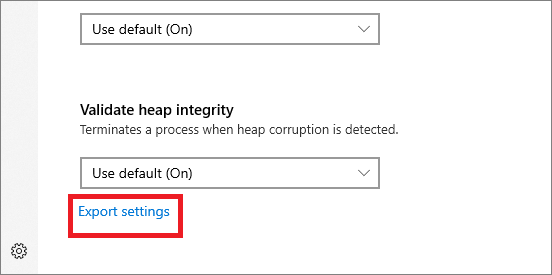
At the bottom of the Exploit protection section, select Export settings. Choose the location and name of the XML file where you want the configuration to be saved.
Important
If you want to use Default configuration, use the settings "On by default" instead of "Use Default (On)" to get the settings exported correctly on the XML file.
Note
When you export the settings, all settings for both app-level and system-level mitigations are saved. This means you don't need to export a file from both the System settings and Program settings sections (either section will export all settings).
Use PowerShell to export a configuration file
Type powershell in the Start menu, right-click Windows PowerShell and select Run as administrator.
Enter the following cmdlet:
Get-ProcessMitigation -RegistryConfigFilePath filename.xmlChange
filenameto any name or location of your choosing.Example command:
Get-ProcessMitigation -RegistryConfigFilePath C:\ExploitConfigfile.xml
Important
When you deploy the configuration using Group Policy, all devices that will use the configuration must be able to access the configuration file. Ensure you place the file in a shared location.
Import a configuration file
You can import an exploit protection configuration file that you've previously created. You can only use PowerShell to import the configuration file.
After importing, the settings will be instantly applied and can be reviewed in the Windows Security app.
Use PowerShell to import a configuration file
Type powershell in the Start menu, right-click Windows PowerShell and select Run as administrator.
Enter the following cmdlet:
Set-ProcessMitigation -PolicyFilePath filename.xmlChange
filenameto the location and name of the exploit protection XML file.Example command:
Set-ProcessMitigation -PolicyFilePath C:\ExploitConfigfile.xml
Important
Ensure you import a configuration file that is created specifically for exploit protection.
Manage or deploy a configuration
You can use Group Policy to deploy the configuration you've created to multiple devices in your network.
Important
When you deploy the configuration using Group Policy, all devices that will use the configuration must be able to access the configuration XML file. Ensure you place the file in a shared location.
Use Group Policy to distribute the configuration
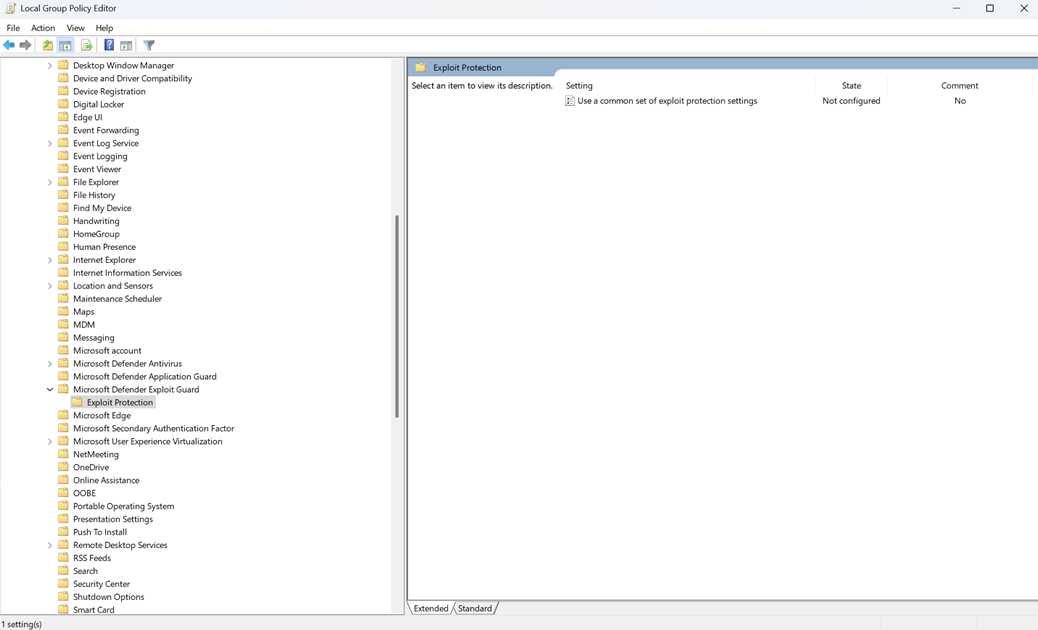
On your Group Policy management device, open the Group Policy Management Console, right-click the Group Policy Object you want to configure and Edit.
In the Group Policy Management Editor, go to Computer configuration and select Administrative templates.
Expand the tree to Windows components > Microsoft Defender Exploit Guard > Exploit protection.
Double-click Use a common set of Exploit protection settings and set the option to Enabled.
In the Options: section, enter the location and file name of the Exploit protection configuration file that you want to use, such as in the following examples:
C:\MitigationSettings\Config.XML\\Server\Share\Config.xmlhttps://localhost:8080/Config.xmlC:\ExploitConfigfile.xml
Select OK and Deploy the updated GPO as you normally do.
See also
- Protect devices from exploits
- Evaluate exploit protection
- Enable exploit protection
- Configure and audit exploit protection mitigations
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.