Σημείωση
Η πρόσβαση σε αυτήν τη σελίδα απαιτεί εξουσιοδότηση. Μπορείτε να δοκιμάσετε να εισέλθετε ή να αλλάξετε καταλόγους.
Η πρόσβαση σε αυτήν τη σελίδα απαιτεί εξουσιοδότηση. Μπορείτε να δοκιμάσετε να αλλάξετε καταλόγους.
Microsoft Entra logs all sign-ins into a Microsoft Entra tenant, which includes your internal apps and resources. As an IT administrator, you need to know what the sign-in log details mean, so that you can interpret the log values correctly.
Reviewing sign-in errors and patterns provides valuable insight into how your users access applications and services. The sign-in logs provided by Microsoft Entra ID are a powerful type of activity log that you can analyze. This article describes several key aspects of the sign-in logs.
Three other activity logs are also available to help monitor the health of your tenant:
- Audit – Information about changes applied to your tenant, such as users and group management or updates applied to your tenant’s resources.
- Sign-ups (preview) - For external tenants only, information about all self-service sign-up attempts, including successful sign-ups and failed attempts.
- Provisioning – Activities performed by a provisioning service, such as the creation of a group in ServiceNow or a user imported from Workday.
What can you do with sign-in logs?
You can use the sign-in logs to answer questions such as:
- How many users signed into a particular application this week?
- How many failed sign-in attempts occurred in the last 24 hours?
- Are users signing in from specific browsers or operating systems?
- Which of my Azure resources were accessed by managed identities and service principals?
You can also describe the activity associated with a sign-in request by identifying the following details:
- Who – The identity (User) performing the sign-in.
- How – The client (Application) used for the sign-in.
- What – The target (Resource) accessed by the identity.
Note
Entries in the sign-in logs are system generated and can't be changed or deleted.
How do you access the sign-in logs?
There are several ways to access the logs, depending on your needs. For more information, see How to access activity logs.
To view the sign-in logs from the Microsoft Entra admin center:
- Sign in to the Microsoft Entra admin center as at least a Reports Reader.
- Browse to Entra ID > Monitoring & health > Sign-in logs.
To more effectively use the sign-in logs in the Microsoft Entra admin center, adjust the filters to only view a specific set of logs. For more information, see Filter sign-in logs.
What are the types of sign-in logs?
There are four types of logs in the sign-in logs preview:
- Interactive user sign-ins
- Non-interactive user sign-ins
- Service principal sign-ins
- Managed identity sign-ins
The classic sign-in logs only include interactive user sign-ins.
Microsoft Entra Agent ID
The Microsoft Entra Agent ID was launched at Microsoft Build 2025 and provides a unified directory of all agent identities created across Microsoft Copilot Studio and Azure AI Foundry. With this initial release, IT administrators can view and manage agent identities directly in the Microsoft Entra admin center, including updated sign-in logs. Because agents can operate with user-delegated or app-only permissions, their sign-ins might appear across each of the four sign-in log types.
A new complex sign-in log resource type, agentSignIn, was added to the Microsoft Entra sign-in logs. This resource type contains properties about the agent, such as if the agent is an app or an instance of an app. If the agent type is agenticAppInstance, the parentID property is included to provide traceability to the provisioning agent.
The new sign-in log resource type is available in the Microsoft Entra admin center and the Microsoft Graph API.
- Use the
isAgentfilter in the Microsoft Entra admin center sign-in logs to filter on only agentic sign-in events. - From Enterprise applications, set the Application type filter to Agent ID (Preview) to view all agent identities in your tenant. Then select Sign-in logs from the app details page to view the sign-in activity.
- For information about the resource type in Microsoft Graph, see agentSignIn
For more information, see the Microsoft Entra Blog announcement.
Sign-in data used by other services
Sign-in data is used by several services in Azure and Microsoft Entra to monitor risky sign-ins, provide insight into application usage, and more.
Microsoft Entra ID Protection
Sign-in log data visualization that relates to risky sign-ins is available in the Microsoft Entra ID Protection overview, which uses the following data:
- Risky users
- Risky user sign-ins
- Risky workload identities
For more information about the Microsoft Entra ID Protection tools, see the Microsoft Entra ID Protection overview.
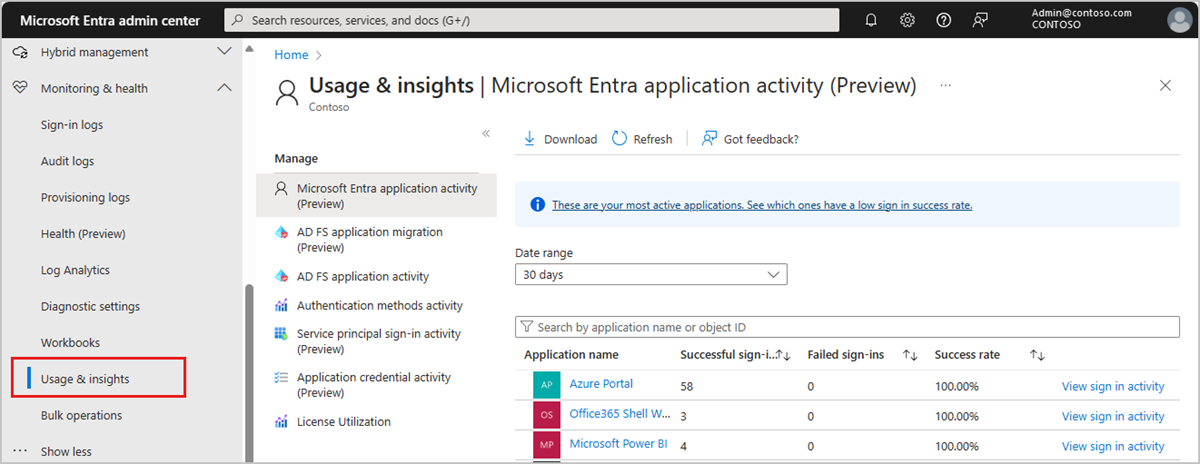
Microsoft Entra Usage and insights
To view application-specific sign-in data, browse to Microsoft Entra ID > Monitoring & health > Usage & insights. These reports provide a closer look at sign-ins for Microsoft Entra application activity and AD FS application activity. For more information, see Microsoft Entra Usage & insights.
There are several reports available in Usage & insights. Some of these reports are in preview.
- Microsoft Entra application activity (preview)
- AD FS application activity
- Authentication methods activity
- Service principal sign-in activity
- Application credential activity
Microsoft 365 activity logs
You can view Microsoft 365 activity logs from the Microsoft 365 admin center. Microsoft 365 activity and Microsoft Entra activity logs share a significant number of directory resources. Only the Microsoft 365 admin center provides a full view of the Microsoft 365 activity logs.
You can access the Microsoft 365 activity logs programmatically by using the Office 365 Management APIs.