Get started with activity explorer
The data classification overview and content explorer tabs give you visibility into what content has been discovered and labeled, and where that content is. Activity explorer rounds out this suite of functionality by allowing you to monitor what's being done with your labeled content. Activity explorer provides a historical view of activities on your labeled content. The activity information is collected from the Microsoft 365 unified audit logs, transformed, and then made available in the Activity explorer UI. Activity explorer reports on up to 30 days worth of data.
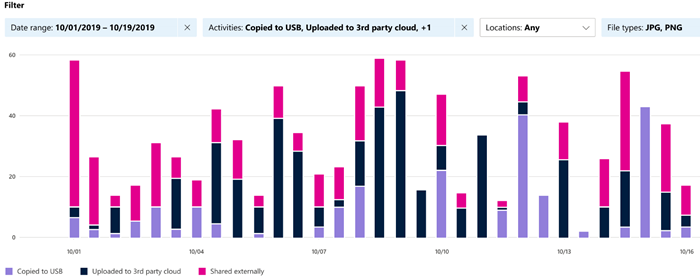
There are more than 30 different filters available for use, some are:
- Date range
- Activity type
- Location
- User
- Sensitivity label
- Retention label
- File path
- DLP policy
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview compliance portal trials hub. Learn details about signing up and trial terms.
Prerequisites
Every account that accesses and uses data classification must have a license assigned to it from one of these subscriptions:
- Microsoft 365 (E5)
- Office 365 (E5)
- Advanced Compliance (E5) add-on
- Advanced Threat Intelligence (E5) add-on
- Microsoft 365 E5/A5 Info Protection & Governance
- Microsoft 365 E5/A5 Compliance
Permissions
An account must be explicitly assigned membership in any one of these role groups, or must be explicitly granted the role.
Roles and Role Groups
There are roles and role groups that you can use to fine-tune your access controls. To learn more about them, see Permissions in the Microsoft Purview compliance portal.
| Microsoft Purview Roles | Microsoft Purview Role Groups | Microsoft 365 Roles | Microsoft 365 Role Groups |
|---|---|---|---|
| Information Protection Admin | Information Protection | Global Admins | Compliance Administrator |
| Information Protection Analyst | Information Protection Admins | Compliance Admins | Security Administrator |
| Information Protection Investigator | Information Protection Investigators | Security Admins | Security Reader |
| Information Protection Reader | Information Protection Analysts | Compliance Data Admins | |
| Information Protection Readers |
Activity types
Activity explorer gathers information from the audit logs of multiple sources of activities.
Some examples of the Sensitivity label activities and Retention labeling activities from applications native to Microsoft Office, the Microsoft Information Protection client and scanner, SharePoint, Exchange (sensitivity labels only), and OneDrive include:
- Label applied
- Label changed (upgraded, downgraded, or removed)
- Autolabeling simulation
- File read
For the current list of activities listed in Activity explorer, go into Activity explorer and open the acitivity filter. The list of activities is available in the dropdown list.
Labeling activity specific to the Microsoft Information Protection client and scanner that comes into Activity explorer includes:
- Protection applied
- Protection changed
- Protection removed
- Files discovered
For more detailed information on what labeling activity makes it into Activity explorer, see Labeling events available in Activity explorer.
In addition, using Endpoint data loss prevention (DLP), Activity explorer gathers DLP policy matches events from Exchange, SharePoint, OneDrive, Teams Chat and Channel, on-premises SharePoint folders and libraries, on-premises file shares, and devices running Windows 10, Windows 11, and any of the three most recent major macOS versions. Some example events gathered from Windows 10 devices include the following actions taken on files:
- Deletion
- Creation
- Copy to clipboard
- Modify
- Read
- Rename
- Copy to network share
- Access by an unallowed app
Understanding the actions that are taken on content with sensitivity labels helps you determine whether the controls that you have in place, such as Microsoft Purview Data Loss Prevention policies, are effective. If not, or if you discover something unexpected (such as a large number of items labeled highly confidential that are downgraded to general), you can manage your policies and take new actions to restrict the undesired behavior.
Note
Activity explorer doesn't currently monitor retention activities for Exchange.
Note
In case the Teams DLP verdict is reported as false positive by the user, the activity will be showing as DLP infoin the list on activity explorer. The entry will not have any rule and policy match details present but will show synthetic values. There will also be no incident report generated for false positive reporting.
Activity type events and alerts
The table that follows lays out the events that are triggered in Activity Explorer for three sample policy configurations, depending on whether or not a policy match is detected.
| Policy configuration | Activity Explorer event triggered for this action type | Activity Explorer event triggered when a DLP rule is matched | Activity Explorer alert triggered |
|---|---|---|---|
| Policy contains a single rule allowing the activity without auditing it. | Yes | No | No |
| Policy contains two rules: Matches for Rule #1 are allowed; policy matches for Rule #2 are audited. | Yes (Rule #2 only) |
Yes (Rule #2 only) |
Yes (Rule #2 only) |
| Policy contains two rules: Matches fore both rules are allowed and not audited. | Yes | No | No |
See also
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for