Set up unmanaged (BYOD) devices with Microsoft 365 Business Premium
Every device, whether managed or unmanaged, is a possible attack avenue into your network. Microsoft 365 Business Premium includes capabilities to help everyone protect devices, including unmanaged devices (also referred to as bring-your-own devices, or BYODs). Learn more about managed and unmanaged devices.
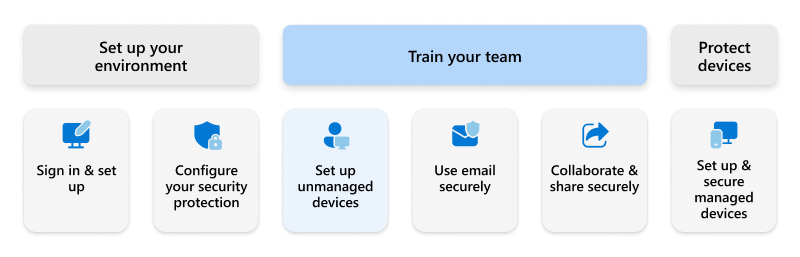
To set up unmanaged (BYOD) devices, follow these steps:
Once you've completed these steps, proceed to Use email securely.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for