"80041317" or "80043431" error when federated users sign in to Microsoft 365, Azure, or Intune
Problem
When a federated user tries to sign in to a Microsoft cloud service such as Microsoft 365, Microsoft Azure, or Microsoft Intune from a sign-in webpage whose URL starts with "https://login.microsoftonline.com/login," authentication for that user fails. Additionally, the user receives the following error message:
Sorry, but we're having trouble signing you in
Please try again in a few minutes. If this doesn't work, you might want to contact your admin and report the following error:
80041317 or 80043431
Cause
This issue occurs when the configuration settings of the federated domain for the on-premises Active Directory Federation Services (AD FS) service and for the Microsoft Entra authentication system are mismatched. This causes the claim that the AD FS service supplies to be malformed and therefore rejected by the Microsoft Entra authentication system.
Note
This can occur after the token-signing certificate is renewed on-premises without updating federation trust data.
Note
Azure AD and MSOnline PowerShell modules are deprecated as of March 30, 2024. To learn more, read the deprecation update. After this date, support for these modules are limited to migration assistance to Microsoft Graph PowerShell SDK and security fixes. The deprecated modules will continue to function through March, 30 2025.
We recommend migrating to Microsoft Graph PowerShell to interact with Microsoft Entra ID (formerly Azure AD). For common migration questions, refer to the Migration FAQ. Note: Versions 1.0.x of MSOnline may experience disruption after June 30, 2024.
To verify that this is the cause of the issue that you're experiencing, follow these steps on a domain-joined computer:
- Verify the mismatched attribute between the AD FS service and the Microsoft cloud service. To do this, follow these steps:
Click Start, click All Programs, click Microsoft Entra ID, and then click Microsoft Azure Active Directory module for Windows PowerShell.
At the command prompt, type the following commands. Make sure that you press Enter after you type each command:
$cred = get-credentialNote
When you're prompted, enter your cloud service admin credentials.
Connect-MSOLService –credential:$credSet-MSOLADFSContext –Computer:<AD FS 2.0 Server Name>Note
In this command, the placeholder <AD FS 2.0 Server Name> represents the Windows host name of the primary AD FS server.
Get-MsolFederationProperty -domainname: <Federated Domain Name>Note
In this command, the <Federated Domain Name> placeholder represents the name of the domain that's already federated with the cloud service for single sign-on (SSO).
Note
The command output is divided into the following two sections:
- The first line of the first section reads "Source: AD FS Server" and represents the configuration that's stored in the local AD FS service.
- The first line of the second section reads "Source: <Microsoft cloud service>" and represents the configuration that's stored in the identity service.
The output resembles the following:
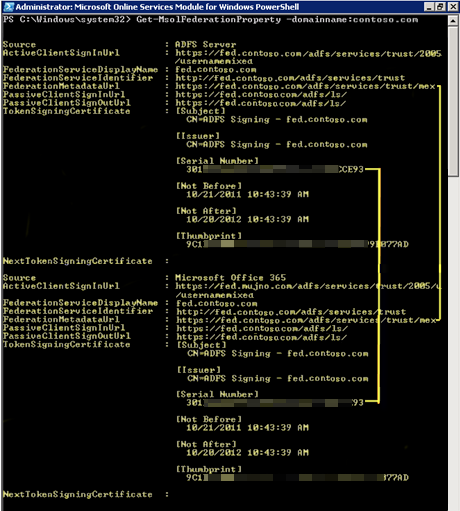
- Compare the values of each attribute in the two sections to determine whether the values are mismatched. If the values are mismatched, the federated domain configuration has to be updated.
Solution
To resolve this issue, use one of the following methods:
Method 1: Update the configuration of the federated domain
For more information about how to do this, see the "How to update the configuration of the Microsoft 365 federated domain" section in How to update or repair the settings of a federated domain in Microsoft 365, Azure, or Intune.
Method 2: Repair the configuration of the federated domain
If method 1 doesn't resolve the issue, try to repair the federated trust. For more information about how to do this, see the "How to repair the configuration of the Microsoft 365 federated domain" section in How to update or to repair the configuration of the Microsoft 365 federated domain .
Method 3: Manually update the attributes by using the Azure Active Directory module for Windows PowerShell
If methods 1 and 2 don't resolve the issue, try to manually update the mismatched attributes. In the Windows PowerShell connection that you used to diagnose the issue, run the appropriate cmdlet from the following table:
| Mismatched attributes | Error code | Command to update attribute | Notes |
|---|---|---|---|
| FederationServiceIdentifier | 80043431 | Set-MSOLDomainFederationSettings -domain name <Domain.suffix> -issueruri <newURI> | The placeholder <Domain.suffix> represents the federated domain name. The placeholder <newURI> represents the URI value of the on-premises FederationServiceIdentifierattribute (listed first in the output of the Get-MsolFederationProperty cmdlet). |
Still need help? Go to Microsoft Community or the Microsoft Entra Forums website.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for