Security and privacy
Note
You've reached the documentation for Microsoft Edge version 45 and earlier. To see the documentation for Microsoft Edge version 77 or later, go to the Microsoft Edge documentation landing page.
Microsoft Edge is designed with improved security in mind, helping to defend people from increasingly sophisticated and prevalent web-based attacks against Windows. Because Microsoft Edge is designed like a Universal Windows app, changing the browser to an app, it fundamentally changes the process model so that both the outer manager process and the different content processes all live within app container sandboxes.
Microsoft Edge runs in 64-bit not just by default, but anytime it’s running on a 64-bit operating system. Because Microsoft Edge doesn’t support legacy ActiveX controls or 3rd-party binary extensions, there’s no longer a reason to run 32-bit processes on a 64-bit system.
The value of running 64-bit all the time is that it strengthens Windows Address Space Layout Randomization (ASLR), randomizing the memory layout of the browser processes, making it much harder for attackers to hit precise memory locations. In turn, 64-bit processes make ASLR much more effective by making the address space exponentially larger and, therefore, more difficult for attackers to find sensitive memory components.
For more details on the security features in Microsoft Edge, see Help protect against web-based security threats below.
You can find the Microsoft Edge Group Policy settings in the following location of the Group Policy Editor unless otherwise noted in the policy:
Computer Configuration\Administrative Templates\Windows Components\Microsoft Edge\
Configure cookies
Supported versions: Microsoft Edge on Windows 10
Default setting: Disabled or not configured (Allow all cookies from all sites)
Microsoft Edge allows all cookies from all websites by default. With this policy, you can configure Microsoft to block only 3rd-party cookies or block all cookies.
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Enabled | 0 | 0 | Block all cookies from all sites. |  |
| Enabled | 1 | 1 | Block only cookies from third party websites. | |
| Disabled or not configured (default) |
2 | 2 | Allow all cookies from all sites. |
ADMX info and settings
ADMX info
- GP English name: Configure cookies
- GP name: Cookies
- GP element: CookiesListBox
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/AllowCookies
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/AllowCookies
- Data type: Integer
Registry settings
- Path: HKLM\Software\Policies\Microsoft\MicrosoftEdge\Main
- Value name: Cookies
- Value type: REG_DWORD
Configure Password Manager
Supported versions: Microsoft Edge on Windows 10
Default setting: Enabled (Allowed/users can change the setting)
By default, Microsoft Edge uses Password Manager automatically, allowing users to manager passwords locally. Disabling this policy restricts Microsoft Edge from using Password Manager. Don’t configure this policy if you want to let users choose to save and manage passwords locally using Password Manager.
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Not configured | Blank | Blank | Users can choose to save and manage passwords locally. | |
| Disabled | 0 | no | Not allowed. |  |
| Enabled (default) |
1 | yes | Allowed. |
Verify not allowed/disabled settings:
- Click or tap More (…) and select Settings > View Advanced settings.
- Verify the settings Save Password is toggled off or on and is greyed out.
ADMX info and settings
ADMX info
- GP English name: Configure Password Manager
- GP name: AllowPasswordManager
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/AllowPasswordManager
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/AllowPasswordManager
- Data type: Integer
Registry settings
- Path: HKLM\Software\Policies\Microsoft\MicrosoftEdge\Main
- Value name: FormSuggest Passwords
- Value type: REG_SZ
Configure Windows Defender SmartScreen
Supported versions: Microsoft Edge on Windows 10
Default setting: Enabled (Turned on)
Microsoft Edge uses Windows Defender SmartScreen (turned on) to protect users from potential phishing scams and malicious software by default. Also, by default, users cannot disable (turn off) Windows Defender SmartScreen. Enabling this policy turns on Windows Defender SmartScreen and prevent users from turning it off. Don’t configure this policy to let users choose to turn Windows defender SmartScreen on or off.
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Not configured | Blank | Blank | Users can choose to use Windows Defender SmartScreen. | |
| Disabled | 0 | 0 | Turned off. Do not protect users from potential threats and prevent users from turning it on. | |
| Enabled | 1 | 1 | Turned on. Protect users from potential threats and prevent users from turning it off. |  |
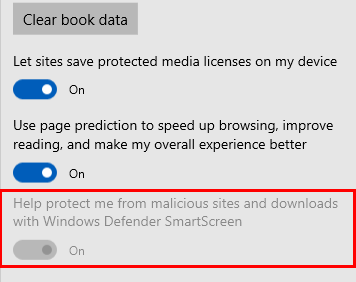
To verify Windows Defender SmartScreen is turned off (disabled):
- Click or tap More (…) and select Settings > View Advanced settings.
- Verify the setting Help protect me from malicious sites and download with Windows Defender SmartScreen is disabled.
ADMX info and settings
ADMX info
- GP English name: Configure Windows Defender SmartScreen
- GP name: AllowSmartScreen
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/AllowSmartScreen
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/AllowSmartScreen
- Data type: Integer
Registry settings
- Path: HKLM\SOFTWARE\Policies\Microsoft\MicrosoftEdge\PhishingFilter
- Value name: EnabledV9
- Value type: REG_DWORD
Prevent bypassing Windows Defender SmartScreen prompts for files
Supported versions: Microsoft Edge on Windows 10, version 1511 or later
Default setting: Disabled or not configured (Allowed/turned off)
By default, Microsoft Edge allows users to bypass (ignore) the Windows Defender SmartScreen warnings about potentially malicious files, allowing them to continue downloading the unverified file(s). Enabling this policy prevents users from bypassing the warnings, blocking them from downloading of the unverified file(s).
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Disabled or not configured (default) |
0 | 0 | Allowed/turned off. Users can ignore the warning and continue to download the unverified file(s). | |
| Enabled | 1 | 1 | Prevented/turned on. |  |
ADMX info and settings
ADMX info
- GP English name: Prevent bypassing Windows Defender SmartScreen prompts for files
- GP name: PreventSmartScreenPromptOverrideForFiles
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/PreventSmartScreenPromptOverrideForFiles
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/PreventSmartScreenPromptOverrideForFiles
- Data type: Integer
Registry settings
- Path: HKLM\SOFTWARE\Policies\Microsoft\MicrosoftEdge\PhishingFilter
- Value name: PreventOverrideAppRepUnknown
- Value type: REG_DWORD
Prevent bypassing Windows Defender SmartScreen prompts for sites
Supported versions: Microsoft Edge on Windows 10, version 1511 or later
Default setting: Disabled or not configured (Allowed/turned off)
By default, Microsoft Edge allows users to bypass (ignore) the Windows Defender SmartScreen warnings about potentially malicious sites, allowing them to continue to the site. With this policy though, you can configure Microsoft Edge to prevent users from bypassing the warnings, blocking them from continuing to the site.
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Disabled or not configured (default) |
0 | 0 | Allowed/turned off. Users can ignore the warning and continue to the site. | |
| Enabled | 1 | 1 | Prevented/turned on. |  |
ADMX info and settings
ADMX info
- GP English name: Prevent bypassing Windows Defender SmartScreen prompts for sites
- GP name: PreventSmartscreenPromptOverride
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/PreventSmartscreenPromptOverride
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/PreventSmartscreenPromptOverride
- Data type: Integer
Registry settings
- Path: HKLM\SOFTWARE\Policies\Microsoft\MicrosoftEdge\PhishingFilter
- Value name: PreventOverride
- Value type: REG_DWORD
Prevent certificate error overrides
Supported versions: Microsoft Edge on Windows 10, version 1809
Default setting: Disabled or not configured (Allowed/turned off)
Microsoft Edge, by default, allows overriding of the security warnings to sites that have SSL errors, bypassing or ignoring certificate errors. Enabling this policy prevents overriding of the security warnings.
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Disabled or not configured (default) |
0 | 0 | Allowed/turned on. Override the security warning to sites that have SSL errors. | |
| Enabled | 1 | 1 | Prevented/turned on. |  |
ADMX info and settings
ADMX info
- GP English name: Prevent certificate error overrides
- GP name: PreventCertErrorOverrides
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/PreventCertErrorOverrides
- Supported devices: Desktop and Mobile
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/PreventCertErrorOverrides
- Data type: Integer
Registry settings
- Path: HKLM\Software\Policies\Microsoft\MicrosoftEdge\Internet Setting
- Value name: PreventCertErrorOverrides
- Value type: REG_DWORD
Prevent using Localhost IP address for WebRTC
Supported versions: Microsoft Edge on Windows 10, version 1511 or later
Default setting: Disabled or not configured (Allowed/show localhost IP addresses)
By default, Microsoft Edge shows localhost IP address while making calls using the WebRTC protocol. Enabling this policy hides the localhost IP addresses.
Supported values
| Group Policy | MDM | Registry | Description | Most restricted |
|---|---|---|---|---|
| Disabled or not configured (default) |
0 | 0 | Allowed. Show localhost IP addresses. | |
| Enabled | 1 | 1 | Prevented. |  |
ADMX info and settings
ADMX info
- GP English name: Prevent using Localhost IP address for WebRTC
- GP name: HideLocalHostIPAddress
- GP path: Windows Components/Microsoft Edge
- GP ADMX file name: MicrosoftEdge.admx
MDM settings
- MDM name: Browser/PreventUsingLocalHostIPAddressForWebRTC
- Supported devices: Desktop
- URI full path: ./Vendor/MSFT/Policy/Config/Browser/PreventUsingLocalHostIPAddressForWebRTC
- Data type: Integer
Registry settings
- Path: HKLM\SOFTWARE\Policies\Microsoft\MicrosoftEdge\Main
- Value name: HideLocalHostIPAddress
- Value type: REG_DWORD
Help protect against web-based security threats
While most websites are safe, some sites have been intentionally designed to steal sensitive and private information or gain access to your system’s resources. You can help protect against threats by using strong security protocols to ensure against such threats.
Thieves use things like phishing attacks to convince someone to enter personal information, such as a banking password, into a website that looks like a legitimate bank but isn't. Attempts to identify legitimate websites through the HTTPS lock symbol and the EV Cert green bar have met with only limited success since attackers are too good at faking legitimate experiences for many people to notice the difference.
Another method thieves often use hacking to attack a system through malformed content that exploits subtle flaws in the browser or various browser extensions. This exploit lets an attacker run code on a device, taking over a browsing session, and perhaps the entire device.
Microsoft Edge addresses these threats to help make browsing the web a safer experience.
| Feature | Description |
|---|---|
| Windows Hello | Microsoft Edge is the first browser to natively support Windows Hello to authenticate the user and the website with asymmetric cryptography technology, powered by early implementation of the Web Authentication (formerly FIDO 2.0 Web API) specification. |
| Microsoft SmartScreen | Defends against phishing by performing reputation checks on sites visited and blocking any sites that are thought to be a phishing site. SmartScreen also helps to defend against installing malicious software, drive-by attacks, or file downloads, even from trusted sites. Drive-by attacks are malicious web-based attacks that compromise your system by targeting security vulnerabilities in commonly used software and may be hosted on trusted sites. |
| Certificate Reputation system | Collects data about certificates in use, detecting new certificates and flagging fraudulent certificates automatically, and sends the data to Microsoft. The systems and tools in place include
|
| Microsoft EdgeHTML and modern web standards | Microsoft Edge uses Microsoft EdgeHTML as the rendering engine. This engine focuses on modern standards letting web developers build and maintain a consistent site across all modern browsers. It also helps to defend against hacking through these security standards features:
NOTE: Both Microsoft Edge and Internet Explorer 11 support HSTS. |
| Code integrity and image loading restrictions | Microsoft Edge content processes support code integrity and image load restrictions, helping to prevent malicious DLLs from loading or injecting into the content processes. Only properly signed images are allowed to load into Microsoft Edge. Binaries on remote devices (such as UNC or WebDAV) can’t load. |
| Memory corruption mitigations | Memory corruption attacks frequently happen to apps written in C or C++ don’t provide safety or buffer overflow protection. When an attacker provides malformed input to a program, the program’s memory becomes corrupt allowing the attacker to take control of the program. Although attackers have adapted and invented new ways to attack, we’ve responded with memory safety defenses, mitigating the most common forms of attack, including and especially use-after-free (UAF) vulnerabilities. |
| Memory Garbage Collector (MemGC) mitigation | MemGC replaces Memory Protector and helps to protect the browser from UAF vulnerabilities. MemGC frees up memory from the programmer and automating it. Only freeing memory when the automation detects no references left pointing to a given block of memory. |
| Control Flow Guard | Attackers use memory corruption attacks to gain control of the CPU program counter to jump to any code location they want. Control Flow Guard, a Microsoft Visual Studio technology, compiles checks around code that performs indirect jumps based on a pointer. Those jumps get restricted to function entry points with known addresses only making attacker take-overs must more difficult constraining where an attack jumps. |
| All web content runs in an app container sandbox | Microsoft Edge takes the sandbox even farther, running its content processes in containers not just by default, but all of the time. Microsoft Edge doesn’t support 3rd party binary extensions, so there is no reason for it to run outside of the container, making Microsoft Edge more secure. |
| Extension model and HTML5 support | Microsoft Edge does not support binary extensions because they can bring code and data into the browser’s processes without any protection. So if anything goes wrong, the entire browser itself can be compromised or go down. We encourage everyone to use our scripted HTML5-based extension model. For more info about the new extensions, see the Microsoft Edge Developer Center. |
| Reduced attack surfaces | Microsoft Edge does not support VBScript, JScript, VML, Browser Helper Objects, Toolbars, ActiveX controls, and document modes. Many IE browser vulnerabilities only appear in legacy document modes, so removing support reduced attack surface making the browser more secure. It also means that it’s not as backward compatible. With this reduced backward compatibility, Microsoft Edge automatically falls back to Internet Explorer 11 for any apps that need backward compatibility. This fall back happens when you use the Enterprise Mode Site List. |