Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this quick start, you connect your GitHub organizations on the Environment settings page in Microsoft Defender for Cloud. This page provides a simple onboarding experience to autodiscover your GitHub repositories.
By connecting your GitHub environments to Defender for Cloud, you extend the security capabilities of Defender for Cloud to your GitHub resources and improve security posture. Learn more.
Prerequisites
To complete this quick start, you need:
- An Azure account with Defender for Cloud onboarded. If you don't already have an Azure account, create one for free.
Availability
| Aspect | Details |
|---|---|
| Release state: | General Availability. |
| Pricing: | For pricing, see the Defender for Cloud pricing page You can also estimate costs with the Defender for Cloud cost calculator. |
| Required permissions: | Account Administrator with permissions to sign in to the Azure portal. Contributor to create the connector on the Azure subscription. Organization Owner in GitHub. |
| GitHub supported plans and user models | GitHub Free, Pro, Team, and Enterprise Cloud (with personal accounts and Enterprise Managed Users) |
| Regions and availability: | Refer to the support and prerequisites section for region support and feature availability. |
| Clouds: |  Commercial
Commercial  National (Azure Government, Microsoft Azure operated by 21Vianet)
National (Azure Government, Microsoft Azure operated by 21Vianet) |
Note
Security Reader role can be applied on the Resource Group/GitHub connector scope to avoid setting highly privileged permissions on a Subscription level for read access of DevOps security posture assessments.
Connect your GitHub environment
To connect your GitHub environment to Microsoft Defender for Cloud:
Sign in to the Azure portal.
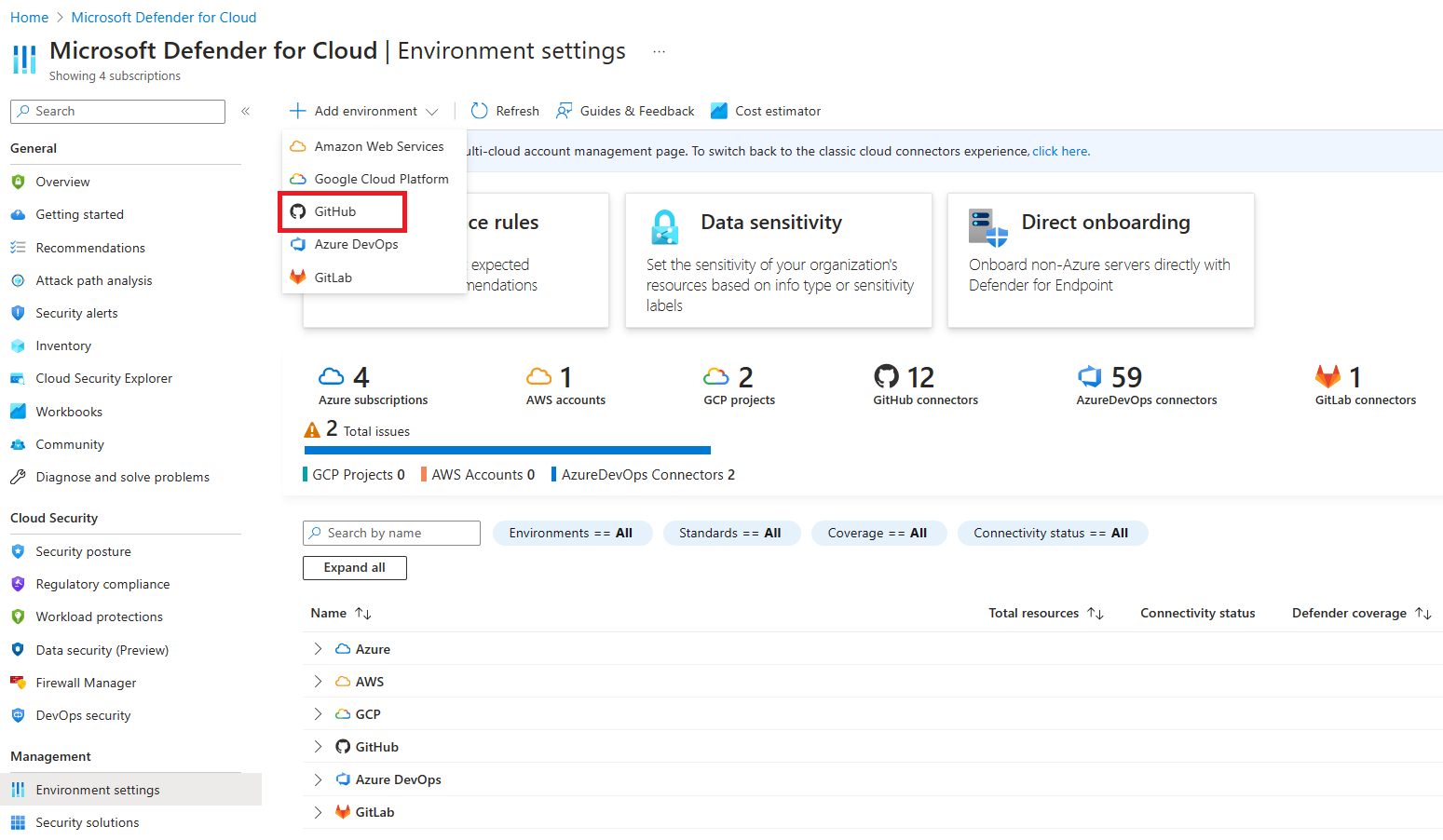
Go to Microsoft Defender for Cloud > Environment settings.
Select Add environment.
Select GitHub.
Enter a name (limit of 20 characters), and then select your subscription, resource group, and region.
The subscription is the location where Defender for Cloud creates and stores the GitHub connection.
Select Next: Configure access.
Select Authorize to grant your Azure subscription access to your GitHub repositories. Sign in, if necessary, with an account that has permissions to the repositories that you want to protect.
After authorization, if you wait too long to install the DevOps security GitHub application, the session will time out and you'll get an error message.
Select Install.
Select the organizations to install the Defender for Cloud GitHub application. It's recommended to grant access to all repositories to ensure Defender for Cloud can secure your entire GitHub environment.
This step grants Defender for Cloud access to organizations that you wish to onboard.
All organizations with the Defender for Cloud GitHub application installed will be onboarded to Defender for Cloud. To change the behavior going forward, select one of the following:
Select all existing organizations to automatically discover all repositories in GitHub organizations where the DevOps security GitHub application is installed.
Select all existing and future organizations to automatically discover all repositories in GitHub organizations where the DevOps security GitHub application is installed and future organizations where the DevOps security GitHub application is installed.
Note
Organizations can be removed from your connector after the connector creation is complete. See the editing your DevOps connector page for more information.
Select Next: Review and generate.
Select Create.
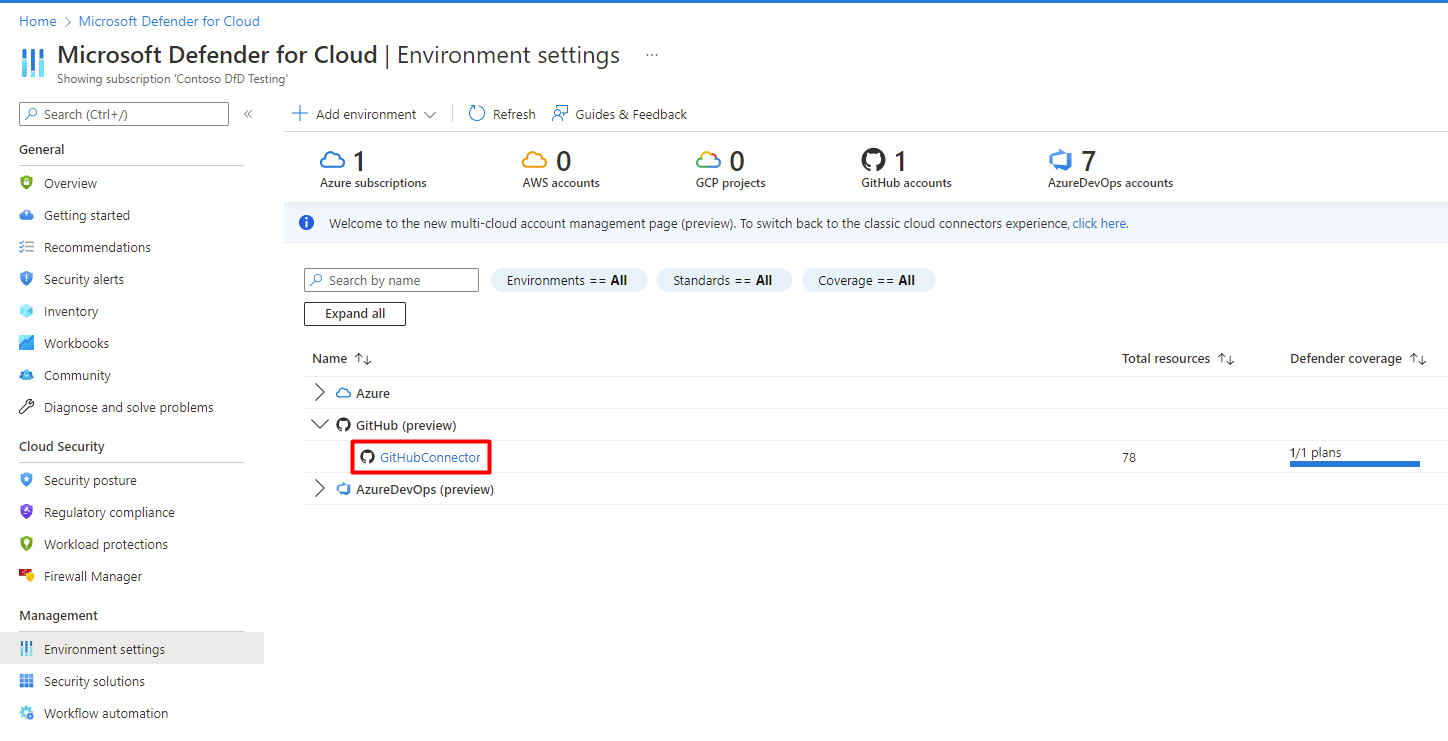
When the process finishes, the GitHub connector appears on your Environment settings page.
The Defender for Cloud service automatically discovers the organizations where you installed the DevOps security GitHub application.
Note
To ensure proper functionality of advanced DevOps posture capabilities in Defender for Cloud, only one instance of a GitHub organization can be onboarded to the Azure Tenant you are creating a connector in.
Upon successful onboarding, DevOps resources (e.g., repositories, builds) will be present within the Inventory and DevOps security pages. It might take up to 8 hours for resources to appear. Security scanning recommendations might require an additional step to configure your workflows. Refresh intervals for security findings vary by recommendation and details can be found on the Recommendations page.
Next steps
- Learn about DevOps security in Defender for Cloud.
- Learn how to configure the Microsoft Security DevOps GitHub action.