Tutorial: Configure Salesforce for automatic user provisioning
The objective of this tutorial is to show the steps required to perform in Salesforce and Microsoft Entra ID to automatically provision and de-provision user accounts from Microsoft Entra ID to Salesforce.
Prerequisites
The scenario outlined in this tutorial assumes that you already have the following items:
A Microsoft Entra tenant.
A Salesforce.com tenant.
A Salesforce account username and password and the token. In future, if you reset the account password, Salesforce provides you with a new token and you'll need to edit the Salesforce provisioning settings.
A custom user profile in Salesforce. Once you have created a custom profile in the Salesforce portal, edit the profile's Administrative Permissions to enable the following:
API Enabled.
Manage Users: Enabling this option automatically enables the following: Assign Permission Sets, Manage Internal UsersManage IP Addresses, Manage Login Access Policies, Manage Password Policies, Manage Profiles and Permission Sets, Manage Roles, Manage Sharing, Reset User Passwords and Unlock Users, View All Users, View Roles and Hierarchy, View Setup and Configuration.
See also Salesforce Create or Clone Profiles documentation.
Note
Assign the permissions directly to the profile. Don't add the permissions through permission sets.
Note
Roles should not be manually edited in Microsoft Entra ID when doing role imports.
Important
If you are using a Salesforce.com trial account, then you will be unable to configure automated user provisioning. Trial accounts do not have the necessary API access enabled until they are purchased. You can get around this limitation by using a free developer account to complete this tutorial.
If you are using a Salesforce Sandbox environment, see the Salesforce Sandbox integration tutorial.
Assigning users to Salesforce
Microsoft Entra ID uses a concept called "assignments" to determine which users should receive access to selected apps. In the context of automatic user account provisioning, only the users and groups that are "assigned" to an application in Microsoft Entra ID are synchronized.
Before configuring and enabling the provisioning service, you need to decide which users or groups in Microsoft Entra ID need access to your Salesforce app. You can assign these users to your Salesforce app by following the instructions in Assign a user or group to an enterprise app
Important tips for assigning users to Salesforce
It is recommended that a single Microsoft Entra user is assigned to Salesforce to test the provisioning configuration. More users and/or groups may be assigned later.
When assigning a user to Salesforce, you must select a valid user role. The "Default Access" role does not work for provisioning
Note
This app imports profiles from Salesforce as part of the provisioning process, which the customer may want to select when assigning users in Microsoft Entra ID. Please note that the profiles that get imported from Salesforce appear as Roles in Microsoft Entra ID.
Enable automated user provisioning
This section guides you through connecting your Microsoft Entra ID to Salesforce's user account provisioning API - v40
Tip
You may also choose to enabled SAML-based Single Sign-On for Salesforce, following the instructions provided in the Azure portal. Single sign-on can be configured independently of automatic provisioning, though these two features complement each other.
Configure automatic user account provisioning
The objective of this section is to outline how to enable user provisioning of Active Directory user accounts to Salesforce.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications.
If you have configured Salesforce for single sign-on, search for your instance of Salesforce using the search field. Otherwise, select Add and search for Salesforce in the application gallery. Select Salesforce from the search results, and add it to your list of applications.
Select your instance of Salesforce, then select the Provisioning tab.
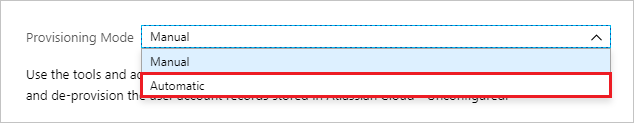
Set the Provisioning Mode to Automatic.
Under the Admin Credentials section, provide the following configuration settings:
In the Admin Username textbox, type a Salesforce account name that has the System Administrator profile in Salesforce.com assigned.
In the Admin Password textbox, type the password for this account.
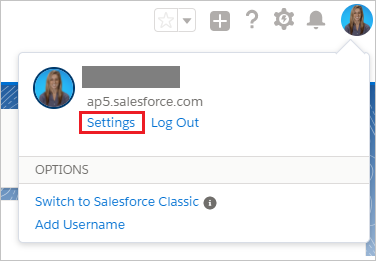
To get your Salesforce security token, open a new tab and sign into the same Salesforce admin account. On the top right corner of the page, click your name, and then click Settings.
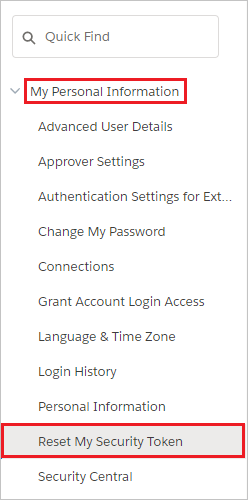
On the left navigation pane, click My Personal Information to expand the related section, and then click Reset My Security Token.
On the Reset Security Token page, click Reset Security Token button.
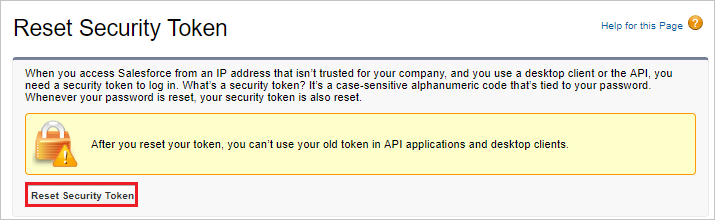
Check the email inbox associated with this admin account. Look for an email from Salesforce.com that contains the new security token.
Copy the token, go to your Microsoft Entra window, and paste it into the Secret Token field.
The Tenant URL should be entered if the instance of Salesforce is on the Salesforce Government Cloud. Otherwise, it is optional. Enter the tenant URL using the format of
https://<your-instance>.my.salesforce.com, replacing<your-instance>with the name of your Salesforce instance.Select Test Connection to ensure Microsoft Entra ID can connect to your Salesforce app.
In the Notification Email field, enter the email address of a person or group who should receive provisioning error notifications, and check the checkbox below.
Click Save.
Under the Mappings section, select Synchronize Microsoft Entra users to Salesforce.
In the Attribute Mappings section, review the user attributes that are synchronized from Microsoft Entra ID to Salesforce. Note that the attributes selected as Matching properties are used to match the user accounts in Salesforce for update operations. Select the Save button to commit any changes.
To enable the Microsoft Entra provisioning service for Salesforce, change the Provisioning Status to On in the Settings section
Click Save.
Note
Once the users are provisioned in the Salesforce application, administrator need to configure the language specific settings for them. Please see this article for more details on language configuration.
This starts the initial synchronization of any users and/or groups assigned to Salesforce in the Users and Groups section. The initial sync takes longer to perform than subsequent syncs, which occur approximately every 40 minutes as long as the service is running. You can use the Synchronization Details section to monitor progress and follow links to provisioning activity logs, which describe all actions performed by the provisioning service on your Salesforce app.
For more information on how to read the Microsoft Entra provisioning logs, see Reporting on automatic user account provisioning.
Common issues
- If you are having issues authorizing access to Salesforce ensure the following:
- The credentials used have admin access to Salesforce.
- The version of Salesforce that you are using supports Web Access (such as Developer, Enterprise, Sandbox, and Unlimited editions of Salesforce.)
- Web API access is enabled for the user.
- The Microsoft Entra provisioning service supports provisioning language, locale, and timeZone for a user. These attributes are in the default attribute mappings but do not have a default source attribute. Ensure that you select the default source attribute and that the source attribute is in the format expected by SalesForce. For example, localeSidKey for english(UnitedStates) is en_US. Review the guidance provided here to determine the proper localeSidKey format. The languageLocaleKey formats can be found here. In addition to ensuring that the format is correct, you may need to ensure that the language is enabled for your users as described here.
- SalesforceLicenseLimitExceeded: The user could not be created in the target application because there are no available licenses for this user. Either procure additional licenses for the target application, or review your user assignments and attribute mapping configuration to ensure that the correct users are assigned with the correct attributes.
- SalesforceDuplicateUserName: The user cannot be provisioned because it has a Salesforce.com 'Username' that is duplicated in another Salesforce.com tenant. In Salesforce.com, values for the 'Username' attribute must be unique across all Salesforce.com tenants. By default, a user’s userPrincipalName in Microsoft Entra ID becomes their 'Username' in Salesforce.com. You have two options. One option is to find and rename the user with the duplicate 'Username' in the other Salesforce.com tenant, if you administer that other tenant as well. The other option is to remove access from the Microsoft Entra user to the Salesforce.com tenant with which your directory is integrated. We will retry this operation on the next synchronization attempt.
- SalesforceRequiredFieldMissing: Salesforce requires certain attributes to be present on the user to successfully create or update the user. This user is missing one of the required attributes. Ensure that attributes such as email and alias are populated on all users that you would like to be provisioned into Salesforce. You can scope users that don't have these attributes out using attribute based scoping filters.
- The default attribute mapping for provisioning to Salesforce includes the SingleAppRoleAssignments expression to map appRoleAssignments in Microsoft Entra ID to ProfileName in Salesforce. Ensure that the users do not have multiple app role assignments in Microsoft Entra ID as the attribute mapping only supports provisioning one role.
- Salesforce requires that email updates be approved manually before being changed. As a result, you may see multiple entries in the provisioning logs to update the user's email (until the email change has been approved).