Microsoft Entra recommendation: Remove unused credentials from apps (preview)
Microsoft Entra recommendations is a feature that provides you with personalized insights and actionable guidance to align your tenant with recommended best practices.
This article covers the recommendation to remove unused credentials from apps. This recommendation is called StaleAppCreds in the recommendations API in Microsoft Graph.
Prerequisites
There are different role requirements for viewing or updating a recommendation. Use the least-privileged role for the type of access needed. For a full list of roles, see Least privileged roles by task.
| Microsoft Entra role | Access type |
|---|---|
| Reports Reader | Read-only |
| Security Reader | Read-only |
| Global Reader | Read-only |
| Authentication Policy Administrator | Update and read |
| Exchange Administrator | Update and read |
| Security Administrator | Update and read |
DirectoryRecommendations.Read.All |
Read-only in Microsoft Graph |
DirectoryRecommendations.ReadWrite.All |
Update and read in Microsoft Graph |
Some recommendations might require a P2 or other license. For more information, see Recommendation availability and license requirements.
Description
Application credentials can include certificates and other types of secrets that need to be registered with that application. These credentials are used to prove the identity of the application. Only credentials actively in use by an application should remain registered with the application.
A credential is considered unused if:
- It has not been used in the past 30 days.
- It's a credential that was added to an application to be used for OAuth/OIDC flows or to the service principal for SAML flow.
The following credentials are exempted from the recommendation:
- Expired credentials do not show in the Impacted resources list.
- Credentials that were identified as unused but have expired since being flagged show as Completed in the Impacted resources list.
Value
Removing unused application credentials helps reduce the attack surface area and helps declutter the app portfolio of a tenant.
Action plan
This recommendation is available in the Microsoft Entra admin center and using the Microsoft Graph API.
Applications that the recommendation identified appear in the list of Impacted resources at the bottom of the recommendation.
Sign in to the Microsoft Entra admin center as at least a Security Administrator.
Browse to Identity > Overview.
Select the Recommendations tab and select the Remove unused credentials from applications recommendation.
Take note of the following details from the Impacted resources table.
- The Resource column displays the application name
- The ID column displays the application ID
Select More Details from the Actions column to view more details.
Note
If the origin of the credential is Service Principal, follow the guidance in the Service principals section.
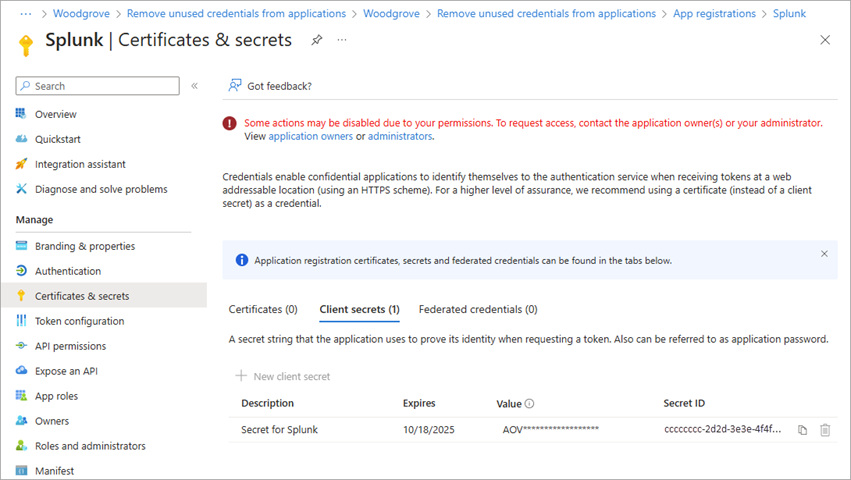
From the panel that opens, select Update Credential to navigate directly to the Certificates & secrets area of the app registration to remove the unused credential.
Locate the unused credential and remove it.
Service principals
If the origin of the credential is service principal, there are a few considerations and extra steps to follow.
Because there's often multiple service principals for a single application, it may be easier to navigate to Enterprise apps to view everything in one place.
In the Microsoft Entra admin center, browse to Identity > Applications > Enterprise applications.
Search for and open the application that was surfaced as part of this recommendation.
Select Single sign-on from the side menu.
If the credential is a service principal but there are SAML certificates in use, you can identify the details of the credential using the Microsoft Graph API. To use the Microsoft Graph API, you need the
DirectoryRecommendations.Read.AllandDirectoryRecommendations.ReadWrite.Allpermissions. For more information, see How to use Identity Recommendations.Sign in to Graph Explorer.
Select GET as the HTTP method from the dropdown.
Set the API version to beta.
Query the
keyCredentialandpasswordCredentialendpoints.Use the
removePasswordorremoveKeyendpoints to remove the credential from the service principal.