A cloud-based identity and access management service for securing user authentication and resource access

This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
I'm building a SPA that's using the oidc-client JavaScript library to authenticate to Azure AD using the OAuth 2.0 authorization code flow with PKCE to obtain an access token to use a custom (Java) API.
In order to be able to validate the access token I created a custom scope as explained under the Problem 1: Azure AD returns invalid JWT access token section at Making Azure AD OIDC Compliant and provided it to the oidc-client library so it is included when authorizing. I got authorizing and requesting initial access and refresh tokens all working as expected.
However when refreshing an access token using the /{tenant}/oauth2/v2.0/token resource I received a 400 Bad Request response containing this error message:
AADSTS90009: Application 'redacted-client-id'(redacted-client-id) is requesting a token for itself. This scenario is supported only if resource is specified using the GUID based App Identifier.
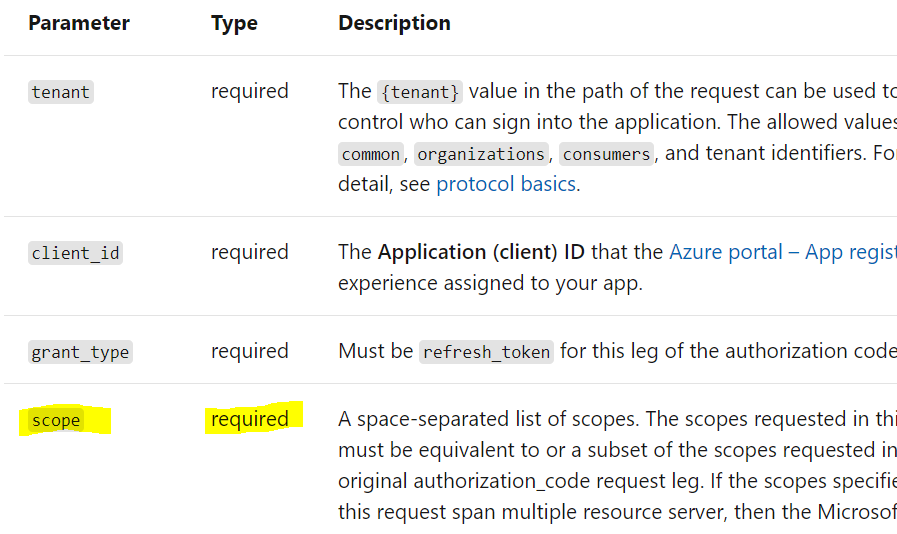
Eventually I found I could successfully refresh the access token by supplying a scope parameter with my custom scope based on it being marked as required for /{tenant}/oauth2/v2.0/token requests to refresh the access token. Is this is what would be expected to fix the problem? I've been confused because the error message talks about specifying a resource, and doesn't make any mention of a scope.
A cloud-based identity and access management service for securing user authentication and resource access

I see the documentation at https://learn.microsoft.com/en-us/azure/active-directory/develop/v2-oauth2-auth-code-flow#refresh-the-access-token has changed to now say the scope parameter is optional, yet I still get the same error from my original post if I do not supply a scope parameter. If the parameter is intended to be optional, why am I still getting the same error when I don't provide it?
Thanks @Vipul Sparsh for confirming that the scope is indeed expected in this case. Can the error message returned please be improved to mention "scope" instead of "resource" when using Microsoft Identity Platform endpoints to avoid confusion for others in the future? It looks like "resource" is only applicable when using the older Azure AD v1.0 endpoints as documented here.
As requested, here is the request made that triggered the error in question:
POST https://login.microsoftonline.com/[redacted-tenant-id]/oauth2/v2.0/token HTTP/1.1
Host: login.microsoftonline.com
Connection: keep-alive
Content-Length: 1318
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Accept: */*
Origin: [redacted]
Sec-Fetch-Site: cross-site
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: [redacted]
Accept-Encoding: gzip, deflate, br
Accept-Language: en-CA,en;q=0.9
request_type=si%3As&refresh_token=[omitted]&grant_type=refresh_token&client_id=[redacted]
@Simon Lieschke Thanks for reaching out.
Can you share the request you are sending when you got that error message.
When you use V2 endpoint , it is mandatory to send the scope parameter specify the permission you are requesting.
You can read more here
==========================================================================================================
If the suggested response helped you resolve your issue, please do not forget to accept the response as Answer and "Up-Vote" for the answer that helped you for benefit of the community.